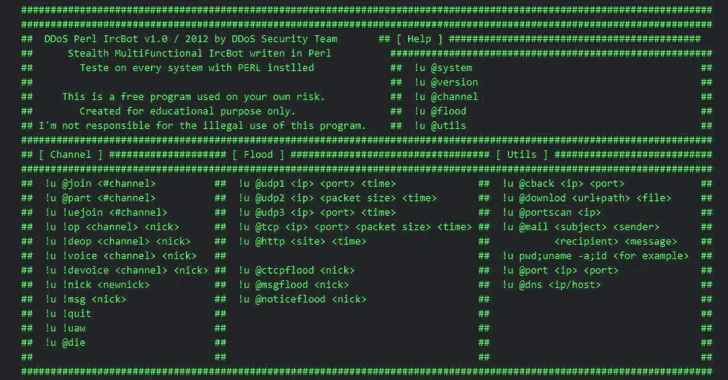
[ad_1] Oct 12, 2023Newsroom The threat actors behind ShellBot are leveraging IP addresses transformed into its hexadecimal notation to infiltrate poorly managed Linux SSH servers and deploy the DDoS malware. “The overall flow remains the same, but the download URL used by the threat actor to install ShellBot has changed from a regular IP address…
Blog
Researchers Uncover Malware Posing as WordPress Caching Plugin
[ad_1] Oct 12, 2023NewsroomWebsite Security / WordPress Cybersecurity researchers have shed light on a new sophisticated strain of malware that masquerades a WordPress plugin to stealthily create administrator accounts and remotely control a compromised site. “Complete with a professional looking opening comment implying it is a caching plugin, this rogue code contains numerous functions, adds…
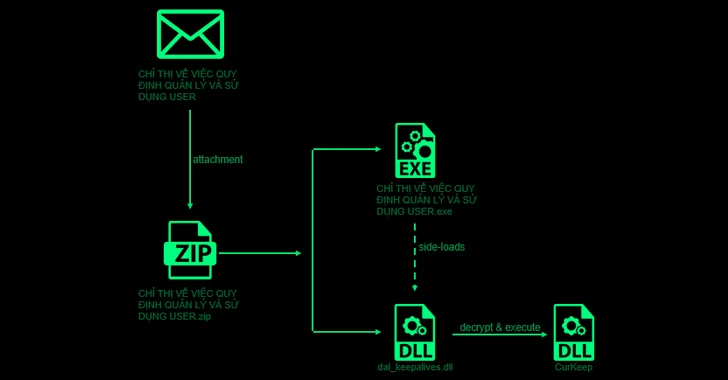
Researchers Uncover Ongoing Attacks Targeting Asian Governments and Telecom Giants
[ad_1] Oct 12, 2023NewsroomCyber Attack / Malware High-profile government and telecom entities in Asia have been targeted as part of an ongoing campaign since 2021 that’s designed to deploy basic backdoors and loaders for delivering next-stage malware. Cybersecurity company Check Point is tracking the activity under the name Stayin’ Alive. Targets include organizations located in…
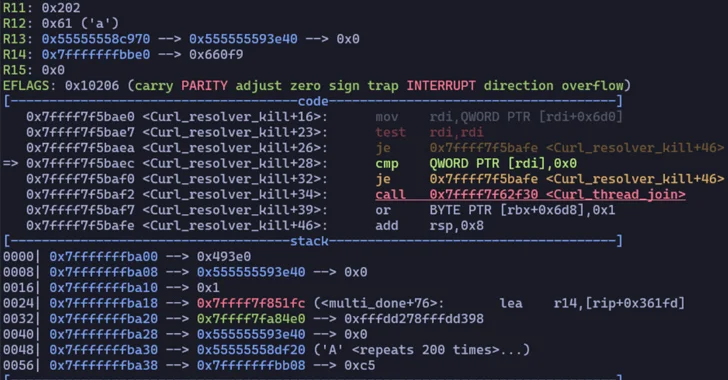
Two High-Risk Security Flaws Discovered in Curl Library
[ad_1] Oct 12, 2023NewsroomVulnerability / Software Security Patches have been released for two security flaws impacting the Curl data transfer library, the most severe of which could potentially result in code execution. The list of vulnerabilities is as follows – CVE-2023-38545 (CVSS score: 7.5) – SOCKS5 heap-based buffer overflow vulnerability CVE-2023-38546 (CVSS score: 5.0) –…
Take an Offensive Approach to Password Security by Continuously Monitoring for Breached Passwords
[ad_1] Oct 11, 2023The Hacker NewsPassword Security / Data Safety Passwords are at the core of securing access to an organization’s data. However, they also come with security vulnerabilities that stem from their inconvenience. With a growing list of credentials to keep track of, the average end-user can default to shortcuts. Instead of creating a…
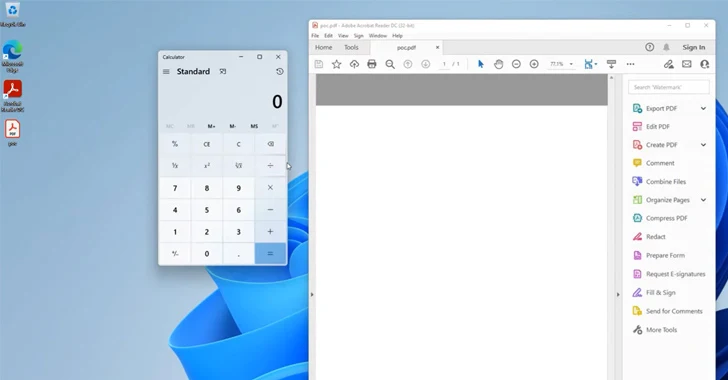
U.S. Cybersecurity Agency Warns of Actively Exploited Adobe Acrobat Reader Vulnerability
[ad_1] Oct 11, 2023NewsroomVulnerability / Exploit The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a high-severity flaw in Adobe Acrobat Reader to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. Tracked as CVE-2023-21608 (CVSS score: 7.8), the vulnerability has been described as a use-after-free bug that can be exploited…
Over 17,000 WordPress Sites Compromised by Balada Injector in September 2023
[ad_1] Oct 11, 2023NewsroomWebsite Security / Hacking More than 17,000 WordPress websites have been compromised in the month of September 2023 with malware known as Balada Injector, nearly twice the number of detections in August. Of these, 9,000 of the websites are said to have been infiltrated using a recently disclosed security flaw in the…
Microsoft Releases October 2023 Patches for 103 Flaws, Including 2 Active Exploits
[ad_1] Oct 11, 2023NewsroomVulnerability / Endpoint Security Microsoft has released its Patch Tuesday updates for October 2023, addressing a total of 103 flaws in its software, two of which have come under active exploitation in the wild. Of the 103 flaws, 13 are rated Critical and 90 are rated Important in severity. This is apart…
Microsoft Warns of Nation-State Hackers Exploiting Critical Atlassian Confluence Vulnerability
[ad_1] Oct 11, 2023NewsroomCyber Attack / Vulnerability Microsoft has linked the exploitation of a recently disclosed critical flaw in Atlassian Confluence Data Center and Server to a nation-state actor it tracks as Storm-0062 (aka DarkShadow or Oro0lxy). The tech giant’s threat intelligence team said it observed in-the-wild abuse of the vulnerability since September 14, 2023….
HTTP/2 Rapid Reset Zero-Day Vulnerability Exploited to Launch Record DDoS Attacks
[ad_1] Oct 10, 2023NewsroomServer Security / Vulnerability Amazon Web Services (AWS), Cloudflare, and Google on Tuesday said they took steps to mitigate record-breaking distributed denial-of-service (DDoS) attacks that relied on a novel technique called HTTP/2 Rapid Reset. The layer 7 attacks were detected in late August 2023, the companies said in a coordinated disclosure. The…