[ad_1] Nov 27, 2024Ravie LakshmananLinux / Malware Cybersecurity researchers have shed light on what has been described as the first Unified Extensible Firmware Interface (UEFI) bootkit designed for Linux systems. Dubbed Bootkitty by its creators who go by the name BlackCat, the bootkit is assessed to be a proof-of-concept (PoC) and there is no evidence…
Month: November 2024
Matrix Botnet Exploits IoT Devices in Widespread DDoS Botnet Campaign
[ad_1] Nov 27, 2024Ravie LakshmananIoT Security / Network Security A threat actor named Matrix has been linked to a widespread distributed denial-of-service (DoD) campaign that leverages vulnerabilities and misconfigurations in Internet of Things (IoT) devices to co-opt them into a disruptive botnet. “This operation serves as a comprehensive one-stop shop for scanning, exploiting vulnerabilities, deploying…
A Free Vulnerability Intelligence Platform For Staying Ahead of the Latest Threats
[ad_1] Nov 26, 2024The Hacker NewsPentest / Vulnerability Assessment When CVEs go viral, separating critical vulnerabilities from the noise is essential to protecting your organization. That’s why Intruder, a leader in attack surface management, built Intel – a free vulnerability intelligence platform designed to help you act fast and prioritize real threats. What is Intel?…
Critical WordPress Anti-Spam Plugin Flaws Expose 200,000+ Sites to Remote Attacks
[ad_1] Nov 26, 2024Ravie LakshmananVulnerability / Website Security Two critical security flaws impacting the Spam protection, Anti-Spam, and FireWall plugin WordPress could allow an unauthenticated attacker to install and enable malicious plugins on susceptible sites and potentially achieve remote code execution. The vulnerabilities, tracked as CVE-2024-10542 and CVE-2024-10781, carry a CVSS score of 9.8 out…
CISA Urges Agencies to Patch Critical “Array Networks” Flaw Amid Active Attacks
[ad_1] Nov 26, 2024Ravie LakshmananVulnerability / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a now-patched critical security flaw impacting Array Networks AG and vxAG secure access gateways to its Known Exploited Vulnerabilities (KEV) catalog following reports of active exploitation in the wild. The vulnerability, tracked as CVE-2023-28461 (CVSS score:…
Flying Under the Radar – Security Evasion Techniques
[ad_1] Dive into the evolution of phishing and malware evasion techniques and understand how attackers are using increasingly sophisticated methods to bypass security measures. The Evolution of Phishing Attacks “I really like the saying that ‘This is out of scope’ said no hacker ever. Whether it’s tricks, techniques or technologies, hackers will do anything to…
ChatGPT, Claude Impersonators Deliver JarkaStealer via Python Libraries
[ad_1] Nov 22, 2024Ravie LakshmananArtificial Intelligence / Malware Cybersecurity researchers have discovered two malicious packages uploaded to the Python Package Index (PyPI) repository that impersonated popular artificial intelligence (AI) models like OpenAI ChatGPT and Anthropic Claude to deliver an information stealer called JarkaStealer. The packages, named gptplus and claudeai-eng, were uploaded by a user named…
Microsoft, Meta, and DOJ Disrupt Global Cybercrime and Fraudulent Networks
[ad_1] Meta Platforms, Microsoft, and the U.S. Department of Justice (DoJ) have announced independent actions to tackle cybercrime and disrupt services that enable scams, fraud, and phishing attacks. To that end, Microsoft’s Digital Crimes Unit (DCU) said it seized 240 fraudulent websites associated with an Egypt-based cybercrime facilitator named Abanoub Nady (aka MRxC0DER and mrxc0derii),…
Are You Doing Enough to Protect Your Data?
[ad_1] Google Workspace has quickly become the productivity backbone for businesses worldwide, offering an all-in-one suite with email, cloud storage and collaboration tools. This single-platform approach makes it easy for teams to connect and work efficiently, no matter where they are, enabling seamless digital transformation that’s both scalable and adaptable. As companies shift from traditional,…
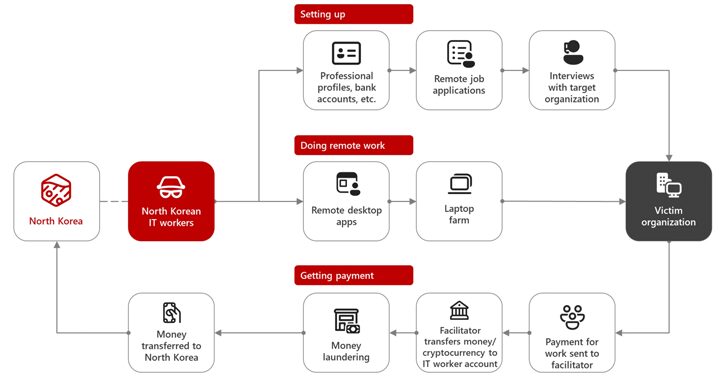
North Korean Hackers Steal $10M with AI-Driven Scams and Malware on LinkedIn
[ad_1] Nov 23, 2024Ravie LakshmananArtificial Intelligence / Cryptocurrency The North Korea-linked threat actor known as Sapphire Sleet is estimated to have stolen more than $10 million worth of cryptocurrency as part of social engineering campaigns orchestrated over a six-month period. These findings come from Microsoft, which said that multiple threat activity clusters with ties to…