[ad_1] Regulatory compliance is no longer just a concern for large enterprises. Small and mid-sized businesses (SMBs) are increasingly subject to strict data protection and security regulations, such as HIPAA, PCI-DSS, CMMC, GDPR, and the FTC Safeguards Rule. However, many SMBs struggle to maintain compliance due to limited IT resources, evolving regulatory requirements, and complex…
Category: Cyber News
YouTube Game Cheats Spread Arcane Stealer Malware to Russian-Speaking Users
[ad_1] Mar 20, 2025Ravie LakshmananMalware / Threat Analysis YouTube videos promoting game cheats are being used to deliver a previously undocumented stealer malware called Arcane likely targeting Russian-speaking users. “What’s intriguing about this malware is how much it collects,” Kaspersky said in an analysis. “It grabs account information from VPN and gaming clients, and all…
Veeam and IBM Release Patches for High-Risk Flaws in Backup and AIX Systems
[ad_1] Mar 20, 2025Ravie LakshmananVulnerability / Software Update Veeam has released security updates to address a critical security flaw impacting its Backup & Replication software that could lead to remote code execution. The vulnerability, tracked as CVE-2025-23120, carries a CVSS score of 9.9 out of 10.0. It affects 12.3.0.310 and all earlier version 12 builds….
How to Protect Your Business from Cyber Threats: Mastering the Shared Responsibility Model
[ad_1] Cybersecurity isn’t just another checkbox on your business agenda. It’s a fundamental pillar of survival. As organizations increasingly migrate their operations to the cloud, understanding how to protect your digital assets becomes crucial. The shared responsibility model, exemplified through Microsoft 365’s approach, offers a framework for comprehending and implementing effective cybersecurity [ad_2]
Six Governments Likely Use Israeli Paragon Spyware to Hack IM Apps and Harvest Data
[ad_1] Mar 20, 2025Ravie LakshmananSpyware / Mobile Security The governments of Australia, Canada, Cyprus, Denmark, Israel, and Singapore are likely customers of spyware developed by Israeli company Paragon Solutions, according to a new report from The Citizen Lab. Paragon, founded in 2019 by Ehud Barak and Ehud Schneorson, is the maker of a surveillance tool…
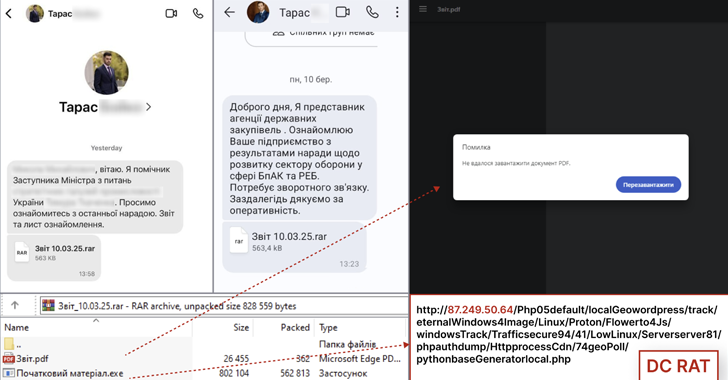
Dark Crystal RAT Targets Ukrainian Defense via Malicious Signal Messages
[ad_1] Mar 20, 2025Ravie LakshmananCybercrime / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) is warning of a new campaign that targets the defense sectors with Dark Crystal RAT (aka DCRat). The campaign, detected earlier this month, has been found to target both employees of enterprises of the defense-industrial complex and individual representatives of…
ClearFake Infects 9,300 Sites, Uses Fake reCAPTCHA and Turnstile to Spread Info-Stealers
[ad_1] Mar 19, 2025Ravie LakshmananCloud Security / Web Security The threat actors behind the ClearFake campaign are using fake reCAPTCHA or Cloudflare Turnstile verifications as lures to trick users into downloading malware such as Lumma Stealer and Vidar Stealer. ClearFake, first highlighted in July 2023, is the name given to a threat activity cluster that…
Hackers Exploit Severe PHP Flaw to Deploy Quasar RAT and XMRig Miners
[ad_1] Mar 19, 2025Ravie LakshmananThreat Intelligence / Cryptojacking Threat actors are exploiting a severe security flaw in PHP to deliver cryptocurrency miners and remote access trojans (RATs) like Quasar RAT. The vulnerability, assigned the CVE identifier CVE-2024-4577, refers to an argument injection vulnerability in PHP affecting Windows-based systems running in CGI mode that could allow…
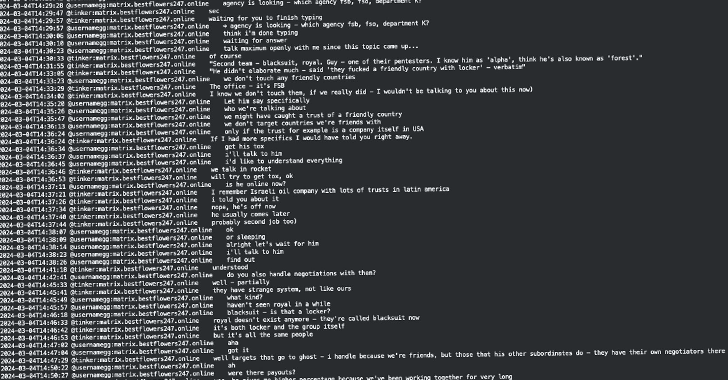
Leaked Black Basta Chats Suggest Russian Officials Aided Leader’s Escape from Armenia
[ad_1] Mar 19, 2025Ravie LakshmananCybercrime / Threat Intelligence The recently leaked trove of internal chat logs among members of the Black Basta ransomware operation has revealed possible connections between the e-crime gang and Russian authorities. The leak, containing over 200,000 messages from September 2023 to September 2024, was published by a Telegram user @ExploitWhispers last…
Watch This Webinar to Learn How to Eliminate Identity-Based Attacks—Before They Happen
[ad_1] Mar 19, 2025The Hacker NewsIdentity Security / Webinar In today’s digital world, security breaches are all too common. Despite the many security tools and training programs available, identity-based attacks—like phishing, adversary-in-the-middle, and MFA bypass—remain a major challenge. Instead of accepting these risks and pouring resources into fixing problems after they occur, why not prevent…