[ad_1] Introduction In today’s interconnected digital ecosystem, Application Programming Interfaces (APIs) play a pivotal role in enabling seamless communication and data exchange between various software applications and systems. APIs act as bridges, facilitating the sharing of information and functionalities. However, as the use of APIs continues to rise, they have become an increasingly attractive target…
Blog
Scattered Spider Getting SaaS-y in the Cloud
[ad_1] LUCR-3 overlaps with groups such as Scattered Spider, Oktapus, UNC3944, and STORM-0875 and is a financially motivated attacker that leverages the Identity Provider (IDP) as initial access into an environment with the goal of stealing Intellectual Property (IP) for extortion. LUCR-3 targets Fortune 2000 companies across various sectors, including but not limited to Software,…
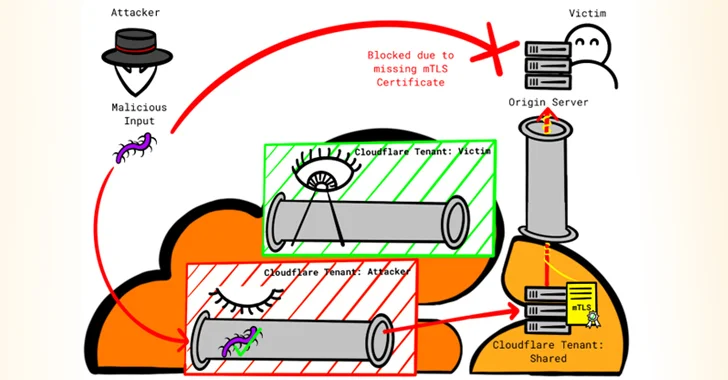
Researcher Reveals New Techniques to Bypass Cloudflare’s Firewall and DDoS Protection
[ad_1] Firewall and distributed denial-of-service (DDoS) attack prevention mechanisms in Cloudflare can be circumvented by exploiting gaps in cross-tenant security controls, defeating the very purpose of these safeguards, it has emerged. “Attackers can utilize their own Cloudflare accounts to abuse the per-design trust-relationship between Cloudflare and the customers’ websites, rendering the protection mechanism ineffective,” Certitude…
Protecting your IT infrastructure with Security Configuration Assessment (SCA)
[ad_1] Oct 03, 2023The Hacker NewsNetwork Security / XDR / SIEM Security Configuration Assessment (SCA) is critical to an organization’s cybersecurity strategy. SCA aims to discover vulnerabilities and misconfigurations that malicious actors exploit to gain unauthorized access to systems and data. Regular security configuration assessments are essential in maintaining a secure and compliant environment, as…
API Security Trends 2023 – Have Organizations Improved their Security Posture?
[ad_1] Oct 03, 2023The Hacker NewsAPI Security / Data Security APIs, also known as application programming interfaces, serve as the backbone of modern software applications, enabling seamless communication and data exchange between different systems and platforms. They provide developers with an interface to interact with external services, allowing them to integrate various functionalities into their…
Over 3 Dozen Data-Stealing Malicious npm Packages Found Targeting Developers
[ad_1] Oct 03, 2023NewsroomSoftware Security / Hacking Nearly three dozen counterfeit packages have been discovered in the npm package repository that are designed to exfiltrate sensitive data from developer systems, according to findings from Fortinet FortiGuard Labs. One set of packages – named @expue/webpack, @expue/core, @expue/vue3-renderer, @fixedwidthtable/fixedwidthtable, and @virtualsearchtable/virtualsearchtable – harbored an obfuscated JavaScript file…
PyTorch Models Vulnerable to Remote Code Execution via ShellTorch
[ad_1] Oct 03, 2023NewsroomArtificial Intelligence / Cyber Threat Cybersecurity researchers have disclosed multiple critical security flaws in the TorchServe tool for serving and scaling PyTorch models that could be chained to achieve remote code execution on affected systems. Israel-based runtime application security company Oligo, which made the discovery, has coined the vulnerabilities ShellTorch. “These vulnerabilities…
Qualcomm Releases Patch for 3 new Zero-Days Under Active Exploitation
[ad_1] Oct 03, 2023NewsroomZero Day / Vulnerability Chipmaker Qualcomm has released security updates to address 17 vulnerabilities in various components, while warning that three other zero-days have come under active exploitation. Of the 17 flaws, three are rated Critical, 13 are rated High, and one is rated Medium in severity. “There are indications from Google…
Microsoft Warns of Cyber Attacks Attempting to Breach Cloud via SQL Server Instance
[ad_1] Oct 04, 2023NewsroomCloud Security / Cyber Threat Microsoft has detailed a new campaign in which attackers unsuccessfully attempted to move laterally to a cloud environment through an SQL Server instance. “The attackers initially exploited a SQL injection vulnerability in an application within the target’s environment,” security researchers Sunders Bruskin, Hagai Ran Kestenberg, and Fady…
Rogue npm Package Deploys Open-Source Rootkit in New Supply Chain Attack
[ad_1] Oct 04, 2023NewsroomSupply Chain / Malware A new deceptive package hidden within the npm package registry has been uncovered deploying an open-source rootkit called r77, marking the first time a rogue package has delivered rootkit functionality. The package in question is node-hide-console-windows, which mimics the legitimate npm package node-hide-console-window in what’s an instance of…