[ad_1] Nov 14, 2024The Hacker NewsData Privacy / Compliance Advertising on TikTok is the obvious choice for any company trying to reach a young market, and especially so if it happens to be a travel company, with 44% of American Gen Zs saying they use the platform to plan their vacations. But one online travel…
Month: November 2024
Google Warns of Rising Cloaking Scams, AI-Driven Fraud, and Crypto Schemes
[ad_1] Nov 14, 2024Ravie LakshmananArtificial Intelligence / Cryptocurrency Google has revealed that bad actors are leveraging techniques like landing page cloaking to conduct scams by impersonating legitimate sites. “Cloaking is specifically designed to prevent moderation systems and teams from reviewing policy-violating content which enables them to deploy the scam directly to users,” Laurie Richardson, VP…
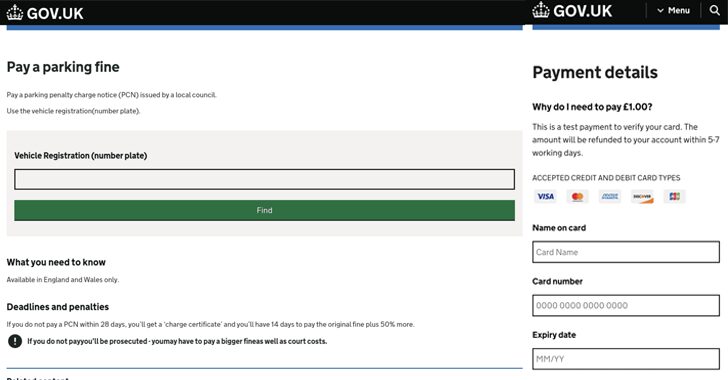
Experts Uncover 70,000 Hijacked Domains in Widespread ‘Sitting Ducks’ Attack Scheme
[ad_1] Multiple threat actors have been found taking advantage of an attack technique called Sitting Ducks to hijack legitimate domains for using them in phishing attacks and investment fraud schemes for years. The findings come from Infoblox, which said it identified nearly 800,000 vulnerable registered domains over the past three months, of which approximately 9%…
5 BCDR Oversights That Leave You Exposed to Ransomware
[ad_1] Ransomware isn’t just a buzzword; it’s one of the most dreaded challenges businesses face in this increasingly digitized world. Ransomware attacks are not only increasing in frequency but also in sophistication, with new ransomware groups constantly emerging. Their attack methods are evolving rapidly, becoming more dangerous and damaging than ever. Almost all respondents (99.8%)…
Free Decryptor Released for BitLocker-Based ShrinkLocker Ransomware Victims
[ad_1] Romanian cybersecurity company Bitdefender has released a free decryptor to help victims recover data encrypted using the ShrinkLocker ransomware. The decryptor is the result of a comprehensive analysis of ShrinkLocker’s inner workings, allowing the researchers to discover a “specific window of opportunity for data recovery immediately after the removal of protectors from BitLocker-encrypted disks.”…
Hamas-Affiliated WIRTE Employs SameCoin Wiper in Disruptive Attacks Against Israel
[ad_1] Nov 13, 2024Ravie LakshmananThreat Intelligence / Cyber Espionage A threat actor affiliated with Hamas has expanded its malicious cyber operations beyond espionage to carry out disruptive attacks that exclusively target Israeli entities. The activity, linked to a group called WIRTE, has also targeted the Palestinian Authority, Jordan, Iraq, Saudi Arabia, and Egypt, Check Point…
Comprehensive Guide to Building a Strong Browser Security Program
[ad_1] Nov 13, 2024The Hacker NewsBrowser Security / SaaS Security The rise of SaaS and cloud-based work environments has fundamentally altered the cyber risk landscape. With more than 90% of organizational network traffic flowing through browsers and web applications, companies are facing new and serious cybersecurity threats. These include phishing attacks, data leakage, and malicious…
New Phishing Tool GoIssue Targets GitHub Developers in Bulk Email Campaigns
[ad_1] Nov 12, 2024Ravie LakshmananEmail Security / Threat Intelligence Cybersecurity researchers are calling attention to a new sophisticated tool called GoIssue that can be used to send phishing messages at scale targeting GitHub users. The program, first marketed by a threat actor named cyberdluffy (aka Cyber D’ Luffy) on the Runion forum earlier this August,…
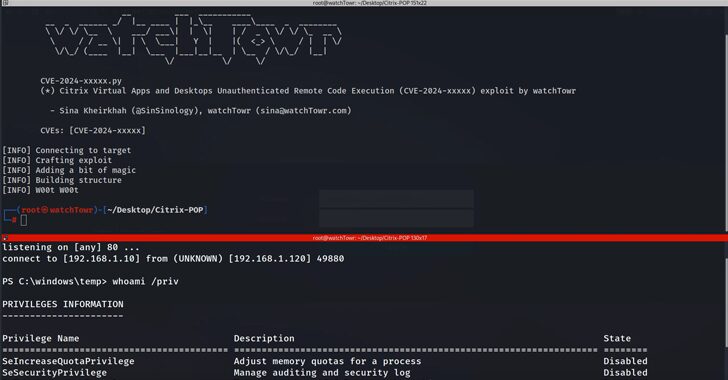
New Flaws in Citrix Virtual Apps Enable RCE Attacks via MSMQ Misconfiguration
[ad_1] Nov 12, 2024Ravie LakshmananVirtualization / Vulnerability Cybersecurity researchers have disclosed new security flaws impacting Citrix Virtual Apps and Desktop that could be exploited to achieve unauthenticated remote code execution (RCE) The issue, per findings from watchTowr, is rooted in the Session Recording component that allows system administrators to capture user activity, and record keyboard…
New Ymir Ransomware Exploits Memory for Stealthy Attacks; Targets Corporate Networks
[ad_1] Cybersecurity researchers have flagged a new ransomware family called Ymir that was deployed in an attack two days after systems were compromised by a stealer malware called RustyStealer. “Ymir ransomware introduces a unique combination of technical features and tactics that enhance its effectiveness,” Russian cybersecurity vendor Kaspersky said. “Threat actors leveraged an unconventional blend…