[ad_1] Feb 08, 2025Ravie LakshmananArtificial Intelligence / Supply Chain Security Cybersecurity researchers have uncovered two malicious machine learning (ML) models on Hugging Face that leveraged an unusual technique of “broken” pickle files to evade detection. “The pickle files extracted from the mentioned PyTorch archives revealed the malicious Python content at the beginning of the file,”…
Month: February 2025
India’s RBI Introduces Exclusive “bank.in” Domain to Combat Digital Banking Fraud
[ad_1] Feb 07, 2025Ravie LakshmananFinancial Security / Regulatory Compliance India’s central bank, the Reserve Bank of India (RBI), said it’s introducing an exclusive “bank.in” internet domain for banks in the country to combat digital financial fraud. “This initiative aims to reduce cyber security threats and malicious activities like phishing; and, streamline secure financial services, thereby…
DeepSeek App Transmits Sensitive User and Device Data Without Encryption
[ad_1] Feb 07, 2025Ravie LakshmananMobile Security / Artificial Intelligence A new audit of DeepSeek’s mobile app for the Apple iOS operating system has found glaring security issues, the foremost being that it sends sensitive data over the internet sans any encryption, exposing it to interception and manipulation attacks. The assessment comes from NowSecure, which also…
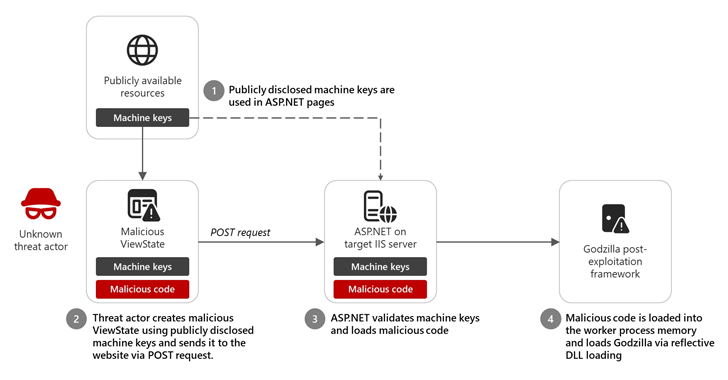
Microsoft Identifies 3,000 Leaked ASP.NET Keys Enabling Code Injection Attacks
[ad_1] Feb 07, 2025Ravie LakshmananCloud Security / Web Security Microsoft is warning of an insecure practice wherein software developers are incorporating publicly disclosed ASP.NET machine keys from publicly accessible resources, thereby putting their applications in attackers’ pathway. The tech giant’s threat intelligence team said it observed limited activity in December 2024 that involved an unknown…
CISA Warns of Active Exploits Targeting Trimble Cityworks Vulnerability
[ad_1] Feb 07, 2025The Hacker NewsVulnerability / Malware The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned that a security flaw impacting Trimble Cityworks GIS-centric asset management software has come under active exploitation in the wild. The vulnerability in question is CVE-2025-0994 (CVSS v4 score: 8.6), a deserialization of untrusted data bug that could…
AI-Powered Social Engineering: Reinvented Threats
[ad_1] The foundations for social engineering attacks – manipulating humans – might not have changed much over the years. It’s the vectors – how these techniques are deployed – that are evolving. And like most industries these days, AI is accelerating its evolution. This article explores how these changes are impacting business, and how cybersecurity…
Hackers Exploiting SimpleHelp RMM Flaws for Persistent Access and Ransomware
[ad_1] Feb 07, 2025Ravie LakshmananVulnerability / Threat Intelligence Threat actors have been observed exploiting recently disclosed security flaws in SimpleHelp’s Remote Monitoring and Management (RMM) software as a precursor for what appears to be a ransomware attack. The intrusion leveraged the now-patched vulnerabilities to gain initial access and maintain persistent remote access to an unspecified…
North Korean APT Kimsuky Uses forceCopy Malware to Steal Browser-Stored Credentials
[ad_1] Feb 06, 2025Ravie LakshmananThreat Intelligence / Malware The North Korea-linked nation-state hacking group known as Kimsuky has been observed conducting spear-phishing attacks to deliver an information stealer malware named forceCopy, according to new findings from the AhnLab Security Intelligence Center (ASEC). The attacks commence with phishing emails containing a Windows shortcut (LNK) file that’s…
The Evolving Role of PAM in Cybersecurity Leadership Agendas for 2025
[ad_1] Privileged Access Management (PAM) has emerged as a cornerstone of modern cybersecurity strategies, shifting from a technical necessity to a critical pillar in leadership agendas. With the PAM market projected to reach $42.96 billion by 2037 (according to Research Nester), organizations invest heavily in PAM solutions. Why is PAM climbing the ranks of leadership…
Ransomware Extortion Drops to $813.5M in 2024, Down from $1.25B in 2023
[ad_1] Feb 06, 2025Ravie LakshmananCybercrime / Ransomware Ransomware attacks netted cybercrime groups a total of $813.5 million in 2024, a decline from $1.25 billion in 2023. The total amount extorted during the first half of 2024 stood at $459.8 million, blockchain intelligence firm Chainalysis said, adding payment activity slumped after July 2024 by about 3.94%….