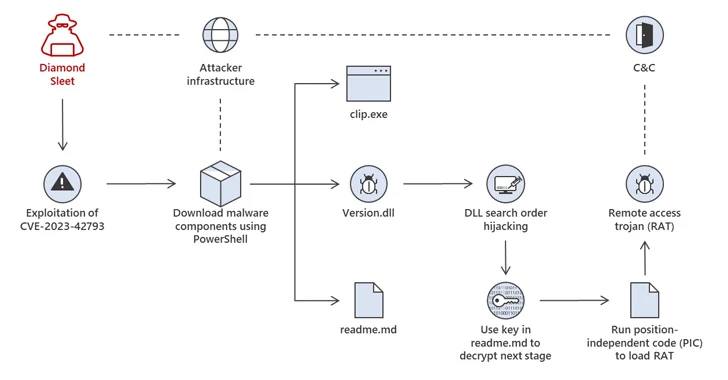
[ad_1] Oct 19, 2023Newsroom North Korean threat actors are actively exploiting a critical security flaw in JetBrains TeamCity to opportunistically breach vulnerable servers, according to Microsoft. The attacks, which entail the exploitation of CVE-2023-42793 (CVSS score: 9.8), have been attributed to Diamond Sleet (aka Labyrinth Chollima) and Onyx Sleet (aka Andariel or Silent Chollima). It’s…
Blog
Google TAG Detects State-Backed Threat Actors Exploiting WinRAR Flaw
[ad_1] Oct 19, 2023NewsroomCyber Threat / Vulnerability A number of state-back threat actors from Russia and China have been observed exploiting a recent security flaw in the WinRAR archiver tool for Windows as part of their operations. The vulnerability in question is CVE-2023-38831 (CVSS score: 7.8), which allows attackers to execute arbitrary code when a…
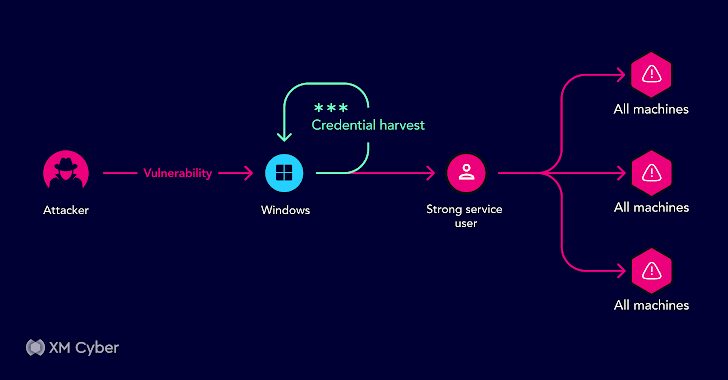
Unraveling Real-Life Attack Paths – Key Lessons Learned
[ad_1] In the ever-evolving landscape of cybersecurity, attackers are always searching for vulnerabilities and exploits within organizational environments. They don’t just target single weaknesses; they’re on the hunt for combinations of exposures and attack methods that can lead them to their desired objective. Despite the presence of numerous security tools, organizations often have to deal…
Lazarus Group Targeting Defense Experts with Fake Interviews via Trojanized VNC Apps
[ad_1] Oct 18, 2023NewsroomCyber Attack / Malware The North Korea-linked Lazarus Group (aka Hidden Cobra or TEMP.Hermit) has been observed using trojanized versions of Virtual Network Computing (VNC) apps as lures to target the defense industry and nuclear engineers as part of a long-running campaign known as Operation Dream Job. “The threat actor tricks job…
Critical Citrix NetScaler Flaw Exploited to Target from Government, Tech Firms
[ad_1] Oct 18, 2023NewsroomEnterprise Security / Vulnerability Citrix is warning of exploitation of a recently disclosed critical security flaw in NetScaler ADC and Gateway appliances that could result in exposure of sensitive information. Tracked as CVE-2023-4966 (CVSS score: 9.4), the vulnerability impacts the following supported versions – NetScaler ADC and NetScaler Gateway 14.1 before 14.1-8.50…
Qubitstrike Targets Jupyter Notebooks with Crypto Mining and Rootkit Campaign
[ad_1] Oct 18, 2023NewsroomRootkit / Cryptocurrency A threat actor, presumably from Tunisia, has been linked to a new campaign targeting exposed Jupyter Notebooks in a two-fold attempt to illicitly mine cryptocurrency and breach cloud environments. Dubbed Qubitstrike by Cado, the intrusion set utilizes Telegram API to exfiltrate cloud service provider credentials following a successful compromise….
Cyber Espionage via Secure USBs Targets APAC Governments
[ad_1] Oct 18, 2023NewsroomCyber Espionage / Malware Government entities in the Asia-Pacific (APAC) region are the target of a long-running cyber espionage campaign dubbed TetrisPhantom. “The attacker covertly spied on and harvested sensitive data from APAC government entities by exploiting a particular type of secure USB drive, protected by hardware encryption to ensure the secure…
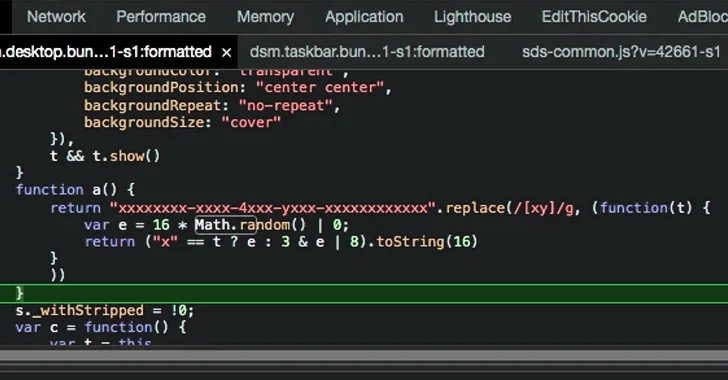
New Admin Takeover Vulnerability Exposed in Synology’s DiskStation Manager
[ad_1] Oct 18, 2023NewsroomVulnerability / Data Security A medium-severity flaw has been discovered in Synology’s DiskStation Manager (DSM) that could be exploited to decipher an administrator’s password and remotely hijack the account. “Under some rare conditions, an attacker could leak enough information to restore the seed of the pseudorandom number generator (PRNG), reconstruct the admin…
Employee Falls Victim to Phishing Attack
[ad_1] Oct 18, 2023NewsroomData Breach / Network Security Taiwanese networking equipment manufacturer D-Link has confirmed a data breach that led to the exposure of what it said is “low-sensitivity and semi-public information.” “The data was confirmed not from the cloud but likely originated from an old D-View 6 system, which reached its end of life…
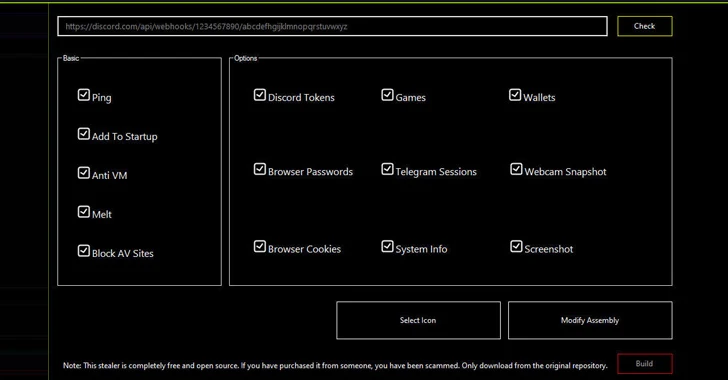
A Playground for Nation-State Hackers Targeting Critical Infrastructure
[ad_1] Oct 17, 2023NewsroomMalware / APT In what’s the latest evolution of threat actors abusing legitimate infrastructure for nefarious ends, new findings show that nation-state hacking groups have entered the fray in leveraging the social platform for targeting critical infrastructure. Discord, in recent years, has become a lucrative target, acting as a fertile ground for…