[ad_1] Apr 05, 2024NewsroomMalware / Endpoint Security Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the attack is a PDF file written in Portuguese that, when opened, shows a blurred image and asks the victim to click on a link to download…
Month: April 2024
New Phishing Campaign Targets Oil & Gas with Evolved Data-Stealing Malware
[ad_1] Apr 04, 2024NewsroomPhishing Attack / Malware An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. “The phishing emails use a unique vehicle incident lure and, in later stages of the infection chain, spoof the Federal Bureau of Transportation in a PDF that…
Vietnam-Based Hackers Steal Financial Data Across Asia with Malware
[ad_1] A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest valuable data since at least May 2023. Cisco Talos is tracking the cluster under the name CoralRaider, describing it as financially motivated. Targets of the campaign include India, China, South Korea, Bangladesh,…
Ivanti Rushes Patches for 4 New Flaws in Connect Secure and Policy Secure
[ad_1] Apr 04, 2024NewsroomNetwork Security / Vulnerability Ivanti has released security updates to address four security flaws impacting Connect Secure and Policy Secure Gateways that could result in code execution and denial-of-service (DoS). The list of flaws is as follows – CVE-2024-21894 (CVSS score: 8.2) – A heap overflow vulnerability in the IPSec component of…
U.S. Cyber Safety Board Slams Microsoft Over Breach by China-Based Hackers
[ad_1] Apr 03, 2024NewsroomData Breach / Incident Response The U.S. Cyber Safety Review Board (CSRB) has criticized Microsoft for a series of security lapses that led to the breach of nearly two dozen companies across Europe and the U.S. by a China-based nation-state group called Storm-0558 last year. The findings, released by the Department of…
Android Zero-Day Flaws in Pixel Phones Exploited by Forensic Companies
[ad_1] Apr 03, 2024NewsroomMobile Security / Zero Day Google has disclosed that two Android security flaws impacting its Pixel smartphones have been exploited in the wild by forensic companies. The high-severity zero-day vulnerabilities are as follows – CVE-2024-29745 – An information disclosure flaw in the bootloader component CVE-2024-29748 – A privilege escalation flaw in the…
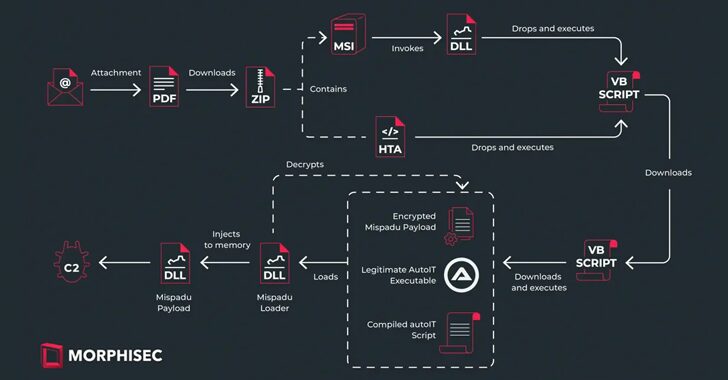
Mispadu Trojan Targets Europe, Thousands of Credentials Compromised
[ad_1] The banking trojan known as Mispadu has expanded its focus beyond Latin America (LATAM) and Spanish-speaking individuals to target users in Italy, Poland, and Sweden. Targets of the ongoing campaign include entities spanning finance, services, motor vehicle manufacturing, law firms, and commercial facilities, according to Morphisec. “Despite the geographic expansion, Mexico remains the primary…
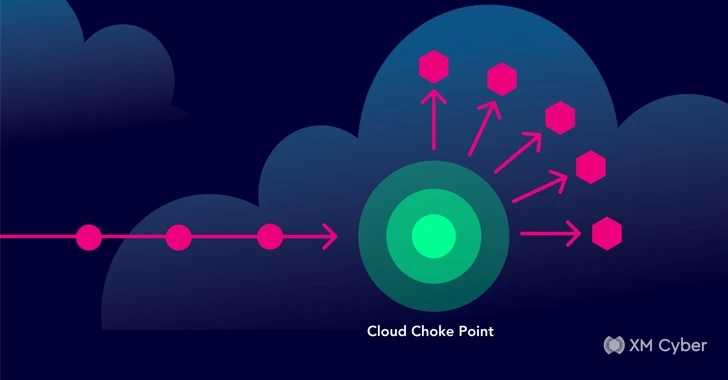
Harnessing the Power of CTEM for Cloud Security
[ad_1] Cloud solutions are more mainstream – and therefore more exposed – than ever before. In 2023 alone, a staggering 82% of data breaches were against public, private, or hybrid cloud environments. What’s more, nearly 40% of breaches spanned multiple cloud environments. The average cost of a cloud breach was above the overall average, at…
Malicious Code in XZ Utils for Linux Systems Enables Remote Code Execution
[ad_1] Apr 02, 2024NewsroomFirmware Security / Vulnerability The malicious code inserted into the open-source library XZ Utils, a widely used package present in major Linux distributions, is also capable of facilitating remote code execution, a new analysis has revealed. The audacious supply chain compromise, tracked as CVE-2024-3094 (CVSS score: 10.0), came to light last week…
Google to Delete Billions of Browsing Records in ‘Incognito Mode’ Privacy Lawsuit Settlement
[ad_1] Apr 02, 2024NewsroomBrowser Security / Data Security Google has agreed to purge billions of data records reflecting users’ browsing activities to settle a class action lawsuit that claimed the search giant tracked them without their knowledge or consent in its Chrome browser. The class action, filed in 2020, alleged the company misled users by…