[ad_1] Mar 28, 2025Ravie LakshmananSpyware / Malware An Android malware family previously observed targeting Indian military personnel has been linked to a new campaign likely aimed at users in Taiwan under the guise of chat apps. “PJobRAT can steal SMS messages, phone contacts, device and app information, documents, and media files from infected Android devices,”…
Category: Cyber News
Nine-Year-Old npm Packages Hijacked to Exfiltrate API Keys via Obfuscated Scripts
[ad_1] Mar 28, 2025Ravie LakshmananCryptocurrency / Developer Security Cybersecurity researchers have discovered several cryptocurrency packages on the npm registry that have been hijacked to siphon sensitive information such as environment variables from compromised systems. “Some of these packages have lived on npmjs.com for over 9 years, and provide legitimate functionality to blockchain developers,” Sonatype researcher…
NetApp SnapCenter Flaw Could Let Users Gain Remote Admin Access on Plug-In Systems
[ad_1] Mar 27, 2025Ravie LakshmananVulnerability / Enterprise Security A critical security flaw has been disclosed in NetApp SnapCenter that, if successfully exploited, could allow privilege escalation. SnapCenter is an enterprise-focused software that’s used to manage data protection across applications, databases, virtual machines, and file systems, offering the ability to backup, restore, and clone data resources….
New Report Explains Why CASB Solutions Fail to Address Shadow SaaS and How to Fix It
[ad_1] Mar 27, 2025The Hacker NewsBrowser Security / Data Protection Whether it’s CRMs, project management tools, payment processors, or lead management tools – your workforce is using SaaS applications by the pound. Organizations often rely on traditional CASB solutions for protecting against malicious access and data exfiltration, but these fall short for protecting against shadow…
New Morphing Meerkat Phishing Kit Mimics 114 Brands Using Victims’ DNS Email Records
[ad_1] Mar 27, 2025Ravie LakshmananEmail Security / Malware Cybersecurity researchers have shed light on a new phishing-as-a-service (PhaaS) platform that leverages the Domain Name System (DNS) mail exchange (MX) records to serve fake login pages that impersonate about 114 brands. DNS intelligence firm Infoblox is tracking the actor behind the PhaaS, the phishing kit, and…
Hackers Repurpose RansomHub’s EDRKillShifter in Medusa, BianLian, and Play Attacks
[ad_1] Mar 27, 2025Ravie LakshmananEndpoint Security / Ransomware A new analysis has uncovered connections between affiliates of RansomHub and other ransomware groups like Medusa, BianLian, and Play. The connection stems from the use of a custom tool that’s designed to disable endpoint detection and response (EDR) software on compromised hosts, according to ESET. The EDR…
APT36 Spoofs India Post Website to Infect Windows and Android Users with Malware
[ad_1] Mar 27, 2025Ravie LakshmananMobile Security / Malware An advanced persistent threat (APT) group with ties to Pakistan has been attributed to the creation of a fake website masquerading as India’s public sector postal system as part of a campaign designed to infect both Windows and Android users in the country. Cybersecurity company CYFIRMA has…
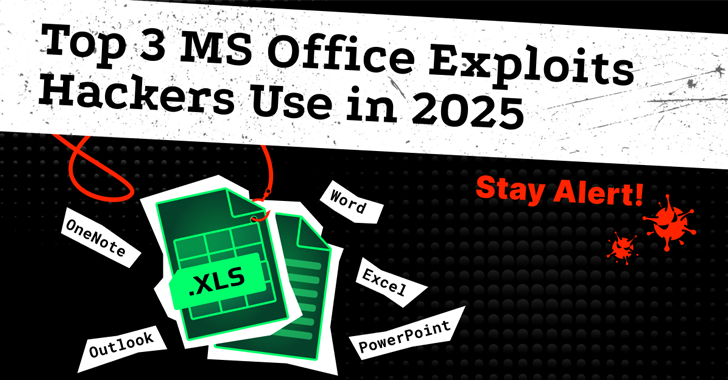
Top 3 MS Office Exploits Hackers Use in 2025 – Stay Alert!
[ad_1] Hackers have long used Word and Excel documents as delivery vehicles for malware, and in 2025, these tricks are far from outdated. From phishing schemes to zero-click exploits, malicious Office files are still one of the easiest ways into a victim’s system. Here are the top three Microsoft Office-based exploits still making the rounds…
150,000 Sites Compromised by JavaScript Injection Promoting Chinese Gambling Platforms
[ad_1] Mar 27, 2025Ravie LakshmananMalware / Website Security An ongoing campaign that infiltrates legitimate websites with malicious JavaScript injects to promote Chinese-language gambling platforms has ballooned to compromise approximately 150,000 sites to date. “The threat actor has slightly revamped their interface but is still relying on an iframe injection to display a full-screen overlay in…
CISA Warns of Sitecore RCE Flaws; Active Exploits Hit Next.js and DrayTek Devices
[ad_1] Mar 27, 2025Ravie LakshmananVulnerability / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two six-year-old security flaws impacting Sitecore CMS and Experience Platform (XP) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerabilities are listed below – CVE-2019-9874 (CVSS score: 9.8) – A deserialization…