[ad_1] May 03, 2024The Hacker NewsSaaS Security / Browser Security SaaS applications are dominating the corporate landscape. Their increased use enables organizations to push the boundaries of technology and business. At the same time, these applications also pose a new security risk that security leaders need to address, since the existing security stack does not…
Category: Cyber News
Hackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
[ad_1] May 03, 2024NewsroomCloud Security / Threat Intelligence Threat actors have been increasingly weaponizing Microsoft Graph API for malicious purposes with the aim of evading detection. This is done to “facilitate communications with command-and-control (C&C) infrastructure hosted on Microsoft cloud services,” the Symantec Threat Hunter Team, part of Broadcom, said in a report shared with…
Expert-Led Webinar – Uncovering Latest DDoS Tactics and Learn How to Fight Back
[ad_1] May 03, 2024The Hacker NewsLive Webinar / Server Security In today’s rapidly evolving digital landscape, the threat of Distributed Denial of Service (DDoS) attacks looms more significant than ever. As these cyber threats grow in sophistication, understanding and countering them becomes crucial for any business seeking to protect its online presence. To address this…
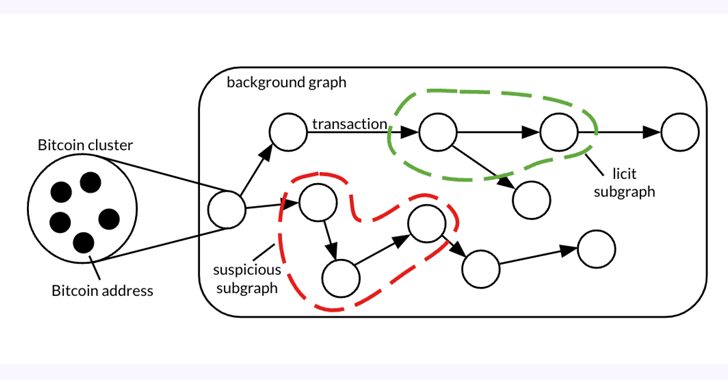
Bitcoin Forensic Analysis Uncovers Money Laundering Clusters and Criminal Proceeds
[ad_1] May 01, 2024NewsroomFinancial Crime / Forensic Analysis A forensic analysis of a graph dataset containing transactions on the Bitcoin blockchain has revealed clusters associated with illicit activity and money laundering, including detecting criminal proceeds sent to a crypto exchange and previously unknown wallets belonging to a Russian darknet market. The findings come from Elliptic…
How to Empower Your Employees for Cybersecurity Success
[ad_1] May 01, 2024The Hacker NewsSecurity Awareness Training There’s a natural human desire to avoid threatening scenarios. The irony, of course, is if you hope to attain any semblance of security, you’ve got to remain prepared to confront those very same threats. As a decision-maker for your organization, you know this well. But no matter…
New U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
[ad_1] Apr 30, 2024NewsroomIoT Security / Botnet The U.K. National Cyber Security Centre (NCSC) is calling on manufacturers of smart devices to comply with new legislation that prohibits them from using default passwords, effective April 29, 2024. “The law, known as the Product Security and Telecommunications Infrastructure act (or PSTI act), will help consumers to…
Millions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
[ad_1] Apr 30, 2024NewsroomDocker Hub / Supply Chain Attack Cybersecurity researchers have discovered multiple campaigns targeting Docker Hub by planting millions of malicious “imageless” containers over the past five years, once again underscoring how open-source registries could pave the way for supply chain attacks. “Over four million of the repositories in Docker Hub are imageless…
U.S. Government Releases New AI Security Guidelines for Critical Infrastructure
[ad_1] Apr 30, 2024NewsroomMachine Learning / National Security The U.S. government has unveiled new security guidelines aimed at bolstering critical infrastructure against artificial intelligence (AI)-related threats. “These guidelines are informed by the whole-of-government effort to assess AI risks across all sixteen critical infrastructure sectors, and address threats both to and from, and involving AI systems,”…
China-Linked ‘Muddling Meerkat’ Hijacks DNS to Map Internet on Global Scale
[ad_1] A previously undocumented cyber threat dubbed Muddling Meerkat has been observed undertaking sophisticated domain name system (DNS) activities in a likely effort to evade security measures and conduct reconnaissance of networks across the world since October 2019. Cloud security firm Infoblox described the threat actor as likely affiliated with the People’s Republic of China…
Google Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
[ad_1] Apr 29, 2024NewsroomMobile Security / Hacking Google on Monday revealed that almost 200,000 app submissions to its Play Store for Android were either rejected or remediated to address issues with access to sensitive data such as location or SMS messages over the past year. The tech giant also said it blocked 333,000 bad accounts…