[ad_1] May 03, 2025Ravie LakshmananMalware / Operational Technology An Iranian state-sponsored threat group has been attributed to a long-term cyber intrusion aimed at a critical national infrastructure (CNI) in the Middle East that lasted nearly two years. The activity, which lasted from at least May 2023 to February 2025, entailed “extensive espionage operations and suspected…
Blog
Malicious Go Modules Deliver Disk-Wiping Linux Malware in Advanced Supply Chain Attack
[ad_1] May 03, 2025Ravie LakshmananSupply Chain Attack / Malware Cybersecurity researchers have discovered three malicious Go modules that include obfuscated code to fetch next-stage payloads that can irrevocably overwrite a Linux system’s primary disk and render it unbootable. The names of the packages are listed below – github[.]com/truthfulpharm/prototransform github[.]com/blankloggia/go-mcp github[.]com/steelpoor/tlsproxy “Despite appearing legitimate, these modules…
TikTok Slammed With €530 Million GDPR Fine for Sending E.U. Data to China
[ad_1] May 02, 2025Ravie LakshmananData Privacy / Social Media Ireland’s Data Protection Commission (DPC) on Tuesday fined popular video-sharing platform TikTok €530 million ($601 million) for infringing data protection regulations in the region by transferring European users’ data to China. “TikTok infringed the GDPR regarding its transfers of EEA [European Economic Area] User Data to…
How to Automate CVE and Vulnerability Advisory Response with Tines
[ad_1] May 02, 2025The Hacker NewsVulnerability Management / Security Operations Run by the team at workflow orchestration and AI platform Tines, the Tines library features pre-built workflows shared by security practitioners from across the community – all free to import and deploy through the platform’s Community Edition. A recent standout is a workflow that automates…
MintsLoader Drops GhostWeaver via Phishing, ClickFix — Uses DGA, TLS for Stealth Attacks
[ad_1] May 02, 2025Ravie LakshmananMalware / Threat Intelligence The malware loader known as MintsLoader has been used to deliver a PowerShell-based remote access trojan called GhostWeaver. “MintsLoader operates through a multi-stage infection chain involving obfuscated JavaScript and PowerShell scripts,” Recorded Future’s Insikt Group said in a report shared with The Hacker News. “The malware employs…
Microsoft Sets Passkeys Default for New Accounts; 15 Billion Users Gain Passwordless Support
[ad_1] May 02, 2025Ravie LakshmananPassword Security / Windows A year after Microsoft announced passkeys support for consumer accounts, the tech giant has announced a big change that pushes individuals signing up for new accounts to use the phishing-resistant authentication method by default. “Brand new Microsoft accounts will now be ‘passwordless by default,’” Microsoft’s Joy Chik…
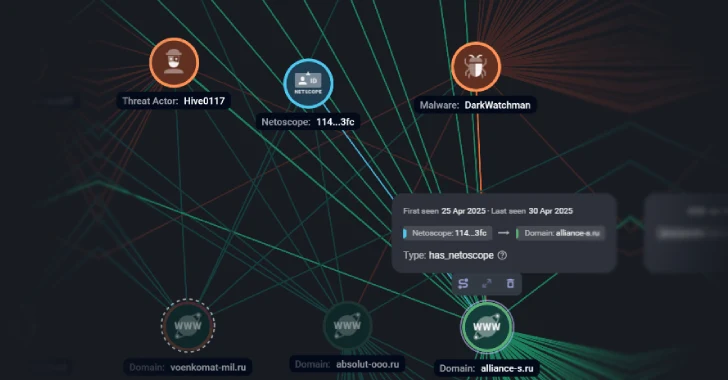
DarkWatchman, Sheriff Malware Hit Russia and Ukraine with Stealth and Nation-Grade Tactics
[ad_1] Russian companies have been targeted as part of a large-scale phishing campaign that’s designed to deliver a known malware called DarkWatchman. Targets of the attacks include entities in the media, tourism, finance and insurance, manufacturing, retail, energy, telecom, transport, and biotechnology sectors, Russian cybersecurity company F6 said. The activity is assessed to be the…
Fake Security Plugin on WordPress Enables Remote Admin Access for Attackers
[ad_1] May 01, 2025Ravie LakshmananMalware / Web Skimming Cybersecurity researchers have shed light on a new campaign targeting WordPress sites that disguises the malware as a security plugin. The plugin, which goes by the name “WP-antymalwary-bot.php,” comes with a variety of features to maintain access, hide itself from the admin dashboard, and execute remote code….
Claude AI Exploited to Operate 100+ Fake Political Personas in Global Influence Campaign
[ad_1] May 01, 2025Ravie LakshmananArtificial Intelligence / Disinformation Artificial intelligence (AI) company Anthropic has revealed that unknown threat actors leveraged its Claude chatbot for an “influence-as-a-service” operation to engage with authentic accounts across Facebook and X. The sophisticated activity, branded as financially-motivated, is said to have used its AI tool to orchestrate 100 distinct persons…
Why top SOC teams are shifting to Network Detection and Response
[ad_1] Security Operations Center (SOC) teams are facing a fundamentally new challenge — traditional cybersecurity tools are failing to detect advanced adversaries who have become experts at evading endpoint-based defenses and signature-based detection systems. The reality of these “invisible intruders” is driving a significant need for a multi-layered approach to detecting threats, including Network Detection…