[ad_1] Oct 31, 2024Ravie LakshmananCryptocurrency / Software Development LottieFiles has revealed that its npm package “lottie-player” was compromised as part of a supply chain attack, prompting it to release an updated version of the library. “On October 30th ~6:20 PM UTC – LottieFiles were notified that our popular open source npm package for the web…
Month: October 2024
New LightSpy Spyware Version Targets iPhones with Increased Surveillance Tactics
[ad_1] Oct 31, 2024Ravie LakshmananSpyware / Mobile Security Cybersecurity researchers have discovered an improved version of an Apple iOS spyware called LightSpy that not only expands on its functionality, but also incorporates destructive capabilities to prevent the compromised device from booting up. “While the iOS implant delivery method closely mirrors that of the macOS version,…
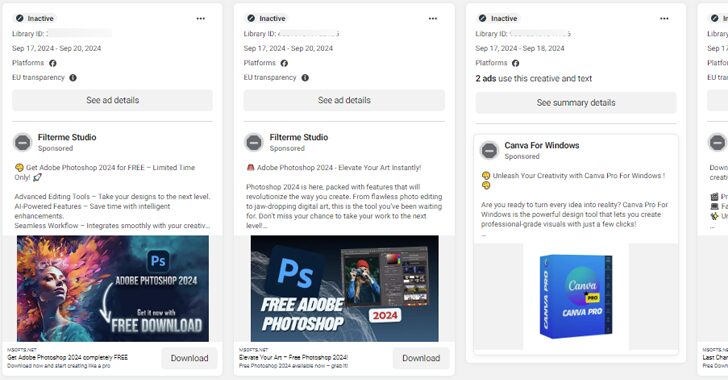
Malvertising Campaign Hijacks Facebook Accounts to Spread SYS01stealer Malware
[ad_1] Cybersecurity researchers have uncovered an ongoing malvertising campaign that abuses Meta’s advertising platform and hijacked Facebook accounts to distribute information known as SYS01stealer. “The hackers behind the campaign use trusted brands to expand their reach,” Bitdefender Labs said in a report shared with The Hacker News. “The malvertising campaign leverages nearly a hundred malicious…
North Korean Group Collaborates with Play Ransomware in Significant Cyber Attack
[ad_1] Oct 30, 2024Ravie LakshmananRansomware / Threat Intelligence Threat actors in North Korea have been implicated in a recent incident that deployed a known ransomware family called Play, underscoring their financial motivations. The activity, observed between May and September 2024, has been attributed to a threat actor tracked as Jumpy Pisces, which is also known…
Opera Browser Fixes Big Security Hole That Could Have Exposed Your Information
[ad_1] Oct 30, 2024Ravie Lakshmanan Browser Security / Vulnerability A now-patched security flaw in the Opera web browser could have enabled a malicious extension to gain unauthorized, full access to private APIs. The attack, codenamed CrossBarking, could have made it possible to conduct actions such as capturing screenshots, modifying browser settings, and account hijacking, Guardio…
Dutch Police Disrupt Major Info Stealers RedLine and MetaStealer in Operation Magnus
[ad_1] Oct 29, 2024Ravie LakshmananCybercrime / Malware The Dutch National Police, along with international partners, have announced the disruption of the infrastructure powering two information stealers tracked as RedLine and MetaStealer. The takedown, which took place on October 28, 2024, is the result of an international law enforcement task force codenamed Operation Magnus that involved…
Researchers Uncover Vulnerabilities in Open-Source AI and ML Models
[ad_1] Oct 29, 2024Ravie LakshmananAI Security / Vulnerability A little over three dozen security vulnerabilities have been disclosed in various open-source artificial intelligence (AI) and machine learning (ML) models, some of which could lead to remote code execution and information theft. The flaws, identified in tools like ChuanhuChatGPT, Lunary, and LocalAI, have been reported as…
Eliminate the Impossible with Exposure Validation
[ad_1] Sherlock Holmes is famous for his incredible ability to sort through mounds of information; he removes the irrelevant and exposes the hidden truth. His philosophy is plain yet brilliant: “When you have eliminated the impossible, whatever remains, however improbable, must be the truth.” Rather than following every lead, Holmes focuses on the details that…
U.S. Government Issues New TLP Guidance for Cross-Sector Threat Intelligence Sharing
[ad_1] Oct 29, 2024Ravie LakshmananDigital Security / Data Privacy The U.S. government (USG) has issued new guidance governing the use of the Traffic Light Protocol (TLP) to handle the threat intelligence information shared between the private sector, individual researchers, and Federal Departments and Agencies. “The USG follows TLP markings on cybersecurity information voluntarily shared by…
New Research Reveals Spectre Vulnerability Persists in Latest AMD and Intel Processors
[ad_1] Oct 29, 2024Ravie LakshmananHardware Security / Vulnerability More than six years after the Spectre security flaw impacting modern CPU processors came to light, new research has found that the latest AMD and Intel processors are still susceptible to speculative execution attacks. The attack, disclosed by ETH Zürich researchers Johannes Wikner and Kaveh Razavi, aims…