[ad_1] While the specifics for security testing vary for applications, web applications, and APIs, a holistic and proactive applications security strategy is essential for all three types. There are six core types of testing that every security professional should know about to secure their applications, regardless of what phase they are in in development or…
Category: Cyber News
Critical Docker Engine Flaw Allows Attackers to Bypass Authorization Plugins
[ad_1] Jul 25, 2024NewsroomContainer Security / Vulnerability Docker is warning of a critical flaw impacting certain versions of Docker Engine that could allow an attacker to sidestep authorization plugins (AuthZ) under specific circumstances. Tracked as CVE-2024-41110, the bypass and privilege escalation vulnerability carries a CVSS score of 10.0, indicating maximum severity. “An attacker could exploit…
Telegram App Flaw Exploited to Spread Malware Hidden in Videos
[ad_1] A zero-day security flaw in Telegram’s mobile app for Android called EvilVideo made it possible for attackers to malicious files disguised as harmless-looking videos. The exploit appeared for sale for an unknown price in an underground forum on June 6, 2024, ESET said. Following responsible disclosure on June 26, the issue was addressed by…
How a Trust Center Solves Your Security Questionnaire Problem
[ad_1] Security questionnaires aren’t just an inconvenience — they’re a recurring problem for security and sales teams. They bleed time from organizations, filling the schedules of professionals with monotonous, automatable work. But what if there were a way to reduce or even altogether eliminate security questionnaires? The root problem isn’t a lack of great questionnaire…
How to Securely Onboard New Employees Without Sharing Temporary Passwords
[ad_1] Jul 23, 2024The Hacker NewsCorporate Security / Data Protection The initial onboarding stage is a crucial step for both employees and employers. However, this process often involves the practice of sharing temporary first-day passwords, which can expose organizations to security risks. Traditionally, IT departments have been cornered into either sharing passwords in plain text…
New ICS Malware ‘FrostyGoop’ Targeting Critical Infrastructure
[ad_1] Jul 23, 2024NewsroomICS Malware / Critical Infrastructure Cybersecurity researchers have discovered what they say is the ninth Industrial Control Systems (ICS)-focused malware that has been used in a disruptive cyber attack targeting an energy company in the Ukrainian city of Lviv earlier this January. Industrial cybersecurity firm Dragos has dubbed the malware FrostyGoop, describing…
Chinese Hackers Target Taiwan and US NGO with MgBot Malware
[ad_1] Jul 23, 2024NewsroomCyber Espionage / Chinese Hackers Organizations in Taiwan and a U.S. non-governmental organization (NGO) based in China have been targeted by a Beijing-affiliated state-sponsored hacking group called Daggerfly using an upgraded set of malware tools. The campaign is a sign that the group “also engages in internal espionage,” Symantec’s Threat Hunter Team,…
Google Abandons Plan to Phase Out Third-Party Cookies in Chrome
[ad_1] Jul 23, 2024NewsroomOnline Privacy / Regulatory Compliance Google on Monday abandoned plans to phase out third-party tracking cookies in its Chrome web browser more than four years after it introduced the option as part of a larger set of a controversial proposal called the Privacy Sandbox. “Instead of deprecating third-party cookies, we would introduce…
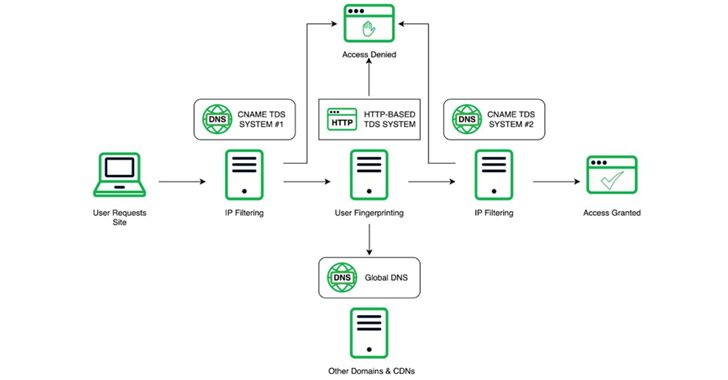
Experts Uncover Chinese Cybercrime Network Behind Gambling and Human Trafficking
[ad_1] The relationship between various TDSs and DNS associated with Vigorish Viper and the final landing experience for the user A Chinese organized crime syndicate with links to money laundering and human trafficking across Southeast Asia has been using an advanced “technology suite” that runs the whole cybercrime supply chain spectrum to spearhead its operations….
PINEAPPLE and FLUXROOT Hacker Groups Abuse Google Cloud for Credential Phishing
[ad_1] Jul 22, 2024NewsroomCloud Security / Phishing Attack A Latin America (LATAM)-based financially motivated actor codenamed FLUXROOT has been observed leveraging Google Cloud serverless projects to orchestrate credential phishing activity, highlighting the abuse of the cloud computing model for malicious purposes. “Serverless architectures are attractive to developers and enterprises for their flexibility, cost effectiveness, and…