[ad_1] The North Korean threat actor known as Lazarus Group has been attributed to the zero-day exploitation of a now-patched security flaw in Google Chrome to seize control of infected devices. Cybersecurity vendor Kaspersky said it discovered a novel attack chain in May 2024 that targeted the personal computer of an unnamed Russian national with…
Month: October 2024
Cisco Issues Urgent Fix for ASA and FTD Software Vulnerability Under Active Attack
[ad_1] Oct 24, 2024Ravie LakshmananVulnerability / Network Security Cisco on Wednesday said it has released updates to address an actively exploited security flaw in its Adaptive Security Appliance (ASA) that could lead to a denial-of-service (DoS) condition. The vulnerability, tracked as CVE-2024-20481 (CVSS score: 5.8), affects the Remote Access VPN (RAVPN) service of Cisco ASA…
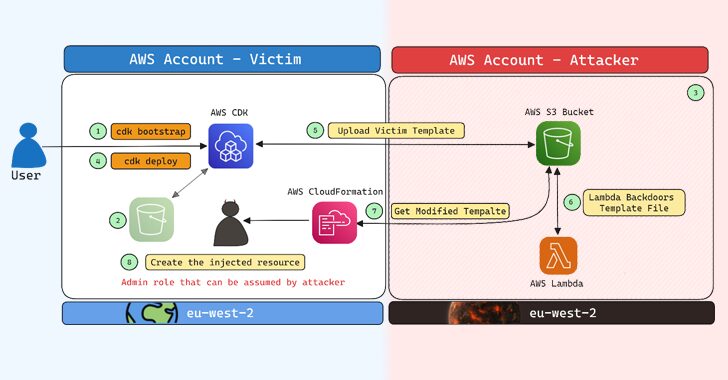
AWS Cloud Development Kit Vulnerability Exposes Users to Potential Account Takeover Risks
[ad_1] Cybersecurity researchers have disclosed a security flaw impacting Amazon Web Services (AWS) Cloud Development Kit (CDK) that could have resulted in an account takeover under specific circumstances. “The impact of this issue could, in certain scenarios, allow an attacker to gain administrative access to a target AWS account, resulting in a full account takeover,”…
New Qilin.B Ransomware Variant Emerges with Improved Encryption and Evasion Tactics
[ad_1] Oct 24, 2024Ravie LakshmananRansomware / Cybercrime Cybersecurity researchers have discovered an advanced version of the Qilin ransomware sporting increased sophistication and tactics to evade detection. The new variant is being tracked by cybersecurity firm Halcyon under the moniker Qilin.B. “Notably, Qilin.B now supports AES-256-CTR encryption for systems with AESNI capabilities, while still retaining Chacha20…
The Hidden Risks of Legacy MFA
[ad_1] Sometimes, it turns out that the answers we struggled so hard to find were sitting right in front of us for so long that we somehow overlooked them. When the Department of Homeland Security, through the Cybersecurity and Infrastructure Security Agency (CISA), in coordination with the FBI, issues a cybersecurity warning and prescribes specific…
A Shake-up in Identity Security Is Looming Large
[ad_1] Oct 23, 2024The Hacker NewsIdentity Security / Data Protection Identity security is front, and center given all the recent breaches that include Microsoft, Okta, Cloudflare and Snowflake to name a few. Organizations are starting to realize that a shake-up is needed in terms of the way we approach identity security both from a strategic…
New Grandoreiro Banking Malware Variants Emerge with Advanced Tactics to Evade Detection
[ad_1] New variants of a banking malware called Grandoreiro have been found to adopt new tactics in an effort to bypass anti-fraud measures, indicating that the malicious software is continuing to be actively developed despite law enforcement efforts to crack down on the operation. “Only part of this gang was arrested: the remaining operators behind…
Researchers Reveal ‘Deceptive Delight’ Method to Jailbreak AI Models
[ad_1] Oct 23, 2024Ravie LakshmananArtificial Intelligence / Vulnerability Cybersecurity researchers have shed light on a new adversarial technique that could be used to jailbreak large language models (LLMs) during the course of an interactive conversation by sneaking in an undesirable instruction between benign ones. The approach has been codenamed Deceptive Delight by Palo Alto Networks…
Security Flaw in Styra’s OPA Exposes NTLM Hashes to Remote Attackers
[ad_1] Oct 22, 2024Ravie LakshmananVulnerability / Software Security Details have emerged about a now-patched security flaw in Styra’s Open Policy Agent (OPA) that, if successfully exploited, could have led to leakage of New Technology LAN Manager (NTLM) hashes. “The vulnerability could have allowed an attacker to leak the NTLM credentials of the OPA server’s local…
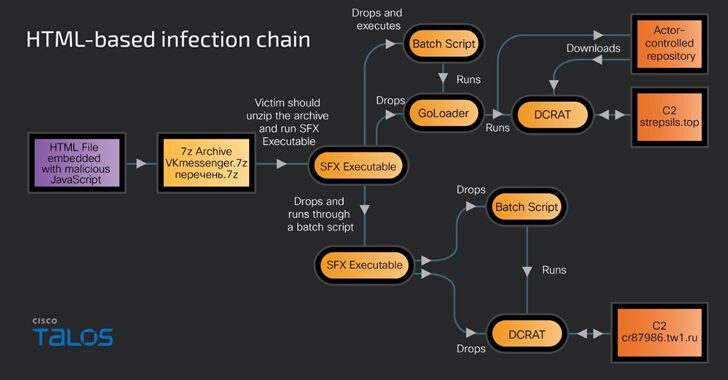
Gophish Framework Used in Phishing Campaigns to Deploy Remote Access Trojans
[ad_1] Russian-speaking users have become the target of a new phishing campaign that leverages an open-source phishing toolkit called Gophish to deliver DarkCrystal RAT (aka DCRat) and a previously undocumented remote access trojan dubbed PowerRAT. “The campaign involves modular infection chains that are either Maldoc or HTML-based infections and require the victim’s intervention to trigger…