[ad_1] Cybersecurity researchers have discovered a new phishing campaign that spreads a new fileless variant of known commercial malware called Remcos RAT. Remcos RAT “provides purchases with a wide range of advanced features to remotely control computers belonging to the buyer,” Fortinet FortiGuard Labs researcher Xiaopeng Zhang said in an analysis published last week. “However,…
Month: November 2024
HPE Issues Critical Security Patches for Aruba Access Point Vulnerabilities
[ad_1] Nov 11, 2024Ravie LakshmananVulnerability / Risk Mitigation Hewlett Packard Enterprise (HPE) has released security updates to address multiple vulnerabilities impacting Aruba Networking Access Point products, including two critical bugs that could result in unauthenticated command execution. The flaws affect Access Points running Instant AOS-8 and AOS-10 – AOS-10.4.x.x: 10.4.1.4 and below Instant AOS-8.12.x.x: 8.12.0.2…
How Cybersecurity Leaders Prove It
[ad_1] Cyber threats are intensifying, and cybersecurity has become critical to business operations. As security budgets grow, CEOs and boardrooms are demanding concrete evidence that cybersecurity initiatives deliver value beyond regulation compliance. Just like you wouldn’t buy a car without knowing it was first put through a crash test, security systems must also be validated…
PAN-OS Firewall Vulnerability Under Active Exploitation – IoCs Released
[ad_1] Nov 16, 2024Ravie LakshmananVulnerability / Network Security Palo Alto Networks has released new indicators of compromise (IoCs) a day after the network security vendor confirmed that a new zero-day vulnerability impacting its PAN-OS firewall management interface has been actively exploited in the wild. To that end, the company said it observed malicious activity originating…
5 Ways Behavioral Analytics is Revolutionizing Incident Response
[ad_1] Behavioral analytics, long associated with threat detection (i.e. UEBA or UBA), is experiencing a renaissance. Once primarily used to identify suspicious activity, it’s now being reimagined as a powerful post-detection technology that enhances incident response processes. By leveraging behavioral insights during alert triage and investigation, SOCs can transform their workflows to become more accurate,…
DEEPDATA Malware Exploiting Unpatched Fortinet Flaw to Steal VPN Credentials
[ad_1] A threat actor known as BrazenBamboo has exploited an unresolved security flaw in Fortinet’s FortiClient for Windows to extract VPN credentials as part of a modular framework called DEEPDATA. Volexity, which disclosed the findings Friday, said it identified the zero-day exploitation of the credential disclosure vulnerability in July 2024, describing BrazenBamboo as the developer…
North Korean Hackers Target macOS Using Flutter-Embedded Malware
[ad_1] Nov 12, 2024Ravie LakshmananMalware / Application Security Threat actors with ties to the Democratic People’s Republic of Korea (DPRK aka North Korea) have been found embedding malware within Flutter applications, marking the first time this tactic has been adopted by the adversary to infect Apple macOS devices. Jamf Threat Labs, which made the discovery…
Iranian Hackers Use “Dream Job” Lures to Deploy SnailResin Malware in Aerospace Attacks
[ad_1] Nov 13, 2024Ravie LakshmananCyber Espionage / Malware The Iranian threat actor known as TA455 has been observed taking a leaf out of a North Korean hacking group’s playbook to orchestrate its own version of the Dream Job campaign targeting the aerospace industry by offering fake jobs since at least September 2023. “The campaign distributed…
Microsoft Fixes 90 New Flaws, Including Actively Exploited NTLM and Task Scheduler Bugs
[ad_1] Nov 13, 2024Ravie LakshmananVulnerability / Patch Tuesday Microsoft on Tuesday revealed that two security flaws impacting Windows NT LAN Manager (NTLM) and Task Scheduler have come under active exploitation in the wild. The security vulnerabilities are among the 90 security bugs the tech giant addressed as part of its Patch Tuesday update for November…
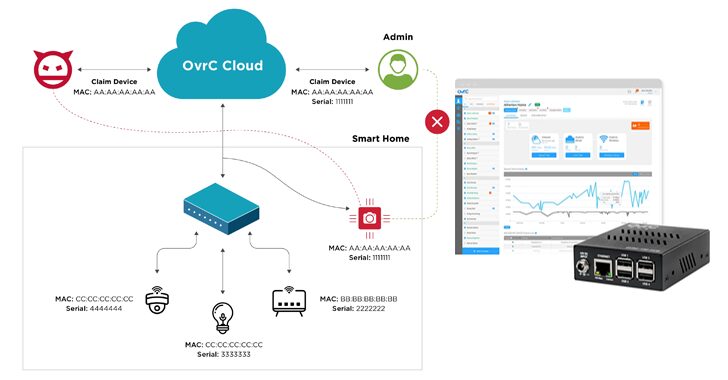
OvrC Platform Vulnerabilities Expose IoT Devices to Remote Attacks and Code Execution
[ad_1] Nov 13, 2024Ravie LakshmananCloud Security / Vulnerability A security analysis of the OvrC cloud platform has uncovered 10 vulnerabilities that could be chained to allow potential attackers to execute code remotely on connected devices. “Attackers successfully exploiting these vulnerabilities can access, control, and disrupt devices supported by OvrC; some of those include smart electrical…