[ad_1] Jan 22, 2024NewsroomCyber Attack / Hacking Media organizations and high-profile experts in North Korean affairs have been at the receiving end of a new campaign orchestrated by a threat actor known as ScarCruft in December 2023. “ScarCruft has been experimenting with new infection chains, including the use of a technical threat research report as…
Category: Cyber News
When Security Measures Go Wrong
[ad_1] Jan 18, 2024The Hacker NewsAuthentication Security / Passwords In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable to a wide range of cyberattacks. To safeguard critical business resources, organizations are increasingly turning to multi-factor authentication (MFA) as a more robust security measure. MFA requires users to provide multiple authentication factors…
TensorFlow CI/CD Flaw Exposed Supply Chain to Poisoning Attacks
[ad_1] Jan 18, 2024NewsroomSupply Chain Attacks / AI Security Continuous integration and continuous delivery (CI/CD) misconfigurations discovered in the open-source TensorFlow machine learning framework could have been exploited to orchestrate supply chain attacks. The misconfigurations could be abused by an attacker to “conduct a supply chain compromise of TensorFlow releases on GitHub and PyPi by…
Experts Warn of macOS Backdoor Hidden in Pirated Versions of Popular Software
[ad_1] Jan 19, 2024NewsroomMalware / Endpoint Security Pirated applications targeting Apple macOS users have been observed containing a backdoor capable of granting attackers remote control to infected machines. “These applications are being hosted on Chinese pirating websites in order to gain victims,” Jamf Threat Labs researchers Ferdous Saljooki and Jaron Bradley said. “Once detonated, the…
Backup and Recovery Strategies for Exchange Server Administrators
[ad_1] In the current digital landscape, data has emerged as a crucial asset for organizations, akin to currency. It’s the lifeblood of any organization in today’s interconnected and digital world. Thus, safeguarding the data is of paramount importance. Its importance is magnified in on-premises Exchange Server environments where vital business communication and emails are stored…
Russian COLDRIVER Hackers Expand Beyond Phishing with Custom Malware
[ad_1] The Russia-linked threat actor known as COLDRIVER has been observed evolving its tradecraft to go beyond credential harvesting to deliver its first-ever custom malware written in the Rust programming language. Google’s Threat Analysis Group (TAG), which shared details of the latest activity, said the attack chains leverage PDFs as decoy documents to trigger the…
Npm Trojan Bypasses UAC, Installs AnyDesk with “Oscompatible” Package
[ad_1] Jan 19, 2024NewsroomSoftware Security / Spyware A malicious package uploaded to the npm registry has been found deploying a sophisticated remote access trojan on compromised Windows machines. The package, named “oscompatible,” was published on January 9, 2024, attracting a total of 380 downloads before it was taken down. oscompatible included a “few strange binaries,”…
U.S. Cybersecurity Agency Warns of Actively Exploited Ivanti EPMM Vulnerability
[ad_1] Jan 19, 2024NewsroomCyber Theat / Zero-Day The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched critical flaw impacting Ivanti Endpoint Manager Mobile (EPMM) and MobileIron Core to its Known Exploited Vulnerabilities (KEV) catalog, stating it’s being actively exploited in the wild. The vulnerability in question is CVE-2023-35082 (CVSS score: 9.8),…
New Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic
[ad_1] Jan 18, 2024NewsroomServer Security / Cryptocurrency Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well as the 9Hits Viewer software as part of a multi-pronged monetization strategy. “This is the first documented case of malware deploying the 9Hits application as a…
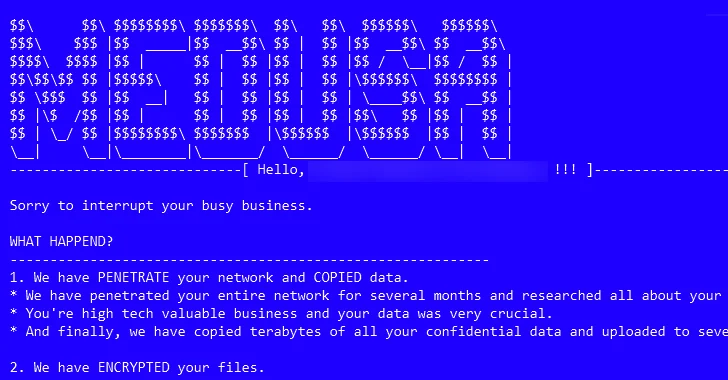
From Data Leaks to Multi-Extortion
[ad_1] The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak site on the dark web in February 2023 to publish sensitive data of victims who are unwilling to agree to their demands. “As part of their multi-extortion strategy, this group will provide victims…