[ad_1] Oct 28, 2024Ravie LakshmananMalware / Threat Intelligence Three malicious packages published to the npm registry in September 2024 have been found to contain a known malware called BeaverTail, a JavaScript downloader and information stealer linked to an ongoing North Korean campaign tracked as Contagious Interview. The Datadog Security Research team is monitoring the activity…
Month: October 2024
Chinese Hackers Use CloudScout Toolset to Steal Session Cookies from Cloud Services
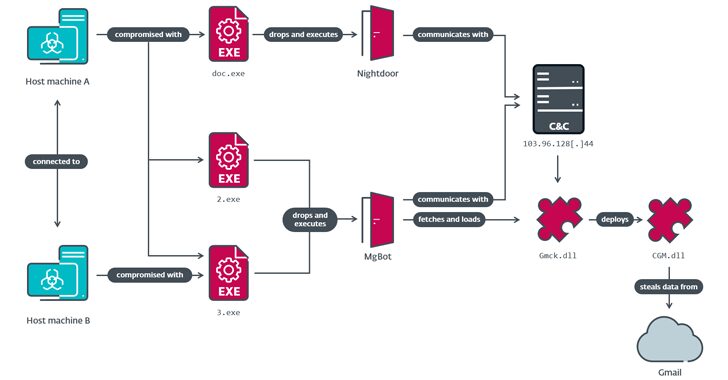
[ad_1] Oct 28, 2024Ravie LakshmananCloud Security / Cyber Attack A government entity and a religious organization in Taiwan were the target of a China-linked threat actor known as Evasive Panda that infected them with a previously undocumented post-compromise toolset codenamed CloudScout. “The CloudScout toolset is capable of retrieving data from various cloud services by leveraging…
Russian Espionage Group Targets Ukrainian Military with Malware via Telegram
[ad_1] Oct 28, 2024Ravie LakshmananCyber Espionage / Android A suspected Russian hybrid espionage and influence operation has been observed delivering a mix of Windows and Android malware to target the Ukrainian military under the Telegram persona Civil Defense. Google’s Threat Analysis Group (TAG) and Mandiant are tracking the activity under the name UNC5812. The threat…
Sailing the Seven Seas Securely from Port to Port – OT Access Security for Ships and Cranes
[ad_1] Oct 28, 2024The Hacker NewsOperational Technology / Cybersecurity Operational Technology (OT) security has affected marine vessel and port operators, since both ships and industrial cranes are being digitalized and automated at a rapid pace, ushering in new types of security challenges. Ships come to shore every six months on average. Container cranes are mostly…
THN Cybersecurity Recap: Top Threats, Tools and News (Oct 21
[ad_1] Oct 28, 2024Ravie LakshmananCyber Security / Hacking News Cybersecurity news can sometimes feel like a never-ending horror movie, can’t it? Just when you think the villains are locked up, a new threat emerges from the shadows. This week is no exception, with tales of exploited flaws, international espionage, and AI shenanigans that could make…
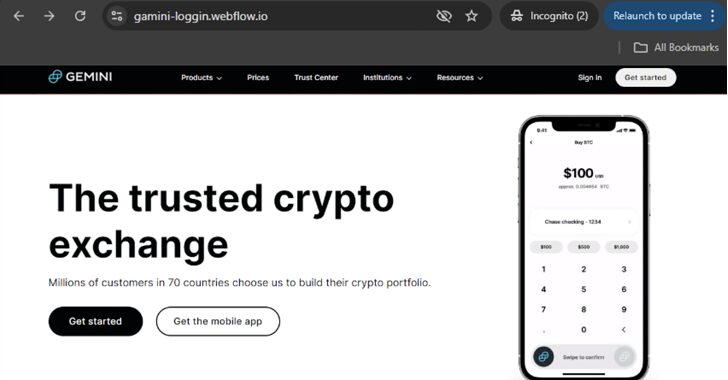
Cybercriminals Use Webflow to Deceive Users into Sharing Sensitive Login Credentials
[ad_1] Cybersecurity researchers have warned of a spike in phishing pages created using a website builder tool called Webflow, as threat actors continue to abuse legitimate services like Cloudflare and Microsoft Sway to their advantage. “The campaigns target sensitive information from different crypto wallets, including Coinbase, MetaMask, Phantom, Trezor, and Bitbuy, as well as login…
Researchers Uncover OS Downgrade Vulnerability Targeting Microsoft Windows Kernel
[ad_1] Oct 28, 2024Ravie LakshmananVulnerability / Windows Security A new attack technique could be used to bypass Microsoft’s Driver Signature Enforcement (DSE) on fully patched Windows systems, leading to operating system (OS) downgrade attacks. “This bypass allows loading unsigned kernel drivers, enabling attackers to deploy custom rootkits that can neutralize security controls, hide processes and…
5 Techniques for Collecting Cyber Threat Intelligence
[ad_1] To defend your organization against cyber threats, you need a clear picture of the current threat landscape. This means constantly expanding your knowledge about new and ongoing threats. There are many techniques analysts can use to collect crucial cyber threat intelligence. Let’s consider five that can greatly improve your threat investigations. Pivoting on С2…
North Korean ScarCruft Exploits Windows Zero-Day to Spread RokRAT Malware
[ad_1] Oct 16, 2024Ravie LakshmananZero-Day / Windows Security The North Korean threat actor known as ScarCruft has been linked to the zero-day exploitation of a now-patched security flaw in Windows to infect devices with malware known as RokRAT. The vulnerability in question is CVE-2024-38178 (CVSS score: 7.5), a memory corruption bug in the Scripting Engine…
From Misuse to Abuse: AI Risks and Attacks
[ad_1] Oct 16, 2024The Hacker NewsArtificial Intelligence / Cybercrime AI from the attacker’s perspective: See how cybercriminals are leveraging AI and exploiting its vulnerabilities to compromise systems, users, and even other AI applications Cybercriminals and AI: The Reality vs. Hype “AI will not replace humans in the near future. But humans who know how to…