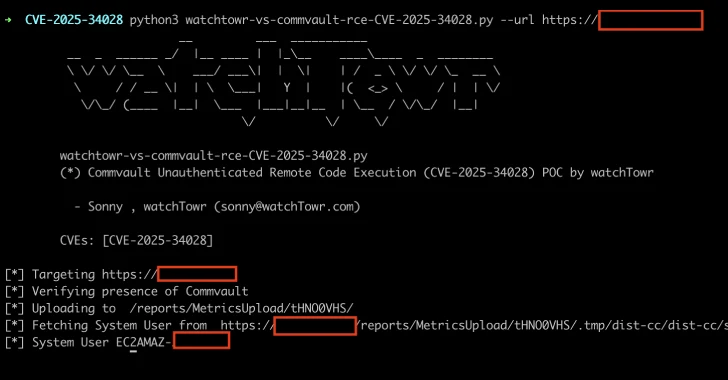
[ad_1] Apr 24, 2025Ravie LakshmananData Breach / Vulnerability A critical security flaw has been disclosed in the Commvault Command Center that could allow arbitrary code execution on affected installations. The vulnerability, tracked as CVE-2025-34028, carries a CVSS score of 9.0 out of a maximum of 10.0. “A critical security vulnerability has been identified in the…
Author: admin
159 CVEs Exploited in Q1 2025 — 28.3% Within 24 Hours of Disclosure
[ad_1] Apr 24, 2025Ravie LakshmananVulnerability / Threat Intelligence As many as 159 CVE identifiers have been flagged as exploited in the wild in the first quarter of 2025, up from 151 in Q4 2024. “We continue to see vulnerabilities being exploited at a fast pace with 28.3% of vulnerabilities being exploited within 1-day of their…
Linux io_uring PoC Rootkit Bypasses System Call-Based Threat Detection Tools
[ad_1] Apr 24, 2025Ravie LakshmananEndpoint Security / Linux Cybersecurity researchers have demonstrated a proof-of-concept (PoC) rootkit dubbed Curing that leverages a Linux asynchronous I/O mechanism called io_uring to bypass traditional system call monitoring. This causes a “major blind spot in Linux runtime security tools,” ARMO said. “This mechanism allows a user application to perform various…
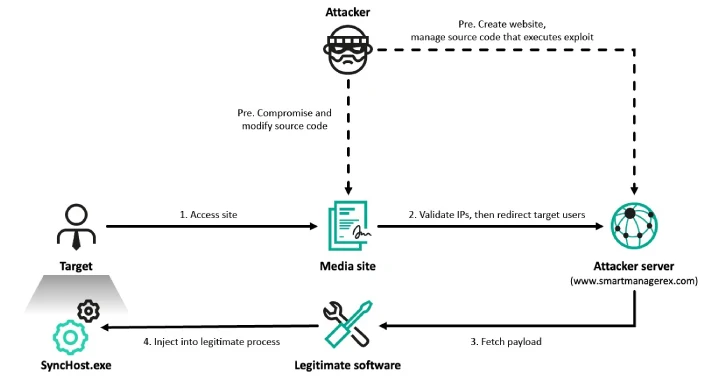
Lazarus Hits 6 South Korean Firms via Cross EX, Innorix Flaws and ThreatNeedle Malware
[ad_1] Apr 24, 2025Ravie LakshmananMalware / Threat Intelligence At least six organizations in South Korea have been targeted by the prolific North Korea-linked Lazarus Group as part of a campaign dubbed Operation SyncHole. The activity targeted South Korea’s software, IT, financial, semiconductor manufacturing, and telecommunications industries, according to a report from Kaspersky published today. The…
Darcula Adds GenAI to Phishing Toolkit, Lowering the Barrier for Cybercriminals
[ad_1] Apr 24, 2025Ravie LakshmananPhishing / Cybercrime The threat actors behind the Darcula phishing-as-a-service (PhaaS) platform have released new updates to their cybercrime suite with generative artificial intelligence (GenAI) capabilities. “This addition lowers the technical barrier for creating phishing pages, enabling less tech-savvy criminals to deploy customized scams in minutes,” Netcraft said in a new…
From Risk Scoring to Dynamic Policy Enforcement Without Network Redesign
[ad_1] The Evolving Healthcare Cybersecurity Landscape Healthcare organizations face unprecedented cybersecurity challenges in 2025. With operational technology (OT) environments increasingly targeted and the convergence of IT and medical systems creating an expanded attack surface, traditional security approaches are proving inadequate. According to recent statistics, the healthcare sector experienced a record-breaking year for data breaches in…
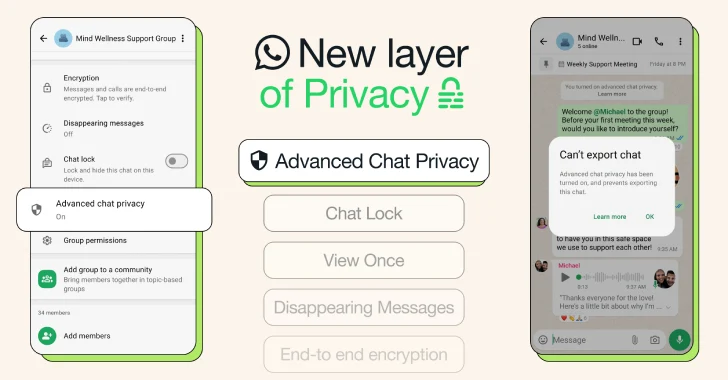
WhatsApp Adds Advanced Chat Privacy to Blocks Chat Exports and Auto-Downloads
[ad_1] Apr 24, 2025Ravie LakshmananData Protection / Artificial Intelligence WhatsApp has introduced an extra layer of privacy called Advanced Chat Privacy that allows users to block participants from sharing the contents of a conversation in traditional chats and groups. “This new setting available in both chats and groups helps prevent others from taking content outside…
DPRK Hackers Steal $137M from TRON Users in Single-Day Phishing Attack
[ad_1] Apr 23, 2025Ravie LakshmananMalware / Cryptocurrency Multiple threat activity clusters with ties to North Korea (aka Democratic People’s Republic of Korea or DPRK) have been linked to attacks targeting organizations and individuals in the Web3 and cryptocurrency space. “The focus on Web3 and cryptocurrency appears to be primarily financially motivated due to the heavy…
Russian Hackers Exploit Microsoft OAuth to Target Ukraine Allies via Signal and WhatsApp
[ad_1] Multiple suspected Russia-linked threat actors are “aggressively” targeting individuals and organizations with ties to Ukraine and human rights with an aim to gain unauthorized access to Microsoft 365 accounts since early March 2025. The highly targeted social engineering operations, per Volexity, are a shift from previously documented attacks that leveraged a technique known as…
Three Reasons Why the Browser is Best for Stopping Phishing Attacks
[ad_1] Phishing attacks remain a huge challenge for organizations in 2025. In fact, with attackers increasingly leveraging identity-based techniques over software exploits, phishing arguably poses a bigger threat than ever before. Attackers are increasingly leveraging identity-based techniques over software exploits, with phishing and stolen credentials (a byproduct of phishing) now the primary cause of breaches….