[ad_1] Apr 04, 2025Ravie LakshmananVulnerability / Cloud Security A maximum severity security vulnerability has been disclosed in Apache Parquet’s Java Library that, if successfully exploited, could allow a remote attacker to execute arbitrary code on susceptible instances. Apache Parquet is a free and open-source columnar data file format that’s designed for efficient data processing and…
Category: Cyber News
Critical Ivanti Flaw Actively Exploited to Deploy TRAILBLAZE and BRUSHFIRE Malware
[ad_1] Apr 04, 2025Ravie LakshmananMalware / Vulnerability Ivanti has disclosed details of a now-patched critical security vulnerability impacting its Connect Secure that has come under active exploitation in the wild. The vulnerability, tracked as CVE-2025-22457 (CVSS score: 9.0), concerns a case of a stack-based buffer overflow that could be exploited to execute arbitrary code on…
CERT-UA Reports Cyberattacks Targeting Ukrainian State Systems with WRECKSTEEL Malware
[ad_1] Apr 04, 2025Ravie LakshmananCritical Infrastructure / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has revealed that no less than three cyber attacks were recorded against state administration bodies and critical infrastructure facilities in the country with an aim to steal sensitive data. The campaign, the agency said, involved the use of compromised…
Triada Malware Preloaded on Counterfeit Android Phones Infects 2,600+ Devices
[ad_1] Apr 03, 2025Ravie LakshmananThreat Intelligence / Mobile Security Counterfeit versions of popular smartphone models that are sold at reduced prices have been found to be preloaded with a modified version of an Android malware called Triada. “More than 2,600 users in different countries have encountered the new version of Triada, the majority in Russia,”…
Google Patches Quick Share Vulnerability Enabling Silent File Transfers Without Consent
[ad_1] Apr 03, 2025Ravie LakshmananData Privacy / Vulnerability Cybersecurity researchers have disclosed details of a new vulnerability impacting Google’s Quick Share data transfer utility for Windows that could be exploited to achieve a denial-of-service (DoS) or send arbitrary files to a target’s device without their approval. The flaw, tracked as CVE-2024-10668 (CVSS score: 5.9), is…
Breaking Through the Security and Compliance Gridlock
[ad_1] AI holds the promise to revolutionize all sectors of enterpriseーfrom fraud detection and content personalization to customer service and security operations. Yet, despite its potential, implementation often stalls behind a wall of security, legal, and compliance hurdles. Imagine this all-too-familiar scenario: A CISO wants to deploy an AI-driven SOC to handle the overwhelming volume…
AI Threats Are Evolving Fast — Learn Practical Defense Tactics in this Expert Webinar
[ad_1] Apr 03, 2025The Hacker News The rules have changed. Again. Artificial intelligence is bringing powerful new tools to businesses. But it’s also giving cybercriminals smarter ways to attack. They’re moving quicker, targeting more precisely, and slipping past old defenses without being noticed. And here’s the harsh truth: If your security strategy hasn’t evolved with…
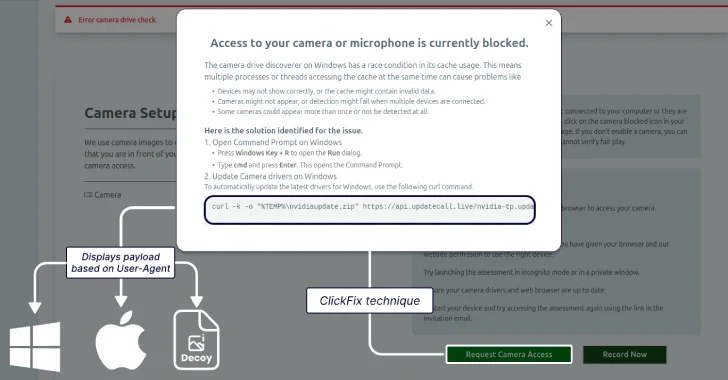
Lazarus Group Targets Job Seekers With ClickFix Tactic to Deploy GolangGhost Malware
[ad_1] The North Korean threat actors behind Contagious Interview have adopted the increasingly popular ClickFix social engineering tactic to lure job seekers in the cryptocurrency sector to deliver a previously undocumented Go-based backdoor called GolangGhost on Windows and macOS systems. The new activity, assessed to be a continuation of the campaign, has been codenamed ClickFake…
Microsoft Warns of Tax-Themed Email Attacks Using PDFs and QR Codes to Deliver Malware
[ad_1] Microsoft is warning of several phishing campaigns that are leveraging tax-related themes to deploy malware and steal credentials. “These campaigns notably use redirection methods such as URL shorteners and QR codes contained in malicious attachments and abuse legitimate services like file-hosting services and business profile pages to avoid detection,” Microsoft said in a report…
Outlaw Group Uses SSH Brute-Force to Deploy Cryptojacking Malware on Linux Servers
[ad_1] Apr 02, 2025Ravie LakshmananCryptojacking / Malware Cybersecurity researchers have shed light on an “auto-propagating” cryptocurrency mining botnet called Outlaw (aka Dota) that’s known for targeting SSH servers with weak credentials. “Outlaw is a Linux malware that relies on SSH brute-force attacks, cryptocurrency mining, and worm-like propagation to infect and maintain control over systems,” Elastic…