[ad_1] Apr 28, 2025Ravie LakshmananCybersecurity / Hacking News What happens when cybercriminals no longer need deep skills to breach your defenses? Today’s attackers are armed with powerful tools that do the heavy lifting — from AI-powered phishing kits to large botnets ready to strike. And they’re not just after big corporations. Anyone can be a…
Blog
WooCommerce Users Targeted by Fake Patch Phishing Campaign Deploying Site Backdoors
[ad_1] Apr 28, 2025Ravie LakshmananWebsite Security / Malware Cybersecurity researchers are warning about a large-scale phishing campaign targeting WooCommerce users with a fake security alert urging them to download a “critical patch” but deploy a backdoor instead. WordPress security company Patchstack described the activity as sophisticated and a variant of another campaign observed in December…
Hackers Exploit Critical Craft CMS Flaws; Hundreds of Servers Likely Compromised
[ad_1] Apr 28, 2025Ravie LakshmananWeb Application Security / Vulnerability Threat actors have been observed exploiting two newly disclosed critical security flaws in Craft CMS in zero-day attacks to breach servers and gain unauthorized access. The attacks, first observed by Orange Cyberdefense SensePost on February 14, 2025, involve chaining the below vulnerabilities – CVE-2024-58136 (CVSS score:…
Storm-1977 Hits Education Clouds with AzureChecker, Deploys 200+ Crypto Mining Containers
[ad_1] Apr 27, 2025Ravie LakshmananKubernetes / Cloud Security Microsoft has revealed that a threat actor it tracks as Storm-1977 has conducted password spraying attacks against cloud tenants in the education sector over the past year. “The attack involves the use of AzureChecker.exe, a Command Line Interface (CLI) tool that is being used by a wide…
ToyMaker Uses LAGTOY to Sell Access to CACTUS Ransomware Gangs for Double Extortion
[ad_1] Apr 26, 2025Ravie LakshmananMalware / Vulnerability Cybersecurity researchers have detailed the activities of an initial access broker (IAB) dubbed ToyMaker that has been observed handing over access to double extortion ransomware gangs like CACTUS. The IAB has been assessed with medium confidence to be a financially motivated threat actor, scanning for vulnerable systems and…
DslogdRAT Malware Deployed via Ivanti ICS Zero-Day CVE-2025-0282 in Japan Attacks
[ad_1] Apr 25, 2025Ravie LakshmananVulnerability / Network Security Cybersecurity researchers are warning about a new malware called DslogdRAT that’s installed following the exploitation of a now-patched security flaw in Ivanti Connect Secure (ICS). The malware, along with a web shell, were “installed by exploiting a zero-day vulnerability at that time, CVE-2025-0282, during attacks against organizations…
North Korean Hackers Spread Malware via Fake Crypto Firms and Job Interview Lures
[ad_1] North Korea-linked threat actors behind the Contagious Interview have set up front companies as a way to distribute malware during the fake hiring process. “In this new campaign, the threat actor group is using three front companies in the cryptocurrency consulting industry—BlockNovas LLC (blocknovas[.] com), Angeloper Agency (angeloper[.]com), and SoftGlide LLC (softglide[.]co)—to spread malware…
Why NHIs Are Security’s Most Dangerous Blind Spot
[ad_1] When we talk about identity in cybersecurity, most people think of usernames, passwords, and the occasional MFA prompt. But lurking beneath the surface is a growing threat that does not involve human credentials at all, as we witness the exponential growth of Non-Human Identities (NHIs). At the top of mind when NHIs are mentioned,…
SAP Confirms Critical NetWeaver Flaw Amid Suspected Zero-Day Exploitation by Hackers
[ad_1] Apr 25, 2025Ravie LakshmananVulnerability / Enterprise Security Threat actors are likely exploiting a new vulnerability in SAP NetWeaver to upload JSP web shells with the goal of facilitating unauthorized file uploads and code execution. “The exploitation is likely tied to either a previously disclosed vulnerability like CVE-2017-9844 or an unreported remote file inclusion (RFI)…
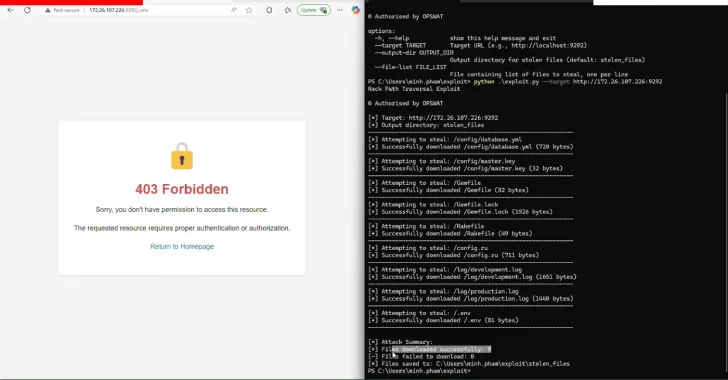
Researchers Identify Rack::Static Vulnerability Enabling Data Breaches in Ruby Servers
[ad_1] Apr 25, 2025Ravie LakshmananVulnerability / Data Breach Cybersecurity researchers have disclosed three security flaws in the Rack Ruby web server interface that, if successfully exploited, could enable attackers to gain unauthorized access to files, inject malicious data, and tamper with logs under certain conditions. The vulnerabilities, flagged by cybersecurity vendor OPSWAT, are listed below…