[ad_1] Cybersecurity researchers have disclosed a privilege escalation vulnerability impacting Google Cloud Platform’s Cloud Functions service that an attacker could exploit to access other services and sensitive data in an unauthorized manner. Tenable has given the vulnerability the name ConfusedFunction. “An attacker could escalate their privileges to the Default Cloud Build Service Account and access…
Category: Cyber News
New SideWinder Cyber Attacks Target Maritime Facilities in Multiple Countries
[ad_1] Jul 30, 2024Ravie LakshmananCyber Espionage / Malware The nation-state threat actor known as SideWinder has been attributed to a new cyber espionage campaign targeting ports and maritime facilities in the Indian Ocean and Mediterranean Sea. The BlackBerry Research and Intelligence Team, which discovered the activity, said targets of the spear-phishing campaign include countries like…
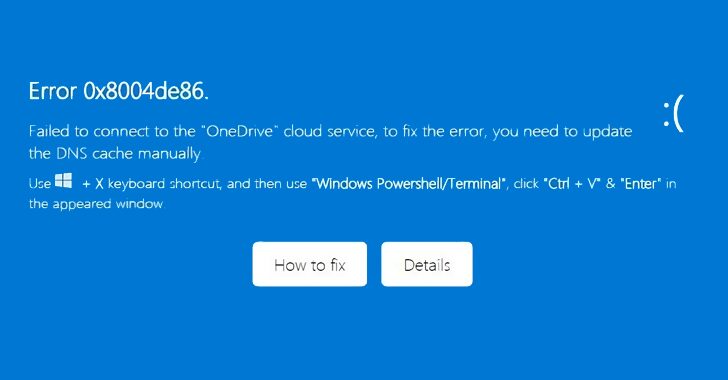
OneDrive Phishing Scam Tricks Users into Running Malicious PowerShell Script
[ad_1] Jul 30, 2024Ravie LakshmananMalware / Email Security Cybersecurity researchers are warning about a new phishing campaign that targets Microsoft OneDrive users with the aim of executing a malicious PowerShell script. “This campaign heavily relies on social engineering tactics to deceive users into executing a PowerShell script, thereby compromising their systems,” Trellix security researcher Rafael…
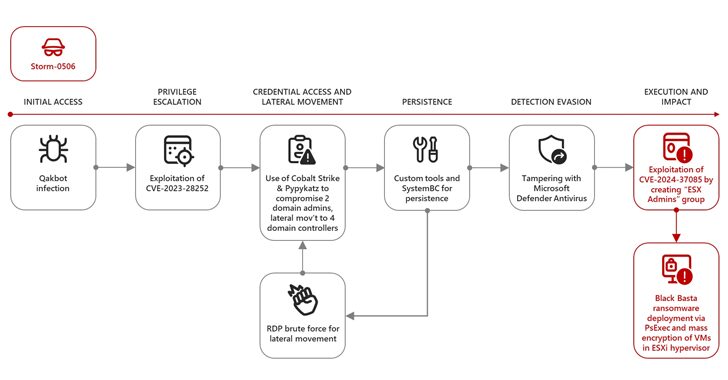
VMware ESXi Flaw Exploited by Ransomware Groups for Admin Access
[ad_1] A recently patched security flaw impacting VMware ESXi hypervisors has been actively exploited by “several” ransomware groups to gain elevated permissions and deploy file-encrypting malware. The attacks involve the exploitation of CVE-2024-37085 (CVSS score: 6.8), an Active Directory integration authentication bypass that allows an attacker to obtain administrative access to the host. “A malicious…
What Enterprises MUST Know about Enterprise Browser Security
[ad_1] Jul 25, 2024The Hacker NewsBrowser Security / Enterprise Security The browser is the nerve center of the modern workspace. Ironically, however, the browser is also one of the least protected threat surfaces of the modern enterprise. Traditional security tools provide little protection against browser-based threats, leaving organizations exposed. Modern cybersecurity requires a new approach…
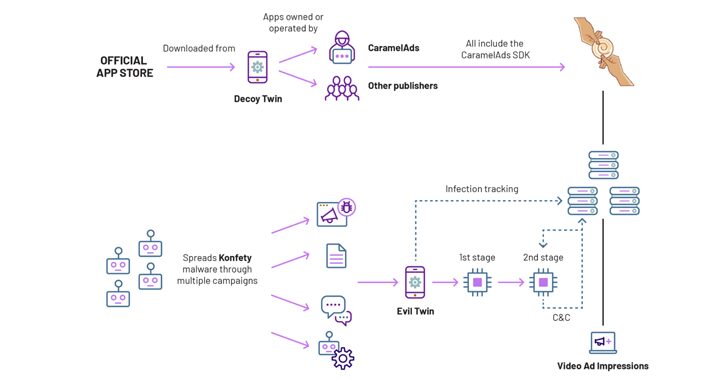
‘Stargazer Goblin’ Creates 3,000 Fake GitHub Accounts for Malware Spread
[ad_1] A threat actor known as Stargazer Goblin has set up a network of inauthentic GitHub accounts to fuel a Distribution-as-a-Service (DaaS) that propagates a variety of information-stealing malware and netting them $100,000 in illicit profits over the past year. The network, which comprises over 3,000 accounts on the cloud-based code hosting platform, spans thousands…
How Searchable Encryption Changes the Data Security Game
[ad_1] Searchable Encryption has long been a mystery. An oxymoron. An unattainable dream of cybersecurity professionals everywhere. Organizations know they must encrypt their most valuable, sensitive data to prevent data theft and breaches. They also understand that organizational data exists to be used. To be searched, viewed, and modified to keep businesses running. Unfortunately, our…
Critical Flaw in Acronis Cyber Infrastructure Exploited in the Wild
[ad_1] Jul 29, 2024Ravie LakshmananEnterprise Security / Data Protection Cybersecurity company Acronis is warning that a now-patched critical security flaw impacting its Cyber Infrastructure (ACI) product has been exploited in the wild. The vulnerability, tracked as CVE-2023-45249 (CVSS score: 9.8), concerns a case of remote code execution that stems from the use of default passwords….
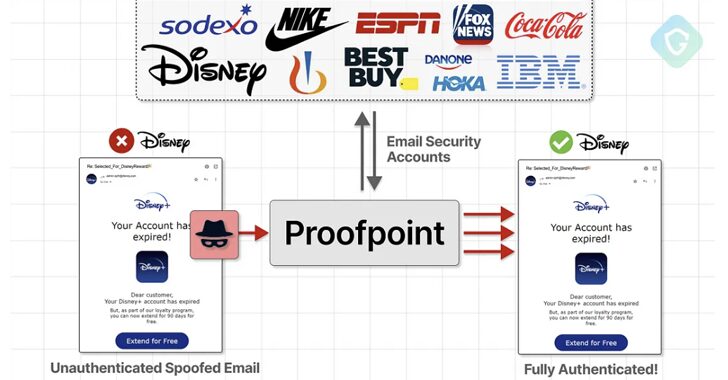
Proofpoint Email Routing Flaw Exploited to Send Millions of Spoofed Phishing Emails
[ad_1] An unknown threat actor has been linked to a massive scam campaign that exploited an email routing misconfiguration in email security vendor Proofpoint’s defenses to send millions of messages spoofing various popular companies like Best Buy, IBM, Nike, and Walt Disney, among others. “These emails echoed from official Proofpoint email relays with authenticated SPF…
Gh0st RAT Trojan Targets Chinese Windows Users via Fake Chrome Site
[ad_1] Jul 29, 2024NewsroomCybersecurity / Cyber Espionage The remote access trojan known as Gh0st RAT has been observed being delivered by an “evasive dropper” called Gh0stGambit as part of a drive-by download scheme targeting Chinese-speaking Windows users. These infections stem from a fake website (“chrome-web[.]com”) serving malicious installer packages masquerading as Google’s Chrome browser, indicating…