[ad_1] Mar 25, 2025Ravie LakshmananThreat Intelligence / Malware A new investigation has unearthed nearly 200 unique command-and-control (C2) domains associated with a malware called Raspberry Robin. “Raspberry Robin (also known as Roshtyak or Storm-0856) is a complex and evolving threat actor that provides initial access broker (IAB) services to numerous criminal groups, many of which…
Category: Cyber News
Keeping Pace with an Expanding Attack Surface
[ad_1] Organizations now use an average of 112 SaaS applications—a number that keeps growing. In a 2024 study, 49% of 644 respondents who frequently used Microsoft 365 believed that they had less than 10 apps connected to the platform, despite the fact that aggregated data indicated over 1,000+ Microsoft 365 SaaS-to-SaaS connections on average per…
Hackers Use .NET MAUI to Target Indian and Chinese Users with Fake Banking, Social Apps
[ad_1] Mar 25, 2025Ravie LakshmananMobile Security / Data Theft Cybersecurity researchers are calling attention to an Android malware campaign that leverages Microsoft’s .NET Multi-platform App UI (.NET MAUI) framework to create bogus banking and social media apps targeting Indian and Chinese-speaking users. “These threats disguise themselves as legitimate apps, targeting users to steal sensitive information,”…
INTERPOL Arrests 306 Suspects, Seizes 1,842 Devices in Cross-Border Cybercrime Bust
[ad_1] Law enforcement authorities in seven African countries have arrested 306 suspects and confiscated 1,842 devices as part of an international operation codenamed Red Card that took place between November 2024 and February 2025. The coordinated effort “aims to disrupt and dismantle cross-border criminal networks which cause significant harm to individuals and businesses,” INTERPOL said,…
Critical Next.js Vulnerability Allows Attackers to Bypass Middleware Authorization Checks
[ad_1] Mar 24, 2025Ravie LakshmananVulnerability / Web Security A critical security flaw has been disclosed in the Next.js React framework that could be potentially exploited to bypass authorization checks under certain conditions. The vulnerability, tracked as CVE-2025-29927, carries a CVSS score of 9.1 out of 10.0. “Next.js uses an internal header x-middleware-subrequest to prevent recursive…
How to Balance Password Security Against User Experience
[ad_1] Mar 24, 2025Ravie LakshmananPassword Security / Compliance If given the choice, most users are likely to favor a seamless experience over complex security measures, as they don’t prioritize strong password security. However, balancing security and usability doesn’t have to be a zero-sum game. By implementing the right best practices and tools, you can strike…
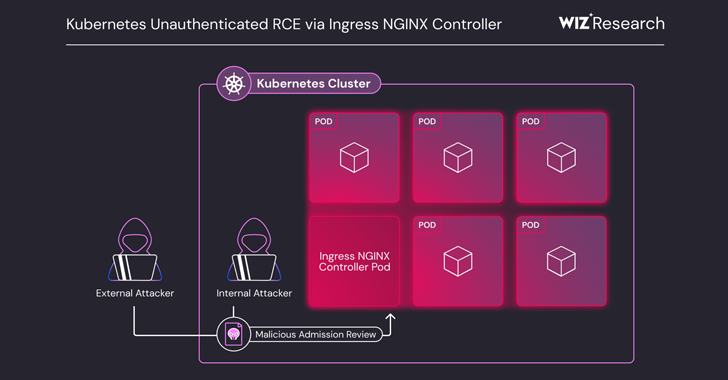
Critical Ingress NGINX Controller Vulnerability Allows RCE Without Authentication
[ad_1] Mar 24, 2025Ravie LakshmananVulnerability / Cloud Security A set of five critical security shortcomings have been disclosed in the Ingress NGINX Controller for Kubernetes that could result in unauthenticated remote code execution, putting over 6,500 clusters at immediate risk by exposing the component to the public internet. The vulnerabilities (CVE-2025-24513, CVE-2025-24514, CVE-2025-1097, CVE-2025-1098, and…
Microsoft Adds Inline Data Protection to Edge for Business to Block GenAI Data Leaks
[ad_1] Mar 24, 2025Ravie LakshmananEnterprise Security / Browser Security Microsoft on Monday announced a new feature called inline data protection for its enterprise-focused Edge for Business web browser. The native data security control is designed to prevent employees from sharing sensitive company-related data into consumer generative artificial intelligence (GenAI) apps like OpenAI ChatGPT, Google Gemini,…
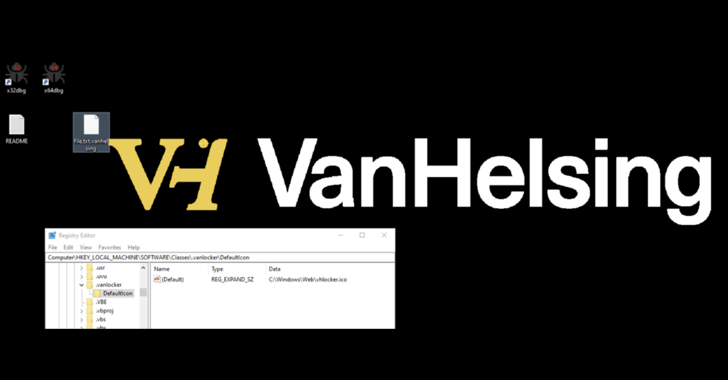
3 Victims, $5K Entry Fee, Multi-OS, and Double Extortion Tactics
[ad_1] Mar 24, 2025Ravie LakshmananMalware / Ransomware A ransomware-as-a-service (RaaS) operation called VanHelsing has already claimed three victims since it launched on March 7, 2025. “The RaaS model allows a wide range of participants, from experienced hackers to newcomers, to get involved with a $5,000 deposit. Affiliates keep 80% of the ransom payments, while the…
VSCode Marketplace Removes Two Extensions Deploying Early-Stage Ransomware
[ad_1] Mar 24, 2025Ravie LakshmananMalware / Encryption Cybersecurity researchers have uncovered two malicious extensions in the Visual Studio Code (VSCode) Marketplace that are designed to deploy ransomware that’s under development to its users. The extensions, named “ahban.shiba” and “ahban.cychelloworld,” have since been taken down by the marketplace maintainers. Both the extensions, per ReversingLabs, incorporate code…