[ad_1] Operational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise’s physical devices, processes, and events. Unlike traditional Information Technology (IT) systems, OT systems directly impact the physical world. This unique characteristic of OT brings additional cybersecurity considerations not typically present in conventional IT security architectures. The convergence…
Category: Cyber News
Researchers Identify Multiple China Hacker Groups Exploiting Ivanti Security Flaws
[ad_1] Multiple China-nexus threat actors have been linked to the zero-day exploitation of three security flaws impacting Ivanti appliances (CVE-2023-46805, CVE-2024-21887, and CVE-2024-21893). The clusters are being tracked by Mandiant under the uncategorized monikers UNC5221, UNC5266, UNC5291, UNC5325, UNC5330, and UNC5337. Also previously linked to the exploitation spree is a Chinese hacking crew called UNC3886,…
New Wave of JSOutProx Malware Targeting Financial Firms in APAC and MENA
[ad_1] Apr 05, 2024NewsroomCyber Espionage / Cybersecurity Financial organizations in the Asia-Pacific (APAC) and Middle East and North Africa (MENA) are being targeted by a new version of an “evolving threat” called JSOutProx. “JSOutProx is a sophisticated attack framework utilizing both JavaScript and .NET,” Resecurity said in a technical report published this week. “It employs…
Hackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites
[ad_1] Apr 06, 2024NewsroomSkimmer / Threat Intelligence Threat actors have been found exploiting a critical flaw in Magento to inject a persistent backdoor into e-commerce websites. The attack leverages CVE-2024-20720 (CVSS score: 9.1), which has been described by Adobe as a case of “improper neutralization of special elements” that could pave the way for arbitrary…
CISO Perspectives on Complying with Cybersecurity Regulations
[ad_1] Compliance requirements are meant to increase cybersecurity transparency and accountability. As cyber threats increase, so do the number of compliance frameworks and the specificity of the security controls, policies, and activities they include. For CISOs and their teams, that means compliance is a time-consuming, high-stakes process that demands strong organizational and communication skills on…
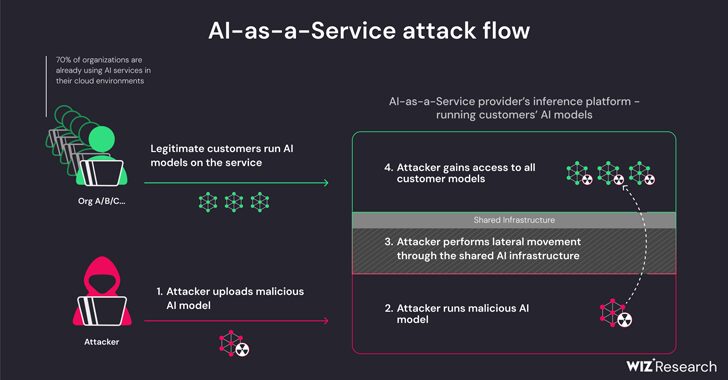
AI-as-a-Service Providers Vulnerable to PrivEsc and Cross-Tenant Attacks
[ad_1] Apr 05, 2024NewsroomArtificial Intelligence / Supply Chain Attack New research has found that artificial intelligence (AI)-as-a-service providers such as Hugging Face are susceptible to two critical risks that could allow threat actors to escalate privileges, gain cross-tenant access to other customers’ models, and even take over the continuous integration and continuous deployment (CI/CD) pipelines….
Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
[ad_1] Apr 05, 2024NewsroomMalware / Endpoint Security Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the attack is a PDF file written in Portuguese that, when opened, shows a blurred image and asks the victim to click on a link to download…
New Phishing Campaign Targets Oil & Gas with Evolved Data-Stealing Malware
[ad_1] Apr 04, 2024NewsroomPhishing Attack / Malware An updated version of an information-stealing malware called Rhadamanthys is being used in phishing campaigns targeting the oil and gas sector. “The phishing emails use a unique vehicle incident lure and, in later stages of the infection chain, spoof the Federal Bureau of Transportation in a PDF that…
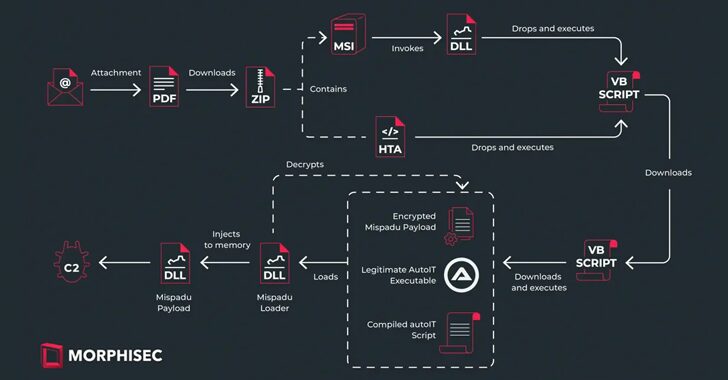
Vietnam-Based Hackers Steal Financial Data Across Asia with Malware
[ad_1] A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest valuable data since at least May 2023. Cisco Talos is tracking the cluster under the name CoralRaider, describing it as financially motivated. Targets of the campaign include India, China, South Korea, Bangladesh,…
Ivanti Rushes Patches for 4 New Flaws in Connect Secure and Policy Secure
[ad_1] Apr 04, 2024NewsroomNetwork Security / Vulnerability Ivanti has released security updates to address four security flaws impacting Connect Secure and Policy Secure Gateways that could result in code execution and denial-of-service (DoS). The list of flaws is as follows – CVE-2024-21894 (CVSS score: 8.2) – A heap overflow vulnerability in the IPSec component of…