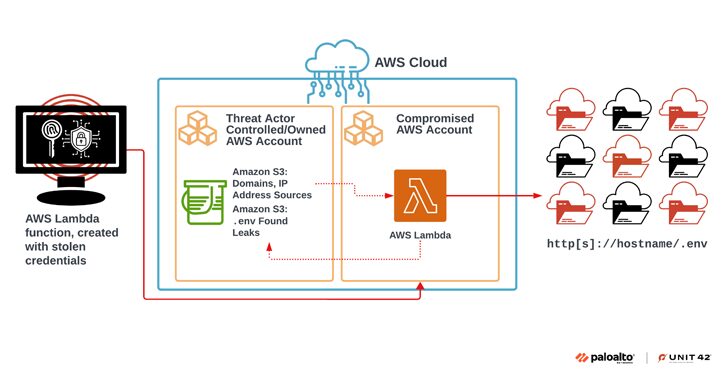
[ad_1] Aug 16, 2024Ravie LakshmananCloud Security / Application Security A large-scale extortion campaign has compromised various organizations by taking advantage of publicly accessible environment variable files (.env) that contain credentials associated with cloud and social media applications. “Multiple security missteps were present in the course of this campaign, including the following: Exposing environment variables, using…
Category: Cyber News
Russian Hackers Using Fake Brand Sites to Spread DanaBot and StealC Malware
[ad_1] Aug 16, 2024Ravie LakshmananMalware / Data Theft Cybersecurity researchers have shed light on a sophisticated information stealer campaign that impersonates legitimate brands to distribute malware like DanaBot and StealC. The activity cluster, orchestrated by Russian-speaking cybercriminals and collectively codenamed Tusk, is said to encompass several sub-campaigns, leveraging the reputation of the platforms to trick…
Identity Threat Detection and Response Solution Guide
[ad_1] Aug 15, 2024The Hacker NewsIdentity Security / Threat Detection The Emergence of Identity Threat Detection and Response Identity Threat Detection and Response (ITDR) has emerged as a critical component to effectively detect and respond to identity-based attacks. Threat actors have shown their ability to compromise the identity infrastructure and move laterally into IaaS, Saas,…
SolarWinds Releases Patch for Critical Flaw in Web Help Desk Software
[ad_1] Aug 15, 2024Ravie LakshmananEnterprise Security / Vulnerability SolarWinds has released patches to address a critical security vulnerability in its Web Help Desk software that could be exploited to execute arbitrary code on susceptible instances. The flaw, tracked as CVE-2024-28986 (CVSS score: 9.8), has been described as a deserialization bug. “SolarWinds Web Help Desk was…
Russian-Linked Hackers Target Eastern European NGOs and Media
[ad_1] Aug 15, 2024Ravie LakshmananCyber Attack / Social Engineering Russian and Belarusian non-profit organizations, Russian independent media, and international non-governmental organizations active in Eastern Europe have become the target of two separate spear-phishing campaigns orchestrated by threat actors whose interests align with that of the Russian government. While one of the campaigns – dubbed River…
How to Augment Your Password Security with EASM
[ad_1] Aug 14, 2024The Hacker NewsPassword Security / Cyber Security Simply relying on traditional password security measures is no longer sufficient. When it comes to protecting your organization from credential-based attacks, it is essential to lock down the basics first. Securing your Active Directory should be a priority – it is like making sure a…
Black Basta-Linked Attackers Target Users with SystemBC Malware
[ad_1] Aug 14, 2024Ravie LakshmananMalware / Network Security An ongoing social engineering campaign with alleged links to the Black Basta ransomware group has been linked to “multiple intrusion attempts” with the goal of conducting credential theft and deploying a malware dropper called SystemBC. “The initial lure being utilized by the threat actors remains the same:…
Belarusian-Ukrainian Hacker Extradited to U.S. for Ransomware and Cybercrime Charges
[ad_1] A coalition of law enforcement agencies coordinated by the U.K. National Crime Agency (NCA) has led to the arrest and extradition of a Belarussian and Ukrainian dual-national believed to be associated with Russian-speaking cybercrime groups. Maksim Silnikau (aka Maksym Silnikov), 38, went by the online monikers J.P. Morgan, xxx, and lansky. He was extradited…
Researchers Uncover Vulnerabilities in AI-Powered Azure Health Bot Service
[ad_1] Aug 13, 2024Ravie LakshmananHealthcare / Vulnerability Cybersecurity researchers have discovered two security flaws in Microsoft’s Azure Health Bot Service that, if exploited, could permit a malicious actor to achieve lateral movement within customer environments and access sensitive patient data. The critical issues, now patched by Microsoft, could have allowed access to cross-tenant resources within…
New T-Head CPU Bugs Expose Devices to Unrestricted Attacks
[ad_1] Aug 13, 2024Ravie LakshmananVulnerability / Hardware Security A team of researchers from the CISPA Helmholtz Center for Information Security in Germany has disclosed an architectural bug impacting Chinese chip company T-Head’s XuanTie C910 and C920 RISC-V CPUs that could allow attackers to gain unrestricted access to susceptible devices. The vulnerability has been codenamed GhostWrite….