[ad_1] Mar 18, 2025Ravie LakshmananCyber Espionage / Malware Threat hunters have shed more light on a previously disclosed malware campaign undertaken by the China-aligned MirrorFace threat actor that targeted a diplomatic organization in the European Union with a backdoor known as ANEL. The attack, detected by ESET in late August 2024, singled out a Central…
Month: March 2025
How to Improve Okta Security in Four Steps
[ad_1] Mar 18, 2025The Hacker NewsAuthentication / Identity Security While Okta provides robust native security features, configuration drift, identity sprawl, and misconfigurations can provide opportunities for attackers to find their way in. This article covers four key ways to proactively secure Okta as part of your identity security efforts. Okta serves as the cornerstone of…
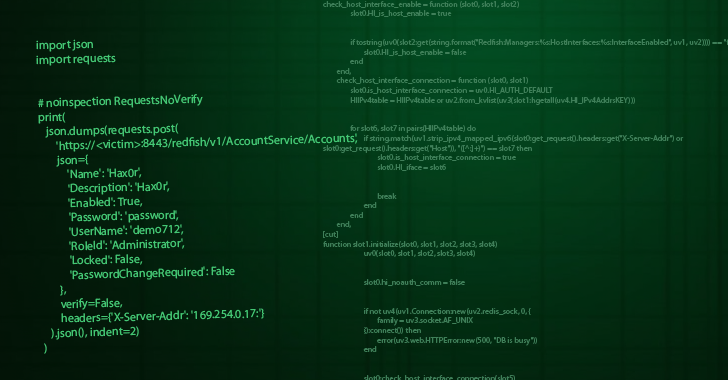
New Critical AMI BMC Vulnerability Enables Remote Server Takeover and Bricking
[ad_1] Mar 18, 2025Ravie LakshmananVulnerability / Firmware Security A critical security vulnerability has been disclosed in AMI’s MegaRAC Baseboard Management Controller (BMC) software that could allow an attacker to bypass authentication and carry out post-exploitation actions. The vulnerability, tracked as CVE-2024-54085, carries a CVSS v4 score of 10.0, indicating maximum severity. “A local or remote…
Google Acquires Wiz for $32 Billion in Its Biggest Deal Ever to Boost Cloud Security
[ad_1] Mar 18, 2025Ravie LakshmananCloud Security / Enterprise Security Google is making the biggest ever acquisition in its history by purchasing cloud security company Wiz in an all-cash deal worth $32 billion. “This acquisition represents an investment by Google Cloud to accelerate two large and growing trends in the AI era: improved cloud security and…
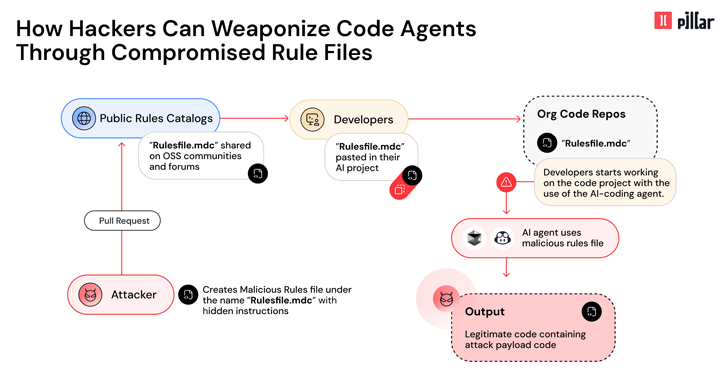
New ‘Rules File Backdoor’ Attack Lets Hackers Inject Malicious Code via AI Code Editors
[ad_1] Mar 18, 2025Ravie LakshmananAI Security / Software Security Cybersecurity researchers have disclosed details of a new supply chain attack vector dubbed Rules File Backdoor that affects artificial intelligence (AI)-powered code editors like GitHub Copilot and Cursor, causing them to inject malicious code. “This technique enables hackers to silently compromise AI-generated code by injecting hidden…
Unpatched Windows Zero-Day Flaw Exploited by 11 State-Sponsored Threat Groups Since 2017
[ad_1] Mar 18, 2025Ravie LakshmananVulnerability / Windows Security An unpatched security flaw impacting Microsoft Windows has been exploited by 11 state-sponsored groups from China, Iran, North Korea, and Russia as part of data theft, espionage, and financially motivated campaigns that date back to 2017. The zero-day vulnerability, tracked by Trend Micro’s Zero Day Initiative (ZDI)…
New Ad Fraud Campaign Exploits 331 Apps with 60M+ Downloads for Phishing and Intrusive Ads
[ad_1] Mar 18, 2025Ravie LakshmananAd Fraud / Mobile Security Cybersecurity researchers have warned about a large-scale ad fraud campaign that has leveraged hundreds of malicious apps published on the Google Play Store to serve full-screen ads and conduct phishing attacks. “The apps display out-of-context ads and even try to persuade victims to give away credentials…
A Stealthy RAT Targeting Credentials and Crypto Wallets
[ad_1] Microsoft is calling attention to a novel remote access trojan (RAT) named StilachiRAT that it said employs advanced techniques to sidestep detection and persist within target environments with an ultimate aim to steal sensitive data. The malware contains capabilities to “steal information from the target system, such as credentials stored in the browser, digital…
Apache Tomcat Vulnerability Actively Exploited Just 30 Hours After Public Disclosure
[ad_1] Mar 17, 2025Ravie LakshmananVulnerability / Web Security A recently disclosed security flaw impacting Apache Tomcat has come under active exploitation in the wild following the release of a public proof-of-concept (PoC) a mere 30 hours after public disclosure. The vulnerability, tracked as CVE-2025-24813, affects the below versions – Apache Tomcat 11.0.0-M1 to 11.0.2 Apache…
SANS Institute Warns of Novel Cloud-Native Ransomware Attacks
[ad_1] Mar 17, 2025The Hacker NewsCloud Security / Threat Intelligence The latest Palo Alto Networks Unit 42 Cloud Threat Report found that sensitive data is found in 66% of cloud storage buckets. This data is vulnerable to ransomware attacks. The SANS Institute recently reported that these attacks can be performed by abusing the cloud provider’s…