[ad_1] Apr 29, 2024NewsroomProgramming / Supply Chain A security vulnerability has been discovered in the R programming language that could be exploited by a threat actor to create a malicious RDS (R Data Serialization) file such that it results in code execution when loaded and referenced. The flaw, assigned the CVE identifier CVE-2024-27322 (CVSS score:…
Month: May 2024
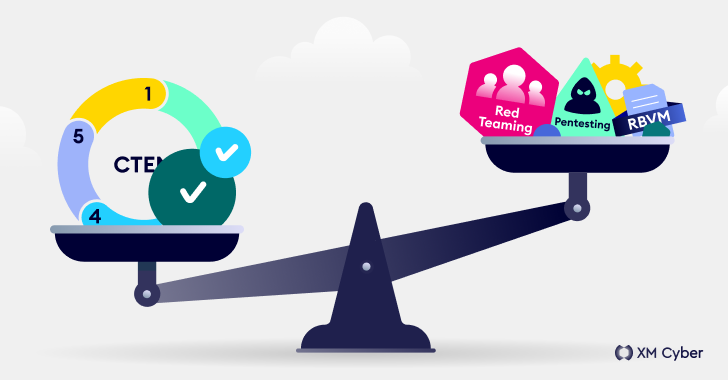
Understanding Exposure Management, Pentesting, Red Teaming and RBVM
[ad_1] It comes as no surprise that today’s cyber threats are orders of magnitude more complex than those of the past. And the ever-evolving tactics that attackers use demand the adoption of better, more holistic and consolidated ways to meet this non-stop challenge. Security teams constantly look for ways to reduce risk while improving security…
Ex-NSA Employee Sentenced to 22 Years for Trying to Sell U.S. Secrets to Russia
[ad_1] May 01, 2024NewsroomNational Security / Insider Threat A former employee of the U.S. National Security Agency (NSA) has been sentenced to nearly 22 years (262 months) in prison for attempting to transfer classified documents to Russia. “This sentence should serve as a stark warning to all those entrusted with protecting national defense information that…
ZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
[ad_1] May 01, 2024NewsroomMalware / Cyber Threat The authors behind the resurfaced ZLoader malware have added a feature that was originally present in the Zeus banking trojan that it’s based on, indicating that it’s being actively developed. “The latest version, 2.4.1.0, introduces a feature to prevent execution on machines that differ from the original infection,”…
Android Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
[ad_1] May 01, 2024NewsroomMalware / Android Cybersecurity researchers have discovered a previously undocumented malware targeting Android devices that uses compromised WordPress sites as relays for its actual command-and-control (C2) servers for detection evasion. The malware, codenamed Wpeeper, is an ELF binary that leverages the HTTPS protocol to secure its C2 communications. “Wpeeper is a typical…
New Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
[ad_1] May 02, 2024NewsroomCyber Espionage / Network Security A new malware called Cuttlefish is targeting small office and home office (SOHO) routers with the goal of stealthily monitoring all traffic through the devices and gather authentication data from HTTP GET and POST requests. “This malware is modular, designed primarily to steal authentication material found in…
Microsoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
[ad_1] Czechia and Germany on Friday revealed that they were the target of a long-term cyber espionage campaign conducted by the Russia-linked nation-state actor known as APT28, drawing condemnation from the European Union (E.U.), the North Atlantic Treaty Organization (NATO), the U.K., and the U.S. The Czech Republic’s Ministry of Foreign Affairs (MFA), in a…
CISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
[ad_1] May 02, 2024NewsroomVulnerability / Data Breach The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical flaw impacting GitLab to its Known Exploited Vulnerabilities (KEV) catalog, owing to active exploitation in the wild. Tracked as CVE-2023-7028 (CVSS score: 10.0), the maximum severity vulnerability could facilitate account takeover by sending password reset emails…
New “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
[ad_1] A never-before-seen botnet called Goldoon has been observed targeting D-Link routers with a nearly decade-old critical security flaw with the goal of using the compromised devices for further attacks. The vulnerability in question is CVE-2015-2051 (CVSS score: 9.8), which affects D-Link DIR-645 routers and allows remote attackers to execute arbitrary commands by means of…
Dropbox Discloses Breach of Digital Signature Service Affecting All Users
[ad_1] May 02, 2024NewsroomCyber Attack / Data Breach Cloud storage services provider Dropbox on Wednesday disclosed that Dropbox Sign (formerly HelloSign) was breached by unidentified threat actors, who accessed emails, usernames, and general account settings associated with all users of the digital signature product. The company, in a filing with the U.S. Securities and Exchange…