[ad_1] Nov 02, 2023The Hacker NewsSaaS Security / Software This new product offers SaaS discovery and risk assessment coupled with a free user access review in a unique “freemium” model Securing employees’ SaaS usage is becoming increasingly crucial for most cloud-based organizations. While numerous tools are available to address this need, they often employ different…
Blog
Iranian Cyber Espionage Group Targets Financial and Government Sectors in Middle East
[ad_1] A threat actor affiliated with Iran’s Ministry of Intelligence and Security (MOIS) has been observed waging a sophisticated cyber espionage campaign targeting financial, government, military, and telecommunications sectors in the Middle East for at least a year. Israeli cybersecurity firm Check Point, which discovered the campaign alongside Sygnia, is tracking the actor under the…
Researchers Expose Prolific Puma’s Underground Link Shortening Service
[ad_1] A threat actor known as Prolific Puma has been maintaining a low profile and operating an underground link shortening service that’s offered to other threat actors for at least over the past four years. Prolific Puma creates “domain names with an RDGA [registered domain generation algorithm] and use these domains to provide a link…
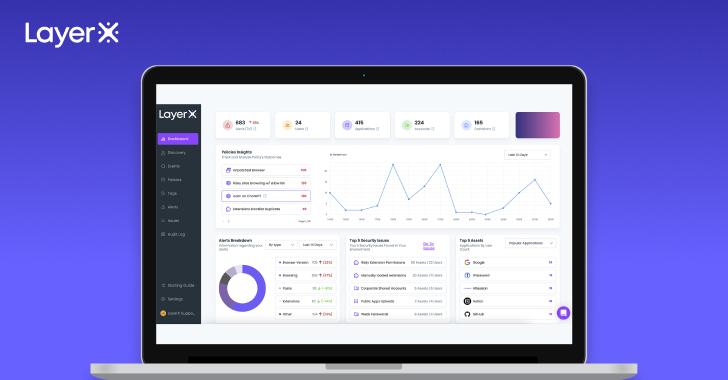
LayerX’s Enterprise Browser Security Extension
[ad_1] The browser has become the main work interface in modern enterprises. It’s where employees create and interact with data, and how they access organizational and external SaaS and web apps. As a result, the browser is extensively targeted by adversaries. They seek to steal the data it stores and use it for malicious access…
PentestPad: Platform for Pentest Teams
[ad_1] In the ever-evolving cybersecurity landscape, the game-changers are those who adapt and innovate swiftly. Pen test solutions not only supercharge productivity but also provide a crucial layer of objectivity, ensuring efficiency and exceptional accuracy. The synergy between a skilled penetration tester and the precision of pen testing solutions are crucial for staying on top…
Arid Viper Targeting Arabic Android Users with Spyware Disguised as Dating App
[ad_1] Oct 31, 2023NewsroomCyber War / Malware The threat actor known as Arid Viper (aka APT-C-23, Desert Falcon, or TAG-63) has been attributed as behind an Android spyware campaign targeting Arabic-speaking users with a counterfeit dating app designed to harvest data from infected handsets. “Arid Viper’s Android malware has a number of features that enable…
Malicious NuGet Packages Caught Distributing SeroXen RAT Malware
[ad_1] Oct 31, 2023NewsroomSoftware Security / Malware Cybersecurity researchers have uncovered a new set of malicious packages published to the NuGet package manager using a lesser-known method for malware deployment. Software supply chain security firm ReversingLabs described the campaign as coordinated and ongoing since August 1, 2023, while linking it to a host of rogue…
A Wake-Up Call for Companies
[ad_1] Oct 30, 2023The Hacker NewsSaaS Security / Data Security Earlier this week, ServiceNow announced on its support site that misconfigurations within the platform could result in “unintended access” to sensitive data. For organizations that use ServiceNow, this security exposure is a critical concern that could have resulted in major data leakage of sensitive corporate…
Pro-Hamas Hacktivists Targeting Israeli Entities with Wiper Malware
[ad_1] Oct 30, 2023NewsroomCyber War / Malware A pro-Hamas hacktivist group has been observed using a new Linux-based wiper malware dubbed BiBi-Linux Wiper, targeting Israeli entities amidst the ongoing Israeli-Hamas war. “This malware is an x64 ELF executable, lacking obfuscation or protective measures,” Security Joes said in a new report published today. “It allows attackers…
5 Must-Know Trends Impacting AppSec
[ad_1] Oct 30, 2023The Hacker NewsWebinar / Web App Security Modern web app development relies on cloud infrastructure and containerization. These technologies scale on demand, handling millions of daily file transfers – it’s almost impossible to imagine a world without them. However, they also introduce multiple attack vectors that exploit file uploads when working with…