[ad_1] Feb 20, 2024NewsroomRansomware / Data Protection The U.K. National Crime Agency (NCA) on Tuesday confirmed that it obtained LockBit’s source code as well as a wealth of intelligence pertaining to its activities and their affiliates as part of a dedicated task force called Operation Cronos. “Some of the data on LockBit’s systems belonged to…
Blog
New Migo Malware Targeting Redis Servers for Cryptocurrency Mining
[ad_1] Feb 20, 2024NewsroomServer Security / Cryptojacking A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised Linux hosts. “This particular campaign involves the use of a number of novel system weakening techniques against the data store itself,” Cado security researcher Matt Muir…
VMware Alert: Uninstall EAP Now
[ad_1] Feb 21, 2024NewsroomActive Directory / Vulnerability VMware is urging users to uninstall the deprecated Enhanced Authentication Plugin (EAP) following the discovery of a critical security flaw. Tracked as CVE-2024-22245 (CVSS score: 9.6), the vulnerability has been described as an arbitrary authentication relay bug. “A malicious actor could trick a target domain user with EAP…
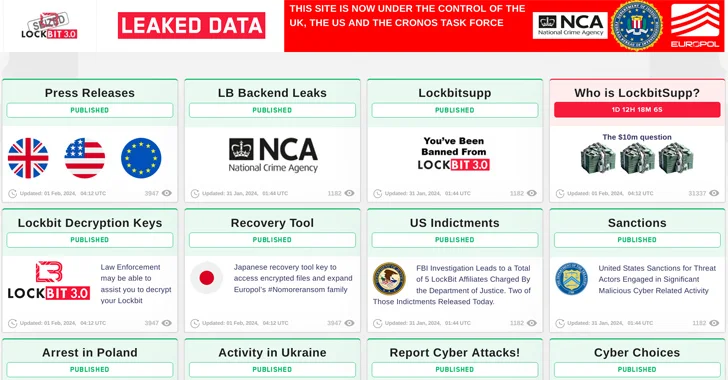
U.S. Offers $15 Million Bounty to Hunt Down LockBit Ransomware Leaders
[ad_1] The U.S. State Department has announced monetary rewards of up to $15 million for information that could lead to the identification of key leaders within the LockBit ransomware group and the arrest of any individual participating in the operation. “Since January 2020, LockBit actors have executed over 2,000 attacks against victims in the United…
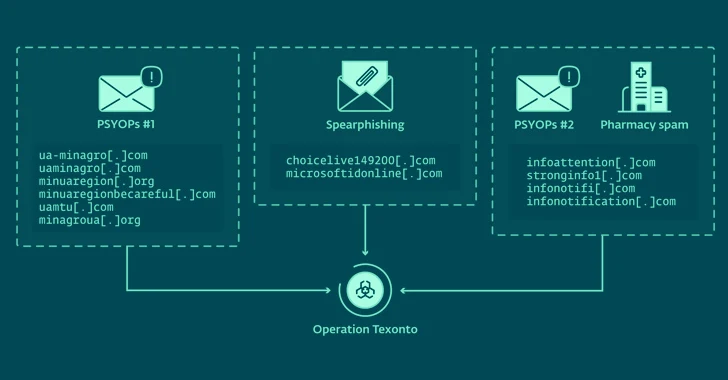
Russian Hackers Target Ukraine with Disinformation and Credential-Harvesting Attacks
[ad_1] Feb 21, 2024NewsroomPhishing Attack / Information Warfare Cybersecurity researchers have unearthed a new influence operation targeting Ukraine that leverages spam emails to propagate war-related disinformation. The activity has been linked to Russia-aligned threat actors by Slovak cybersecurity company ESET, which also identified a spear-phishing campaign aimed at a Ukrainian defense company in October 2023…
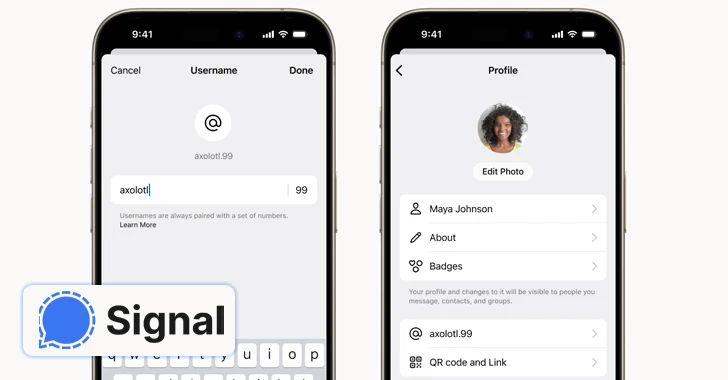
Signal Introduces Usernames, Allowing Users to Keep Their Phone Numbers Private
[ad_1] Feb 21, 2024NewsroomSecure Communication / Anonymity End-to-end encrypted (E2EE) messaging app Signal said it’s piloting a new feature that allows users to create unique usernames (not to be confused with profile names) and keep the phone numbers away from prying eyes. “If you use Signal, your phone number will no longer be visible to…
Cybersecurity for Healthcare—Diagnosing the Threat Landscape and Prescribing Solutions for Recovery
[ad_1] On Thanksgiving Day 2023, while many Americans were celebrating, hospitals across the U.S. were doing quite the opposite. Systems were failing. Ambulances were diverted. Care was impaired. Hospitals in three states were hit by a ransomware attack, and in that moment, the real-world repercussions came to light—it wasn’t just computer networks that were brought…
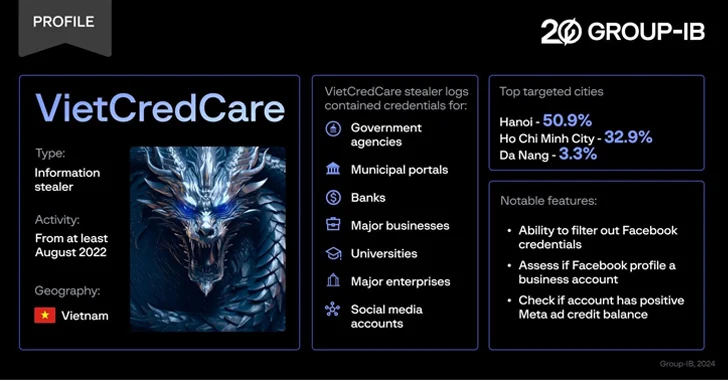
New ‘VietCredCare’ Stealer Targeting Facebook Advertisers in Vietnam
[ad_1] Feb 21, 2024NewsroomMalware / Cyber Threat Facebook advertisers in Vietnam are the target of a previously unknown information stealer dubbed VietCredCare at least since August 2022. The malware is “notable for its ability to automatically filter out Facebook session cookies and credentials stolen from compromised devices, and assess whether these accounts manage business profiles…
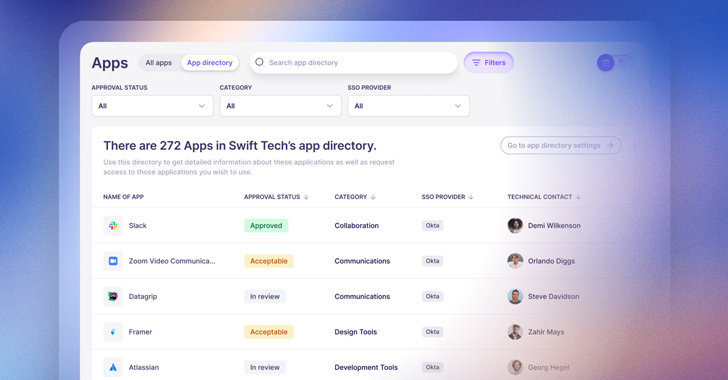
6 Ways to Simplify SaaS Identity Governance
[ad_1] With SaaS applications now making up the vast majority of technology used by employees in most organizations, tasks related to identity governance need to happen across a myriad of individual SaaS apps. This presents a huge challenge for centralized IT teams who are ultimately held responsible for managing and securing app access, but can’t…
New Wi-Fi Vulnerabilities Expose Android and Linux Devices to Hackers
[ad_1] Feb 21, 2024NewsroomNetwork Security / Vulnerability Cybersecurity researchers have identified two authentication bypass flaws in open-source Wi-Fi software found in Android, Linux, and ChromeOS devices that could trick users into joining a malicious clone of a legitimate network or allow an attacker to join a trusted network without a password. The vulnerabilities, tracked as…