[ad_1] May 20, 2024NewsroomCyber Attack / Threat Intelligence An Iranian threat actor affiliated with the Ministry of Intelligence and Security (MOIS) has been attributed as behind destructive wiping attacks targeting Albania and Israel under the personas Homeland Justice and Karma, respectively. Cybersecurity firm Check Point is tracking the activity under the moniker Void Manticore, which…
Month: May 2024
Cyber Criminals Exploit GitHub and FileZilla to Deliver Cocktail Malware
[ad_1] May 20, 2024NewsroomMalvertising / Cryptocurrency A “multi-faceted campaign” has been observed abusing legitimate services like GitHub and FileZilla to deliver an array of stealer malware and banking trojans such as Atomic (aka AMOS), Vidar, Lumma (aka LummaC2), and Octo by impersonating credible software like 1Password, Bartender 5, and Pixelmator Pro. “The presence of multiple…
Google Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
[ad_1] May 16, 2024NewsroomBrowser Security / Vulnerability Google has rolled out fixes to address a set of nine security issues in its Chrome browser, including a new zero-day that has been exploited in the wild. Assigned the CVE identifier CVE-2024-4947, the vulnerability relates to a type confusion bug in the V8 JavaScript and WebAssembly engine….
Grandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
[ad_1] May 19, 2024NewsroomBanking Troja / Email Security The threat actors behind the Windows-based Grandoreiro banking trojan have returned in a global campaign since March 2024 following a law enforcement takedown in January. The large-scale phishing attacks, likely facilitated by other cybercriminals via a malware-as-a-service (MaaS) model, target over 1,500 banks across the world, spanning…
Chinese Nationals Arrested for Laundering $73 Million in Pig Butchering Crypto Scam
[ad_1] The U.S. Department of Justice (DoJ) has charged two arrested Chinese nationals for allegedly orchestrating a pig butchering scam that laundered at least $73 million from victims through shell companies. The individuals, Daren Li, 41, and Yicheng Zhang, 38, were arrested in Atlanta and Los Angeles on April 12 and May 16, respectively. The…
Cybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
[ad_1] May 16, 2024NewsroomRansomware / Incident Response The Microsoft Threat Intelligence team said it has observed a threat actor it tracks under the name Storm-1811 abusing the client management tool Quick Assist to target users in social engineering attacks. “Storm-1811 is a financially motivated cybercriminal group known to deploy Black Basta ransomware,” the company said…
CISA Warns of Actively Exploited D-Link Router Vulnerabilities
[ad_1] May 17, 2024NewsroomVulnerability / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting D-Link routers to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The list of vulnerabilities is as follows – CVE-2014-100005 – A cross-site request forgery (CSRF) vulnerability impacting D-Link…
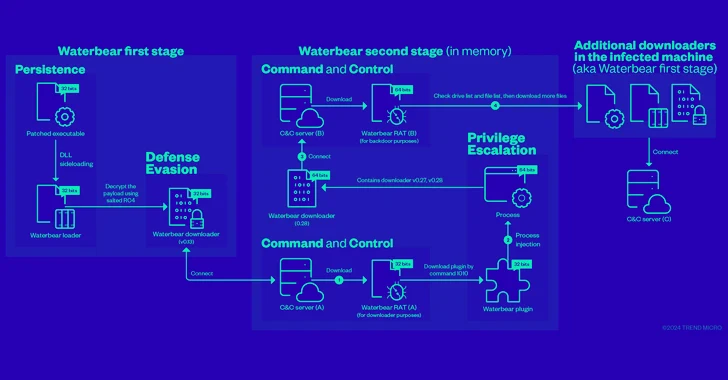
China-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
[ad_1] Cybersecurity researchers have shed more light on a remote access trojan (RAT) known as Deuterbear used by the China-linked BlackTech hacking group as part of a cyber espionage campaign targeting the Asia-Pacific region this year. “Deuterbear, while similar to Waterbear in many ways, shows advancements in capabilities such as including support for shellcode plugins,…
80% of Exposures from Misconfigurations, Less Than 1% from CVEs
[ad_1] A new report from XM Cyber has found – among other insights – a dramatic gap between where most organizations focus their security efforts, and where the most serious threats actually reside. The new report, Navigating the Paths of Risk: The State of Exposure Management in 2024, is based on hundreds of thousands of…
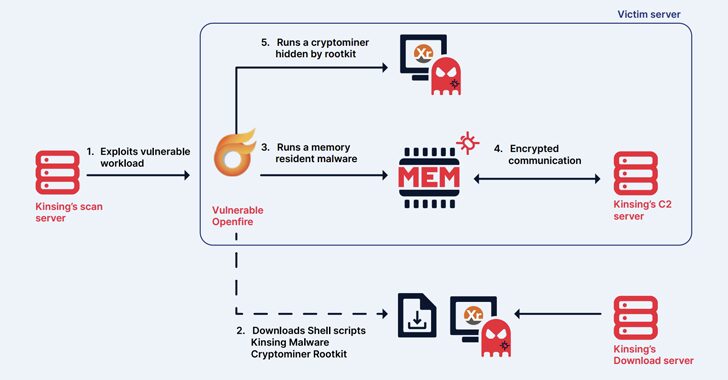
Kinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
[ad_1] May 17, 2024NewsroomCryptojacking / Malware The cryptojacking group known as Kinsing has demonstrated its ability to continuously evolve and adapt, proving to be a persistent threat by swiftly integrating newly disclosed vulnerabilities to exploit arsenal and expand its botnet. The findings come from cloud security firm Aqua, which described the threat actor as actively…