[ad_1] Permissions in SaaS platforms like Salesforce, Workday, and Microsoft 365 are remarkably precise. They spell out exactly which users have access to which data sets. The terminology differs between apps, but each user’s base permission is determined by their role, while additional permissions may be granted based on tasks or projects they are involved…
Category: Cyber News
Hackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
[ad_1] May 08, 2024NewsroomWeb Security / Vulnerability A high-severity flaw impacting the LiteSpeed Cache plugin for WordPress is being actively exploited by threat actors to create rogue admin accounts on susceptible websites. The findings come from WPScan, which said that the vulnerability (CVE-2023-40000, CVSS score: 8.3) has been leveraged to set up bogus admin users…
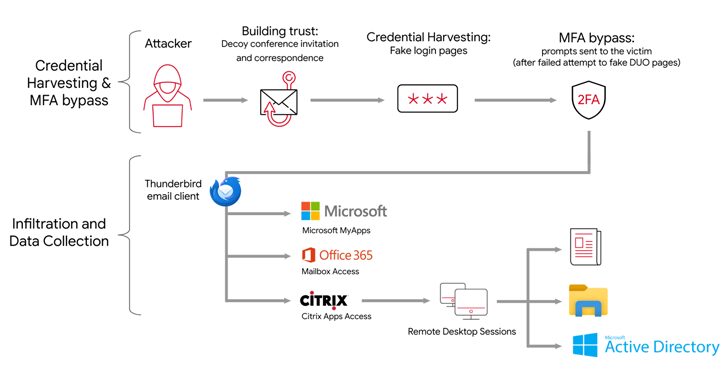
APT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
[ad_1] The Iranian state-backed hacking outfit called APT42 is making use of enhanced social engineering schemes to infiltrate target networks and cloud environments. Targets of the attack include Western and Middle Eastern NGOs, media organizations, academia, legal services and activists, Google Cloud subsidiary Mandiant said in a report published last week. “APT42 was observed posing…
Russian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
[ad_1] The U.K. National Crime Agency (NCA) has unmasked the administrator and developer of the LockBit ransomware operation, revealing it to be a 31-year-old Russian national named Dmitry Yuryevich Khoroshev. In addition, Khoroshev has been sanctioned by the U.K. Foreign, Commonwealth and Development Office (FCD), the U.S. Department of the Treasury’s Office of Foreign Assets…
Russian Operator of BTC-e Crypto Exchange Pleads Guilty to Money Laundering
[ad_1] May 07, 2024NewsroomCryptocurrency / Cybercrime A Russian operator of a now-dismantled BTC-e cryptocurrency exchange has pleaded guilty to money laundering charges from 2011 to 2017. Alexander Vinnik, 44, was charged in January 2017 and taken into custody in Greece in July 2017. He was subsequently extradited to the U.S. in August 2022. Vinnik and…
China-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
[ad_1] May 06, 2024NewsroomNetwork Security / Malware The recently uncovered cyber espionage campaign targeting perimeter network devices from several vendors, including Cisco, may have been the work of China-linked actors, according to new findings from attack surface management firm Censys. Dubbed ArcaneDoor, the activity is said to have commenced around July 2023, with the first…
Critical Tinyproxy Flaw Opens Over 50,000 Hosts to Remote Code Execution
[ad_1] May 06, 2024NewsroomVulnerability / Server Security More than 50% of the 90,310 hosts have been found exposing a Tinyproxy service on the internet that’s vulnerable to a critical unpatched security flaw in the HTTP/HTTPS proxy tool. The issue, tracked as CVE-2023-49606, carries a CVSS score of 9.8 out of a maximum of 10, per…
New ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
[ad_1] May 06, 2024NewsroomSpyware / Malware Cybersecurity researchers have discovered a new information stealer targeting Apple macOS systems that’s designed to set up persistence on the infected hosts and act as a spyware. Dubbed Cuckoo by Kandji, the malware is a universal Mach-O binary that’s capable of running on both Intel- and Arm-based Macs. The…
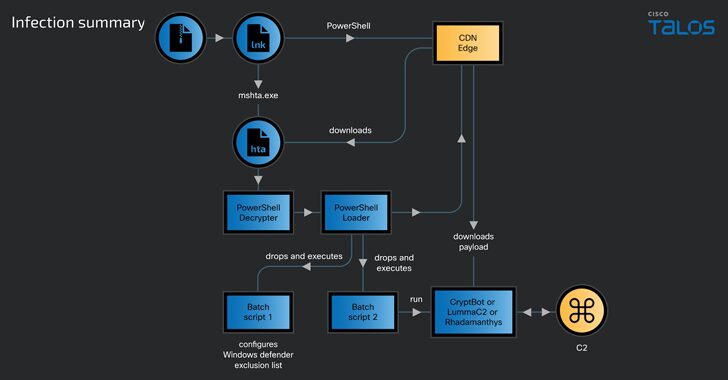
CoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
[ad_1] Apr 24, 2024NewsroomMalware / Data Security A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery Network (CDN) cache domains since at least February 2024. Cisco Talos has attributed the activity with moderate confidence to a threat actor tracked as CoralRaider, a…
eScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
[ad_1] A new malware campaign has been exploiting the updating mechanism of the eScan antivirus software to distribute backdoors and cryptocurrency miners like XMRig through a long-standing threat codenamed GuptiMiner targeting large corporate networks. Cybersecurity firm Avast said the activity is the work of a threat actor with possible connections to a North Korean hacking…