[ad_1] Mar 11, 2025Ravie LakshmananICS Security / Vulnerability Taiwanese company Moxa has released a security update to address a critical security flaw impacting its PT switches that could permit an attacker to bypass authentication guarantees. The vulnerability, tracked as CVE-2024-12297, has been assigned a CVSS v4 score of 9.2 out of a maximum of 10.0….
Category: Cyber News
SideWinder APT Targets Maritime, Nuclear, and IT Sectors Across Asia, Middle East, and Africa
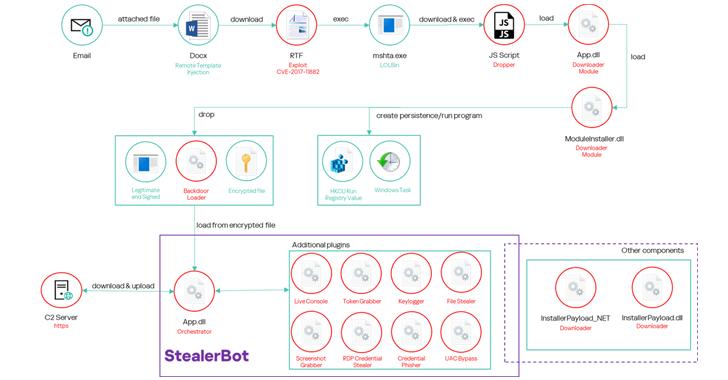
[ad_1] Mar 11, 2025Ravie LakshmananCyber Espionage / Maritime Security Maritime and logistics companies in South and Southeast Asia, the Middle East, and Africa have become the target of an advanced persistent threat (APT) group dubbed SideWinder. The attacks, observed by Kaspersky in 2024, spread across Bangladesh, Cambodia, Djibouti, Egypt, the United Arab Emirates, and Vietnam….
CISA Adds Five Actively Exploited Vulnerabilities in Advantive VeraCore and Ivanti EPM to KEV List
[ad_1] Mar 11, 2025Ravie LakshmananEnterprise Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added five security flaws impacting Advantive VeraCore and Ivanti Endpoint Manager (EPM) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation in the wild. The list of vulnerabilities is as follows – CVE-2024-57968…
Researchers Expose New Polymorphic Attack That Clones Browser Extensions to Steal Credentials
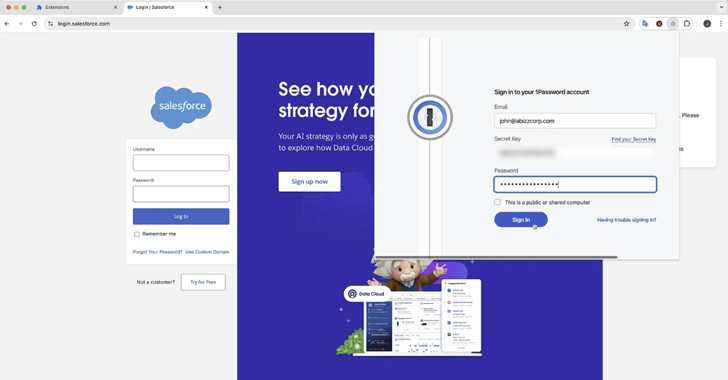
[ad_1] Mar 10, 2025Ravie LakshmananCybersecurity / Malware Cybersecurity researchers have demonstrated a novel technique that allows a malicious web browser extension to impersonate any installed add-on. “The polymorphic extensions create a pixel perfect replica of the target’s icon, HTML popup, workflows and even temporarily disables the legitimate extension, making it extremely convincing for victims to…
Desert Dexter Targets 900 Victims Using Facebook Ads and Telegram Malware Links
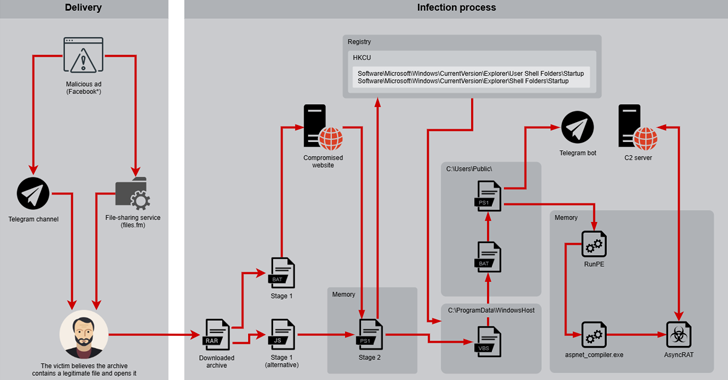
[ad_1] Mar 10, 2025Ravie LakshmananData Theft / Cryptocurrency The Middle East and North Africa have become the target of a new campaign that delivers a modified version of a known malware called AsyncRAT since September 2024. “The campaign, which leverages social media to distribute malware, is tied to the region’s current geopolitical climate,” Positive Technologies…
Why The Modern Google Workspace Needs Unified Security
[ad_1] The Need For Unified Security Google Workspace is where teams collaborate, share ideas, and get work done. But while it makes work easier, it also creates new security challenges. Cybercriminals are constantly evolving, finding ways to exploit misconfigurations, steal sensitive data, and hijack user accounts. Many organizations try to secure their environment by piecing…
New Attacks, Old Tricks, Bigger Impact
[ad_1] Mar 10, 2025Ravie LakshmananCybersecurity / Newsletter Cyber threats today don’t just evolve—they mutate rapidly, testing the resilience of everything from global financial systems to critical infrastructure. As cybersecurity confronts new battlegrounds—ranging from nation-state espionage and ransomware to manipulated AI chatbots—the landscape becomes increasingly complex, prompting vital questions: How secure are our cloud environments? Can…
SilentCryptoMiner Infects 2,000 Russian Users via Fake VPN and DPI Bypass Tools
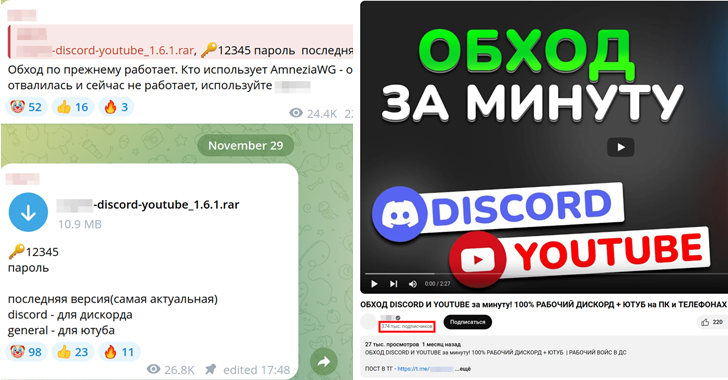
[ad_1] Mar 10, 2025Ravie LakshmananThreat Intelligence / Cybercrime A new mass malware campaign is infecting users with a cryptocurrency miner named SilentCryptoMiner by masquerading it as a tool designed to circumvent internet blocks and restrictions around online services. Russian cybersecurity company Kaspersky said the activity is part of a larger trend where cybercriminals are increasingly…
U.S. Secret Service Seizes Russian Garantex Crypto Exchange Website
[ad_1] Mar 07, 2025Ravie LakshmananCryptocurrency / Ransomware A coalition of international law enforcement agencies has seized the website associated with the cryptocurrency exchange Garantex (“garantex[.]org”), nearly three years after the service was sanctioned by the U.S. Treasury Department in April 2022. “The domain for Garantex has been seized by the United States Secret Service pursuant…
This Malicious PyPI Package Stole Ethereum Private Keys via Polygon RPC Transactions
[ad_1] Mar 07, 2025Ravie LakshmananMalware / Blockchain Cybersecurity researchers have discovered a malicious Python package on the Python Package Index (PyPI) repository that’s equipped to steal a victim’s Ethereum private keys by impersonating popular libraries. The package in question is set-utils, which has received 1,077 downloads to date. It’s no longer available for download from…