[ad_1] Oct 21, 2023NewsroomZero-Day / Vulnerability Cisco has warned of a new zero-day flaw in IOS XE that has been actively exploited by an unknown threat actor to deploy a malicious Lua-based implant on susceptible devices. Tracked as CVE-2023-20273 (CVSS score: 7.2), the issue relates to a privilege escalation flaw in the web UI feature…
Blog
U.S. DoJ Cracks Down on North Korean IT Scammers Defrauding Global Businesses
[ad_1] Oct 20, 2023NewsroomOnline Seucrity / Cyber Threat The U.S. government has announced the seizure of 17 website domains used by North Korean information technology (IT) workers as part of an illicit scheme to defraud businesses across the world, evade sanctions, and fund the country’s ballistic missile program. The Department of Justice (DoJ) said the…
A New Low-Cost Cybercrime Weapon Emerges
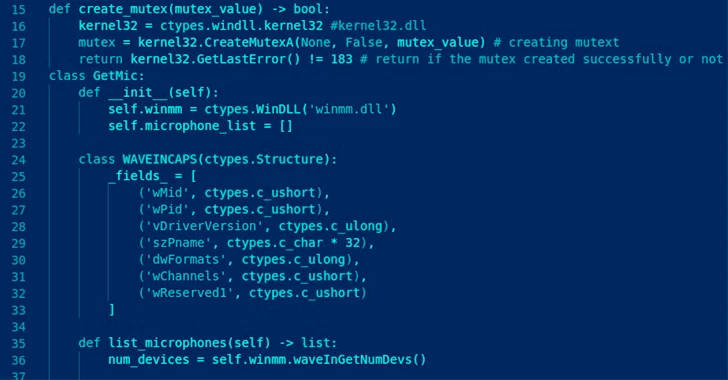
[ad_1] Oct 20, 2023NewsroomCyber Threat / Malware A new information stealer named ExelaStealer has become the latest entrant to an already crowded landscape filled with various off-the-shelf malware designed to capture sensitive data from compromised Windows systems. “ExelaStealer is a largely open-source infostealer with paid customizations available from the threat actor,” Fortinet FortiGuard Labs researcher…
Unleashing the Power of the Internet of Things and Cyber Security
[ad_1] Due to the rapid evolution of technology, the Internet of Things (IoT) is changing the way business is conducted around the world. This advancement and the power of the IoT have been nothing short of transformational in making data-driven decisions, accelerating efficiencies, and streamlining operations to meet the demands of a competitive global marketplace….
Vietnamese Hackers Target U.K., U.S., and India with DarkGate Malware
[ad_1] Oct 20, 2023NewsroomMalware / Cyber Attack Attacks leveraging the DarkGate commodity malware targeting entities in the U.K., the U.S., and India have been linked to Vietnamese actors associated with the use of the infamous Ducktail stealer. “The overlap of tools and campaigns is very likely due to the effects of a cybercrime marketplace,” WithSecure…
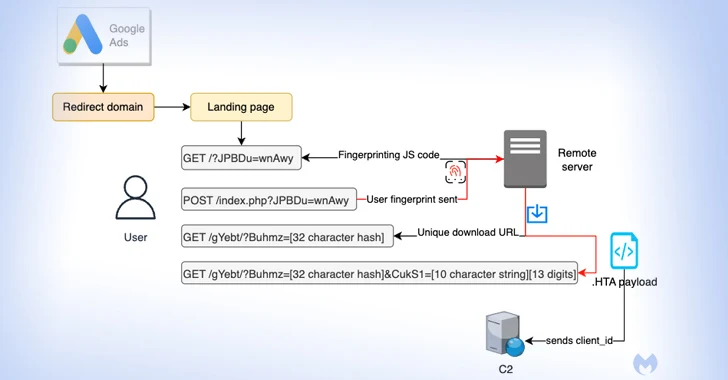
Malvertisers Using Google Ads to Target Users Searching for Popular Software
[ad_1] Oct 20, 2023NewsroomMalvertising / Cyber Threat Details have emerged about a malvertising campaign that leverages Google Ads to direct users searching for popular software to fictitious landing pages and distribute next-stage payloads. Malwarebytes, which discovered the activity, said it’s “unique in its way to fingerprint users and distribute time sensitive payloads.” The attack singles…
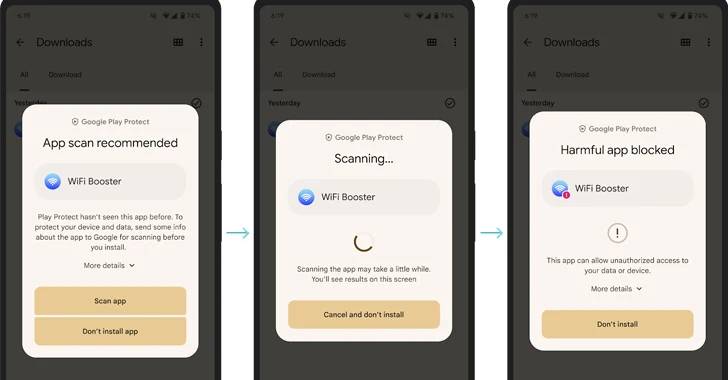
Google Play Protect Introduces Real-Time Code-Level Scanning for Android Malware
[ad_1] Oct 19, 2023NewsroomMobile Security / Technology Google has announced an update to its Play Protect with support for real-time scanning at the code level to tackle novel malicious apps prior to downloading and installing them on Android devices. “Google Play Protect will now recommend a real-time app scan when installing apps that have never…
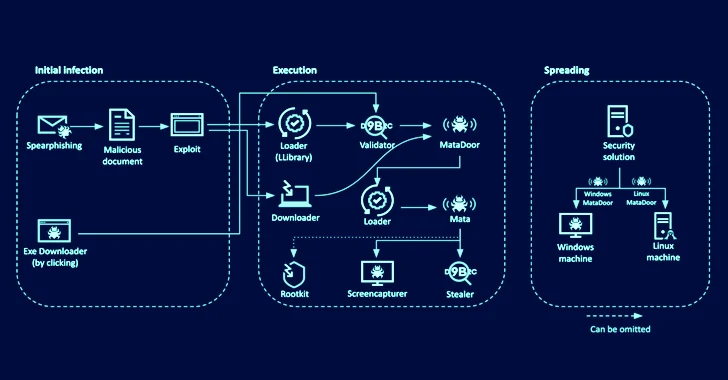
Sophisticated MATA Framework Strikes Eastern European Oil and Gas Companies
[ad_1] An updated version of a sophisticated backdoor framework called MATA has been used in attacks aimed at over a dozen Eastern European companies in the oil and gas sector and defense industry as part of a cyber espionage operation that took place between August 2022 and May 2023. “The actors behind the attack used…
How Often Should I Scan?
[ad_1] The time between a vulnerability being discovered and hackers exploiting it is narrower than ever – just 12 days. So it makes sense that organizations are starting to recognize the importance of not leaving long gaps between their scans, and the term “continuous vulnerability scanning” is becoming more popular. Hackers won’t wait for your…
Iran-Linked OilRig Targets Middle East Governments in 8-Month Cyber Campaign
[ad_1] Oct 19, 2023NewsroomCyber Attack / Cyber Espionage The Iran-linked OilRig threat actor targeted an unnamed Middle East government between February and September 2023 as part of an eight-month-long campaign. The attack led to the theft of files and passwords and, in one instance, resulted in the deployment of a PowerShell backdoor called PowerExchange, the…