[ad_1]
An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick them into downloading a Python backdoor.
Cybersecurity firm Securonix is tracking the activity under the name DEV#POPPER, linking it to North Korean threat actors.
“During these fraudulent interviews, the developers are often asked to perform tasks that involve downloading and running software from sources that appear legitimate, such as GitHub,” security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said. “The software contained a malicious Node JS payload that, once executed, compromised the developer’s system.”
Details of the campaign first emerged in late November 2023, when Palo Alto Networks Unit 42 detailed an activity cluster dubbed Contagious Interview in which the threat actors pose as employers to lure software developers into installing malware such as BeaverTail and InvisibleFerret through the interview process.
Then earlier this February, software supply chain security firm Phylum uncovered a set of malicious packages on the npm registry that delivered the same malware families to siphon sensitive information from compromised developer systems.
It’s worth noting that Contagious Interview is said to be disparate from Operation Dream Job (aka DeathNote or NukeSped), with Unit 42 telling The Hacker News that the former is “focused on targeting developers, mainly through fake identities in freelance job portals, and the next stages involve the use of developer tools and npm packages leading to […] BeaverTail and InvisibleFerret.”
Operation Dream Job, linked to the prolific Lazarus Group from North Korea, is a long-running offensive campaign that sends unsuspecting professionals employed in various sectors like aerospace, cryptocurrency, defense, and others malicious files dressed as job offers to distribute malware.
First uncovered by Israeli cybersecurity firm ClearSky at the start of 2020, it also exhibits overlaps with two other Lazarus clusters known as Operation In(ter)ception and Operation North Star.
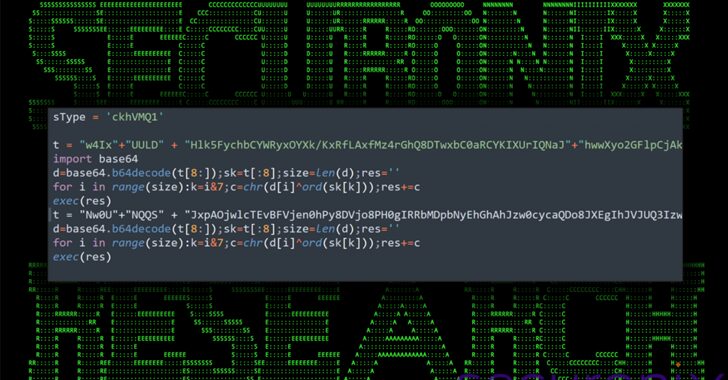
The attack chain detailed by Securonix starts with a ZIP archive hosted on GitHub that’s likely sent to the target as part of the interview. Present within the file is a seemingly innocuous npm module that harbors a malicious JavaScript file codenamed BeaverTail that acts as an information stealer and a loader for a Python backdoor called InvisibleFerret that’s retrieved from a remote server.
The implant, besides gathering system information, is capable of command execution, file enumeration and exfiltration, and clipboard and keystroke logging.
The development is a sign that North Korean threat actors continue to hone a raft of weapons for their cyber attack arsenal, consistently updating their tradecraft with improved abilities to hide their actions and blend in on host systems and networks, not to mention siphon off data and turn compromises into financial gain.
“When it comes to attacks which originate through social engineering, it’s critical to maintain a security-focused mindset, especially during intense and stressful situations like job interviews,” Securonix researchers said.
“The attackers behind the DEV#POPPER campaigns abuse this, knowing that the person on the other end is in a highly distracted and in a much more vulnerable state.”
[ad_2]