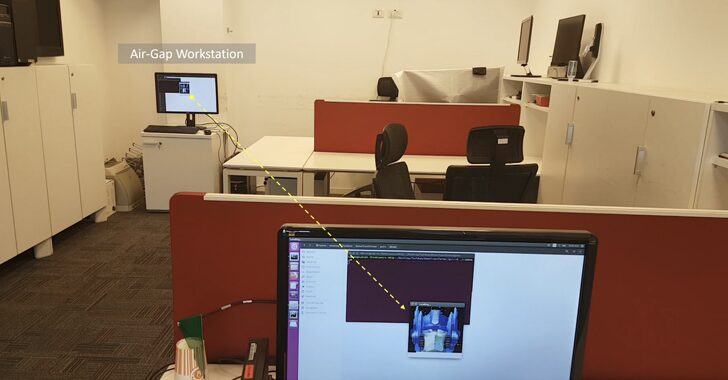
[ad_1] Sep 09, 2024Ravie LakshmananVulnerability / Hardware Security A novel side-channel attack has been found to leverage radio signals emanated by a device’s random access memory (RAM) as a data exfiltration mechanism, posing a threat to air-gapped networks. The technique has been codenamed RAMBO by Dr. Mordechai Guri, the head of the Offensive Cyber Research…
Month: September 2024
One More Tool Will Do It? Reflecting on the CrowdStrike Fallout
[ad_1] Sep 09, 2024The Hacker NewsData Protection / Threat Detection The proliferation of cybersecurity tools has created an illusion of security. Organizations often believe that by deploying a firewall, antivirus software, intrusion detection systems, identity threat detection and response, and other tools, they are adequately protected. However, this approach not only fails to address the…
TIDRONE Espionage Group Targets Taiwan Drone Makers in Cyber Campaign
[ad_1] Sep 09, 2024Ravie LakshmananCyber Attack / Threat Intelligence A previously undocumented threat actor with likely ties to Chinese-speaking groups has predominantly singled out drone manufacturers in Taiwan as part of a cyber attack campaign that commenced in 2024. Trend Micro is tracking the adversary under the moniker TIDRONE, stating the activity is espionage-driven given…
Unpatched AVTECH IP Camera Flaw Exploited by Hackers for Botnet Attacks
[ad_1] Aug 29, 2024Ravie LakshmananIoT Security / Vulnerability A years-old high-severity flaw impacting AVTECH IP cameras has been weaponized by malicious actors as a zero-day to rope them into a botnet. CVE-2024-7029 (CVSS score: 8.7), the vulnerability in question, is a “command injection vulnerability found in the brightness function of AVTECH closed-circuit television (CCTV) cameras…
How AitM Phishing Attacks Bypass MFA and EDR—and How to Fight Back
[ad_1] Attackers are increasingly using new phishing toolkits (open-source, commercial, and criminal) to execute adversary-in-the-middle (AitM) attacks. AitM enables attackers to not just harvest credentials but steal live sessions, allowing them to bypass traditional phishing prevention controls such as MFA, EDR, and email content filtering. In this article, we’re going to look at what AitM…
Russian Hackers Exploit Safari and Chrome Flaws in High-Profile Cyberattack
[ad_1] Cybersecurity researchers have flagged multiple in-the-wild exploit campaigns that leveraged now-patched flaws in Apple Safari and Google Chrome browsers to infect mobile users with information-stealing malware. “These campaigns delivered n-day exploits for which patches were available, but would still be effective against unpatched devices,” Google Threat Analysis Group (TAG) researcher Clement Lecigne said in…
Malicious npm Packages Mimicking ‘noblox.js’ Compromise Roblox Developers’ Systems
[ad_1] Sep 02, 2024Ravie LakshmananSoftware Security / Malware Roblox developers are the target of a persistent campaign that seeks to compromise systems through bogus npm packages, once again underscoring how threat actors continue to exploit the trust in the open-source ecosystem to deliver malware. “By mimicking the popular ‘noblox.js’ library, attackers have published dozens of…
Ex-Engineer Charged in Missouri for Failed $750,000 Bitcoin Extortion Attempt
[ad_1] Sep 03, 2024Ravie LakshmananInsider Threat / Network Security A 57-year-old man from the U.S. state of Missouri has been arrested in connection with a failed data extortion campaign that targeted his former employer. Daniel Rhyne of Kansas City, Missouri, has been charged with one count of extortion in relation to a threat to cause…
New Flaws in Microsoft macOS Apps Could Allow Hackers to Gain Unrestricted Access
[ad_1] Eight vulnerabilities have been uncovered in Microsoft applications for macOS that an adversary could exploit to gain elevated privileges or access sensitive data by circumventing the operating system’s permissions-based model, which revolves around the Transparency, Consent, and Control (TCC) framework. “If successful, the adversary could gain any privileges already granted to the affected Microsoft…
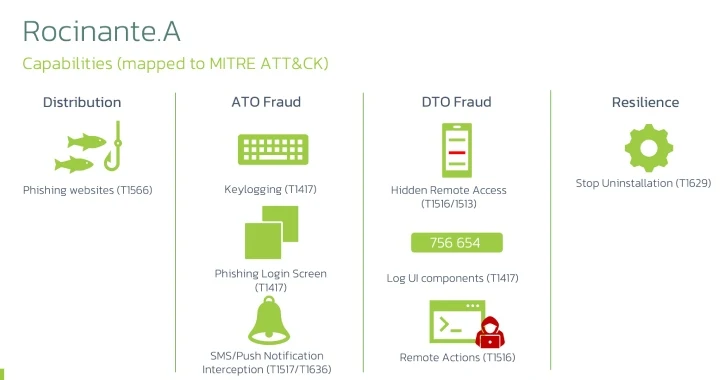
Rocinante Trojan Poses as Banking Apps to Steal Sensitive Data from Brazilian Android Users
[ad_1] Mobile users in Brazil are the target of a new malware campaign that delivers a new Android banking trojan named Rocinante. “This malware family is capable of performing keylogging using the Accessibility Service, and is also able to steal PII from its victims using phishing screens posing as different banks,” Dutch security company ThreatFabric…