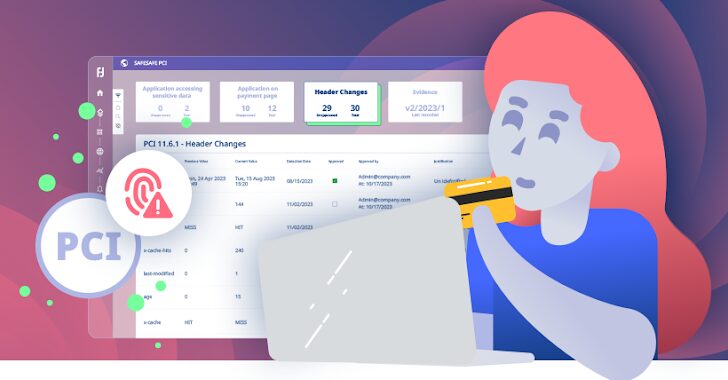
[ad_1] Sep 16, 2024The Hacker NewsPayment Security / Data Protection The PCI DSS landscape is evolving rapidly. With the Q1 2025 deadline looming ever larger, businesses are scrambling to meet the stringent new requirements of PCI DSS v4.0. Two sections in particular, 6.4.3 and 11.6.1, are troublesome as they demand that organizations rigorously monitor and…
Category: Cyber News
Designing an Identity-Focused Incident Response Playbook
[ad_1] Sep 16, 2024The Hacker NewsIdentity Protection / Incident Response Imagine this… You arrive at work to a chaotic scene. Systems are down, panic is in the air. The culprit? Not a rogue virus, but a compromised identity. The attacker is inside your walls, masquerading as a trusted user. This isn’t a horror movie, it’s…
SolarWinds Issues Patch for Critical ARM Vulnerability Enabling RCE Attacks
[ad_1] Sep 17, 2024Ravie LakshmananSoftware Security / Data Protection SolarWinds has released fixes to address two security flaws in its Access Rights Manager (ARM) software, including a critical vulnerability that could result in remote code execution. The vulnerability, tracked as CVE-2024-28991, is rated 9.0 out of a maximum of 10.0 on the CVSS scoring system….
Meta to Train AI Models Using Public U.K. Facebook and Instagram Posts
[ad_1] Sep 17, 2024Ravie LakshmananArtificial Intelligence / Regulatory Compliance Meta has announced that it will begin training its artificial intelligence (AI) systems using public content shared by adult users across Facebook and Instagram in the U.K. in the coming months. “This means that our generative AI models will reflect British culture, history, and idiom, and…
How to Investigate ChatGPT activity in Google Workspace
[ad_1] Sep 17, 2024The Hacker NewsGenAI Security / SaaS Security When you connect your organization’s Google Drive account to ChatGPT, you grant ChatGPT extensive permissions for not only your personal files, but resources across your entire shared drive. As you might imagine, this introduces an array of cybersecurity challenges. This post outlines how to see…
Patch Issued for Critical VMware vCenter Flaw Allowing Remote Code Execution
[ad_1] Sep 18, 2024Ravie LakshmananVirtualization / Network Security Broadcom on Tuesday released updates to address a critical security flaw impacting VMware vCenter Server that could pave the way for remote code execution. The vulnerability, tracked as CVE-2024-38812 (CVSS score: 9.8), has been described as a heap-overflow vulnerability in the DCE/RPC protocol. “A malicious actor with…
GSMA Plans End-to-End Encryption for Cross-Platform RCS Messaging
[ad_1] Sep 18, 2024Ravie LakshmananMobile Security / Encryption The GSM Association (GSMA), the governing body that oversees the development of the Rich Communications Services (RCS) protocol, on Tuesday, said it’s working towards implementing end-to-end encryption (E2EE) to secure messages sent between the Android and iOS ecosystems. “The next major milestone is for the RCS Universal…
North Korean Hackers Target Energy and Aerospace Industries with New MISTPEN Malware
[ad_1] Sep 18, 2024Ravie LakshmananCyber Espionage / Malware A North Korea-linked cyber-espionage group has been observed leveraging job-themed phishing lures to target prospective victims in energy and aerospace verticals and infect them with a previously undocumented backdoor dubbed MISTPEN. The activity cluster is being tracked by Google-owned Mandiant under the moniker UNC2970, which it said…
Why Pay A Pentester?
[ad_1] The evolution of software always catches us by surprise. I remember betting against the IBM computer Deep Blue during its chess match against the grandmaster Garry Kasparov in 1997, only to be stunned when the machine claimed victory. Fast forward to today, would we have imagined just three years ago that a chatbot could…
The SSPM Justification Kit
[ad_1] SaaS applications contain a wealth of sensitive data and are central to business operations. Despite this, far too many organizations rely on half measures and hope their SaaS stack will remain secure. Unfortunately, this approach is lacking and will leave security teams blind to threat prevention and detection, as well as open to regulatory…