[ad_1] Dec 03, 2024Ravie LakshmananVulnerability / Network Security Cisco on Monday updated an advisory to warn customers of active exploitation of a decade-old security flaw impacting its Adaptive Security Appliance (ASA). The vulnerability, tracked as CVE-2014-2120 (CVSS score: 4.3), concerns a case of insufficient input validation in ASA’s WebVPN login page that could allow an…
Month: December 2024
Horns&Hooves Campaign Delivers RATs via Fake Emails and JavaScript Payloads
[ad_1] Dec 03, 2024Ravie LakshmananMalware / Phishing Attack A newly discovered malware campaign has been found to target private users, retailers, and service businesses mainly located in Russia to deliver NetSupport RAT and BurnsRAT. The campaign, dubbed Horns&Hooves by Kaspersky, has hit more than 1,000 victims since it began around March 2023. The end goal…
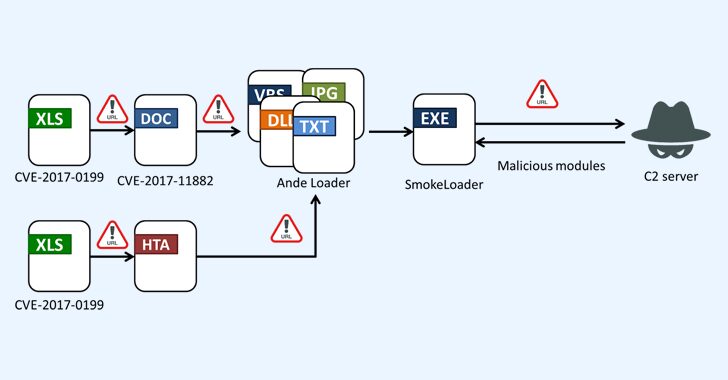
SmokeLoader Malware Resurfaces, Targeting Manufacturing and IT in Taiwan
[ad_1] Dec 02, 2024Ravie LakshmananMalware / Cryptocurrency Taiwanese entities in manufacturing, healthcare, and information technology sectors have become the target of a new campaign distributing the SmokeLoader malware. “SmokeLoader is well-known for its versatility and advanced evasion techniques, and its modular design allows it to perform a wide range of attacks,” Fortinet FortiGuard Labs said…
A Guide to Securing AI App Development: Join This Cybersecurity Webinar
[ad_1] Dec 02, 2024The Hacker NewsAI Security / Data Protection Artificial Intelligence (AI) is no longer a far-off dream—it’s here, changing the way we live. From ordering coffee to diagnosing diseases, it’s everywhere. But while you’re creating the next big AI-powered app, hackers are already figuring out ways to break it. Every AI app is…
APT-C-60 Hackers Exploit StatCounter and Bitbucket in SpyGlace Malware Campaign
[ad_1] Nov 27, 2024Ravie LakshmananMalware / Cyber Espionage The threat actor known as APT-C-60 has been linked to a cyber attack targeting an unnamed organization in Japan that used a job application-themed lure to deliver the SpyGlace backdoor. That’s according to findings from JPCERT/CC, which said the intrusion leveraged legitimate services like Google Drive, Bitbucket,…
Latest Multi-Stage Attack Scenarios with Real-World Examples
[ad_1] Multi-stage cyber attacks, characterized by their complex execution chains, are designed to avoid detection and trick victims into a false sense of security. Knowing how they operate is the first step to building a solid defense strategy against them. Let’s examine real-world examples of some of the most common multi-stage attack scenarios that are…
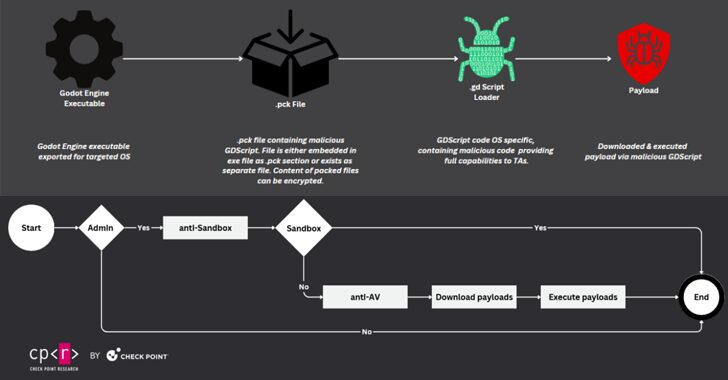
Cybercriminals Exploit Popular Game Engine Godot to Distribute Cross-Platform Malware
[ad_1] A popular open-source game engine called Godot Engine is being misused as part of a new GodLoader malware campaign, infecting over 17,000 systems since at least June 2024. “Cybercriminals have been taking advantage of Godot Engine to execute crafted GDScript code which triggers malicious commands and delivers malware,” Check Point said in a new…
XML-RPC npm Library Turns Malicious, Steals Data, Deploys Crypto Miner
[ad_1] Nov 28, 2024Ravie LakshmananSoftware Security / Data Breach Cybersecurity researchers have discovered a software supply chain attack that has remained active for over a year on the npm package registry by starting off as an innocuous library and later adding malicious code to steal sensitive data and mine cryptocurrency on infected systems. The package,…