[ad_1] Mar 06, 2025Ravie LakshmananData Breach / Website Security Over 1,000 websites powered by WordPress have been infected with a third-party JavaScript code that injects four separate backdoors. “Creating four backdoors facilitates the attackers having multiple points of re-entry should one be detected and removed,” c/side researcher Himanshu Anand said in a Wednesday analysis. The…
Category: Cyber News
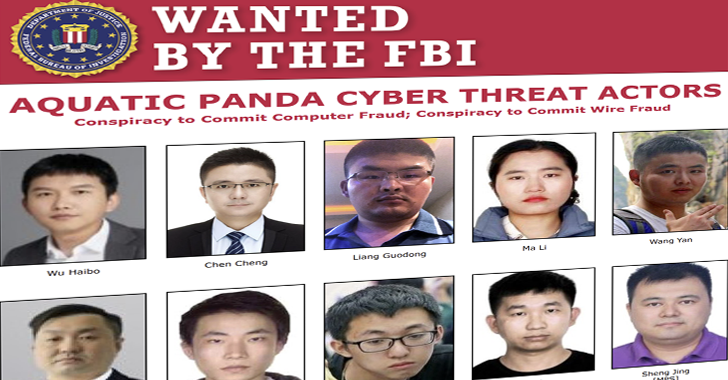
U.S. Charges 12 Chinese Nationals in State-Backed Hacking Operations
[ad_1] The U.S. Department of Justice (DoJ) has announced charges against 12 Chinese nationals for their alleged participation in a wide-ranging scheme designed to steal data and suppress free speech and dissent globally. The individuals include two officers of the People’s Republic of China’s (PRC) Ministry of Public Security (MPS), eight employees of an ostensibly…
Identity: The New Cybersecurity Battleground
[ad_1] The rapid adoption of cloud services, SaaS applications, and the shift to remote work have fundamentally reshaped how enterprises operate. These technological advances have created a world of opportunity but also brought about complexities that pose significant security threats. At the core of these vulnerabilities lies Identity—the gateway to enterprise security and the number…
Chinese APT Lotus Panda Targets Governments With New Sagerunex Backdoor Variants
[ad_1] Mar 05, 2025Ravie LakshmananCyber Espionage / Network Security The threat actor known as Lotus Panda has been observed targeting government, manufacturing, telecommunications, and media sectors in the Philippines, Vietnam, Hong Kong, and Taiwan with updated versions of a known backdoor called Sagerunex. “Lotus Blossom has been using the Sagerunex backdoor since at least 2016…
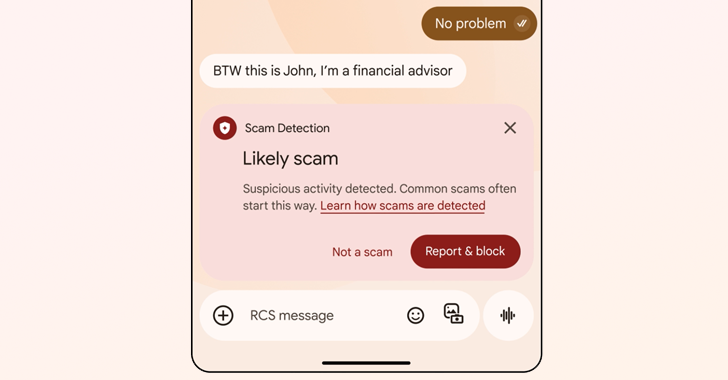
Google Rolls Out AI Scam Detection for Android to Combat Conversational Fraud
[ad_1] Mar 05, 2025Ravie LakshmananMobile Security / Artificial Intelligence Google has announced the rollout of artificial intelligence (AI)-powered scam detection features to secure Android device users and their personal information. “These features specifically target conversational scams, which can often appear initially harmless before evolving into harmful situations,” Google said. “And more phone calling scammers are…
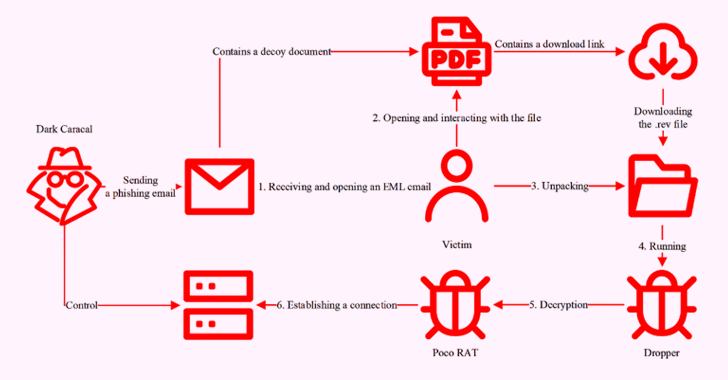
Dark Caracal Uses Poco RAT to Target Spanish-Speaking Enterprises in Latin America
[ad_1] Mar 05, 2025Ravie LakshmananCyber Espionage / Malware The threat actor known as Dark Caracal has been attributed to a campaign that deployed a remote access trojan called Poco RAT in attacks targeting Spanish-speaking targets in Latin America in 2024. The findings come from Russian cybersecurity company Positive Technologies, which described the malware as loaded…
Defending against USB drive attacks with Wazuh
[ad_1] USB drive attacks constitute a significant cybersecurity risk, taking advantage of the everyday use of USB devices to deliver malware and circumvent traditional network security measures. These attacks lead to data breaches, financial losses, and operational disruptions, with lasting impacts on an organization’s reputation. An example is the Stuxnet worm discovered in 2010, a…
China-Linked Silk Typhoon Expands Cyber Attacks to IT Supply Chains for Initial Access
[ad_1] Mar 05, 2025Ravie LakshmananNetwork Security / Data Breach The China-lined threat actor behind the zero-day exploitation of security flaws in Microsoft Exchange servers in January 2021 has shifted its tactics to target the information technology (IT) supply chain as a means to obtain initial access to corporate networks. That’s according to new findings from…
Seven Malicious Go Packages Found Deploying Malware on Linux and macOS Systems
[ad_1] Mar 05, 2025Ravie LakshmananOpen Source / Malware Cybersecurity researchers are alerting of an ongoing malicious campaign targeting the Go ecosystem with typosquatted modules that are designed to deploy loader malware on Linux and Apple macOS systems. “The threat actor has published at least seven packages impersonating widely used Go libraries, including one (github[.]com/shallowmulti/hypert) that…
Over 4,000 ISP IPs Targeted in Brute-Force Attacks to Deploy Info Stealers and Cryptominers
[ad_1] Mar 04, 2025Ravie LakshmananNetwork Security / Ransomware Internet service providers (ISPs) in China and the West Coast of the United States have become the target of a mass exploitation campaign that deploys information stealers and cryptocurrency miners on compromised hosts. The findings come from the Splunk Threat Research Team, which said the activity also…