[ad_1] Feb 29, 2024NewsroomThreat Intelligence / Cyber Threat Cybersecurity researchers have disclosed a new attack technique called Silver SAML that can be successful even in cases where mitigations have been applied against Golden SAML attacks. Silver SAML “enables the exploitation of SAML to launch attacks from an identity provider like Entra ID against applications configured…
Month: February 2024
New Backdoor Targeting European Officials Linked to Indian Diplomatic Events
[ad_1] Feb 29, 2024NewsroomCyber Espionage / Malware A previously undocumented threat actor dubbed SPIKEDWINE has been observed targeting officials in European countries with Indian diplomatic missions using a new backdoor called WINELOADER. The adversary, according to a report from Zscaler ThreatLabz, used a PDF file in emails that purported to come from the Ambassador of…
FBI Warns U.S. Healthcare Sector of Targeted BlackCat Ransomware Attacks
[ad_1] The U.S. government is warning about the resurgence of BlackCat (aka ALPHV) ransomware attacks targeting the healthcare sector as recently as this month. “Since mid-December 2023, of the nearly 70 leaked victims, the healthcare sector has been the most commonly victimized,” the government said in an updated advisory. “This is likely in response to…
Iran-Linked UNC1549 Hackers Target Middle East Aerospace & Defense Sectors
[ad_1] Feb 28, 2024NewsroomCyber Espionage / Malware An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation, and defense industries in the Middle East, including Israel and the U.A.E. Other targets of the cyber espionage activity likely include Turkey, India, and Albania, Google-owned…
How to Bridge Privileged Access Management and Identity Management
[ad_1] Feb 28, 2024The Hacker NewsZero Trust / Cyber Threat Traditional perimeter-based security has become costly and ineffective. As a result, communications security between people, systems, and networks is more important than blocking access with firewalls. On top of that, most cybersecurity risks are caused by just a few superusers – typically one out of…
WordPress LiteSpeed Plugin Vulnerability Puts 5 Million Sites at Risk
[ad_1] Feb 27, 2024NewsroomVulnerability / Website Security A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that could enable unauthenticated users to escalate their privileges. Tracked as CVE-2023-40000, the vulnerability was addressed in October 2023 in version 5.7.0.1. “This plugin suffers from unauthenticated site-wide stored [cross-site scripting] vulnerability and could allow…
Five Eyes Agencies Expose APT29’s Evolving Cloud Attack Tactics
[ad_1] Feb 27, 2024NewsroomCloud Security / Threat Intelligence Cybersecurity and intelligence agencies from the Five Eyes nations have released a joint advisory detailing the evolving tactics of the Russian state-sponsored threat actor known as APT29. The hacking outfit, also known as BlueBravo, Cloaked Ursa, Cozy Bear, Midnight Blizzard (formerly Nobelium), and The Dukes, is assessed…
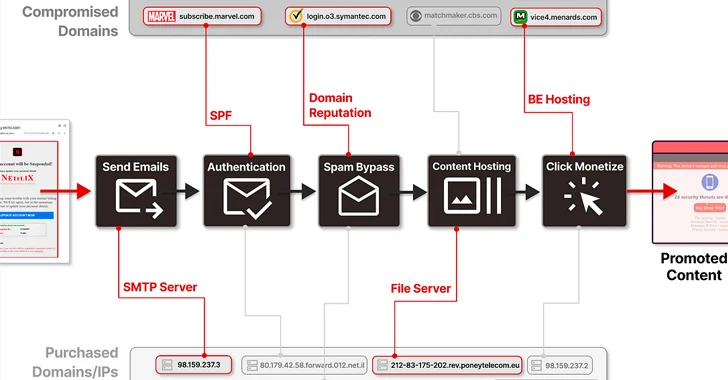
8,000+ Domains of Trusted Brands Hijacked for Massive Spam Operation
[ad_1] More than 8,000 domains and 13,000 subdomains belonging to legitimate brands and institutions have been hijacked as part of a sophisticated distribution architecture for spam proliferation and click monetization. Guardio Labs is tracking the coordinated malicious activity, which has been ongoing since at least September 2022, under the name SubdoMailing. The emails range from…
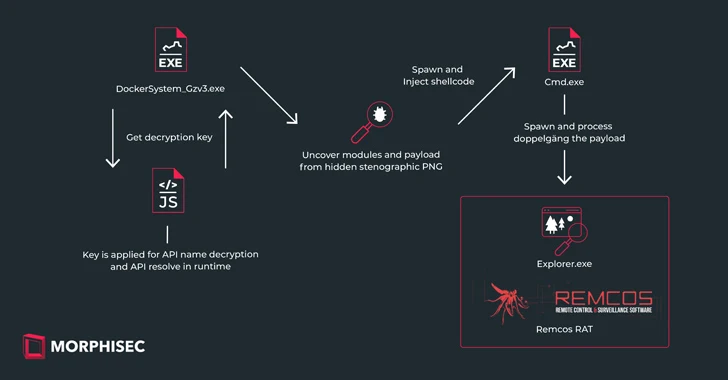
New IDAT Loader Attacks Using Steganography to Deploy Remcos RAT
[ad_1] Feb 26, 2024The Hacker NewsSteganography / Malware Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as Remcos RAT using a malware loader called IDAT Loader. The attack has been attributed to a threat actor tracked by the Computer Emergency Response Team…
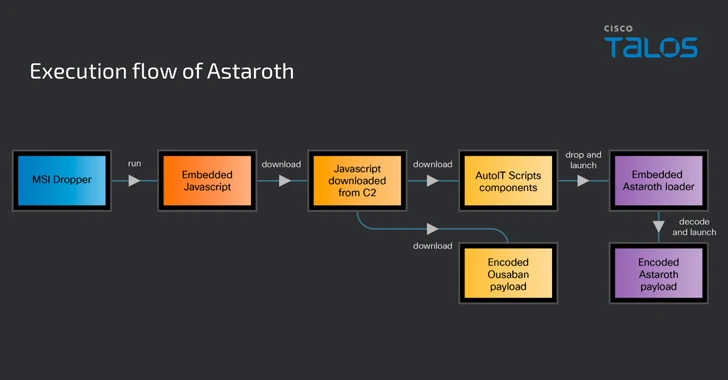
Banking Trojans Target Latin America and Europe Through Google Cloud Run
[ad_1] Cybersecurity researchers are warning about a spike in email phishing campaigns that are weaponizing the Google Cloud Run service to deliver various banking trojans such as Astaroth (aka Guildma), Mekotio, and Ousaban (aka Javali) to targets across Latin America (LATAM) and Europe. “The infection chains associated with these malware families feature the use of…