[ad_1] Feb 25, 2025Ravie LakshmananNetwork Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two security flaws impacting Adobe ColdFusion and Oracle Agile Product Lifecycle Management (PLM) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerabilities in question are listed below – CVE-2017-3066 (CVSS score:…
Category: Cyber News
Australia Bans Kaspersky Software Over National Security and Espionage Concerns
[ad_1] Feb 24, 2025Ravie LakshmananSoftware Security / Data Protection Australia has become the latest country to ban the installation of security software from Russian company Kaspersky, citing national security concerns. “After considering threat and risk analysis, I have determined that the use of Kaspersky Lab, Inc. products and web services by Australian Government entities poses…
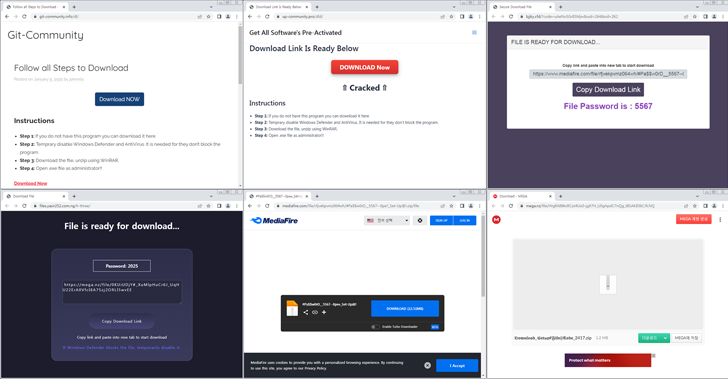
New Malware Campaign Uses Cracked Software to Spread Lumma and ACR Stealer
[ad_1] Feb 24, 2025Ravie LakshmananEndpoint Security / Vulnerability Cybersecurity researchers are warning of a new campaign that leverages cracked versions of software as a lure to distribute information stealers like Lumma and ACR Stealer. The AhnLab Security Intelligence Center (ASEC) said it has observed a spike in the distribution volume of ACR Stealer since January…
Why Continuous Validation Is Your Best Defense
[ad_1] Ransomware doesn’t hit all at once—it slowly floods your defenses in stages. Like a ship subsumed with water, the attack starts quietly, below the surface, with subtle warning signs that are easy to miss. By the time encryption starts, it’s too late to stop the flood. Each stage of a ransomware attack offers a…
Google Cloud KMS Adds Quantum-Safe Digital Signatures to Defend Against Future Threats
[ad_1] Feb 24, 2025Ravie LakshmananCloud Security / Encryption Google Cloud has announced quantum-safe digital signatures in Google Cloud Key Management Service (Cloud KMS) for software-based keys as a way to bulletproof encryption systems against the threat posed by cryptographically-relevant quantum computers. The feature, currently in preview, coexists with the National Institute of Standards and Technology’s…
From $1.5B Crypto Heist to AI Misuse & Apple’s Data Dilemma
[ad_1] Feb 24, 2025Ravie Lakshmanan Welcome to your weekly roundup of cyber news, where every headline gives you a peek into the world of online battles. This week, we look at a huge crypto theft, reveal some sneaky AI scam tricks, and discuss big changes in data protection. Let these stories spark your interest and…
Bybit Confirms Record-Breaking $1.46 Billion Crypto Heist in Sophisticated Cold Wallet Attack
[ad_1] Feb 22, 2025Ravie LakshmananFinancial Crime / Cryptocurrency Cryptocurrency exchange Bybit on Friday revealed that a “sophisticated” attack led to the theft of over $1.46 billion worth of cryptocurrency from one of its Ethereum cold (offline) wallets, making it the largest ever single crypto heist in history. “The incident occurred when our ETH multisig cold…
OpenAI Bans Accounts Misusing ChatGPT for Surveillance and Influence Campaigns
[ad_1] Feb 22, 2025Ravie LakshmananDisinformation / Artificial Intelligence OpenAI on Friday revealed that it banned a set of accounts that used its ChatGPT tool to develop a suspected artificial intelligence (AI)-powered surveillance tool. The social media listening tool is said to likely originate from China and is powered by one of Meta’s Llama models, with…
CISA Flags Craft CMS Vulnerability CVE-2025-23209 Amid Active Attacks
[ad_1] Feb 21, 2025Ravie LakshmananWeb Security / Vulnerability A high-severity security flaw impacting the Craft content management system (CMS) has been added by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerability in question is CVE-2025-23209 (CVSS score: 8.1), which impacts…
Data Leak Exposes TopSec’s Role in China’s Censorship-as-a-Service Operations
[ad_1] Feb 21, 2025Ravie LakshmananSurveillance / Content Monitoring An analysis of a data leak from a Chinese cybersecurity company TopSec has revealed that it likely offers censorship-as-a-service solutions to prospective customers, including a state-owned enterprise in the country. Founded in 1995, TopSec ostensibly offers services such as Endpoint Detection and Response (EDR) and vulnerability scanning….