[ad_1] Mar 07, 2025The Hacker NewsPayment Security / Compliance Access on-demand webinar here Avoid a $100,000/month Compliance Disaster March 31, 2025: The Clock is Ticking. What if a single overlooked script could cost your business $100,000 per month in non-compliance fines? PCI DSS v4 is coming, and businesses handling payment card data must be prepared….
Category: Cyber News
Learn How ASPM Transforms Application Security from Reactive to Proactive
[ad_1] Mar 07, 2025The Hacker NewsSoftware Security / AppSec Are you tired of dealing with outdated security tools that never seem to give you the full picture? You’re not alone. Many organizations struggle with piecing together scattered information, leaving your apps vulnerable to modern threats. That’s why we’re excited to introduce a smarter, unified approach:…
FIN7, FIN8, and Others Use Ragnar Loader for Persistent Access and Ransomware Operations
[ad_1] Mar 07, 2025Ravie Lakshmanan Threat hunters have shed light on a “sophisticated and evolving malware toolkit” called Ragnar Loader that’s used by various cybercrime and ransomware groups like Ragnar Locker (aka Monstrous Mantis), FIN7, FIN8, and Ruthless Mantis (ex-REvil). “Ragnar Loader plays a key role in keeping access to compromised systems, helping attackers stay…
Microsoft Warns of Malvertising Campaign Infecting Over 1 Million Devices Worldwide
[ad_1] Mar 07, 2025Ravie LakshmananMalvertising / Open Source Microsoft has disclosed details of a large-scale malvertising campaign that’s estimated to have impacted over one million devices globally as part of what it said is an opportunistic attack designed to steal sensitive information. The tech giant, which detected the activity in early December 2024, is tracking…
PHP-CGI RCE Flaw Exploited in Attacks on Japan’s Tech, Telecom, and E-Commerce Sectors
[ad_1] Mar 07, 2025Ravie LakshmananThreat Intelligence /Vulnerability Threat actors of unknown provenance have been attributed to a malicious campaign predominantly targeting organizations in Japan since January 2025. “The attacker has exploited the vulnerability CVE-2024-4577, a remote code execution (RCE) flaw in the PHP-CGI implementation of PHP on Windows, to gain initial access to victim machines,”…
Safe{Wallet} Confirms North Korean TraderTraitor Hackers Stole $1.5 Billion in Bybit Heist
[ad_1] Mar 07, 2025Ravie LakshmananSecurity Breach / Cryptocurrency Safe{Wallet} has revealed that the cybersecurity incident that led to the Bybit $1.5 billion crypto heist is a “highly sophisticated, state-sponsored attack,” stating the North Korean threat actors behind the hack took steps to erase traces of the malicious activity in an effort to hamper investigation efforts….
Medusa Ransomware Hits 40+ Victims in 2025, Demands $100K–$15M Ransom
[ad_1] Mar 06, 2025Ravie LakshmananThreat Intelligence / Vulnerability The threat actors behind the Medusa ransomware have claimed nearly 400 victims since it first emerged in January 2023, with the financially motivated attacks witnessing a 42% increase between 2023 and 2024. In the first two months of 2025 alone, the group has claimed over 40 attacks,…
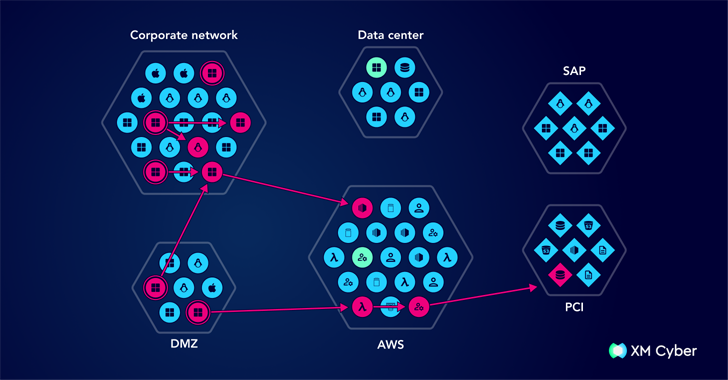
Outsmarting Cyber Threats with Attack Graphs
[ad_1] Cyber threats are growing more sophisticated, and traditional security approaches struggle to keep up. Organizations can no longer rely on periodic assessments or static vulnerability lists to stay secure. Instead, they need a dynamic approach that provides real-time insights into how attackers move through their environment. This is where attack graphs come in. By…
EncryptHub Deploys Ransomware and Stealer via Trojanized Apps, PPI Services, and Phishing
[ad_1] Mar 06, 2025Ravie LakshmananMalware / Ransomware The financially motivated threat actor known as EncryptHub has been observed orchestrating sophisticated phishing campaigns to deploy information stealers and ransomware, while also working on a new product called EncryptRAT. “EncryptHub has been observed targeting users of popular applications, by distributing trojanized versions,” Outpost24 KrakenLabs said in a…
Elastic Releases Urgent Fix for Critical Kibana Vulnerability Enabling Remote Code Execution
[ad_1] Mar 06, 2025Ravie LakshmananData Security / Software Security Elastic has rolled out security updates to address a critical security flaw impacting the Kibana data visualization dashboard software for Elasticsearch that could result in arbitrary code execution. The vulnerability, tracked as CVE-2025-25012, carries a CVSS score of 9.9 out of a maximum of 10.0. It…