[ad_1] Feb 20, 2025Ravie LakshmananSoftware Security / Vulnerability Microsoft has released security updates to address two Critical-rated flaws impacting Bing and Power Pages, including one that has come under active exploitation in the wild. The vulnerabilities are listed below – CVE-2025-21355 (CVSS score: 8.6) – Microsoft Bing Remote Code Execution Vulnerability CVE-2025-24989 (CVSS score: 8.2)…
Category: Cyber News
Citrix Releases Security Fix for NetScaler Console Privilege Escalation Vulnerability
[ad_1] Feb 20, 2025Ravie LakshmananVulnerability / IT Security Citrix has released security updates for a high-severity security flaw impacting NetScaler Console (formerly NetScaler ADM) and NetScaler Agent that could lead to privilege escalation under certain conditions. The vulnerability, tracked as CVE-2024-12284, has been given a CVSS v4 score of 8.8 out of a maximum of…
Hackers Exploit Signal’s Linked Devices Feature to Hijack Accounts via Malicious QR Codes
[ad_1] Feb 19, 2025Ravie LakshmananMobile Security / Cyber Espionage Multiple Russia-aligned threat actors have been observed targeting individuals of interest via the privacy-focused messaging app Signal to gain unauthorized access to their accounts. “The most novel and widely used technique underpinning Russian-aligned attempts to compromise Signal accounts is the abuse of the app’s legitimate ‘linked…
Trojanized Game Installers Deploy Cryptocurrency Miner in Large-Scale StaryDobry Attack
[ad_1] Feb 19, 2025The Hacker NewsWindows Security / Malware Users who are on the lookout for popular games were lured into downloading trojanized installers that led to the deployment of a cryptocurrency miner on compromised Windows hosts. The large-scale activity has been codenamed StaryDobry by Russian cybersecurity company Kaspersky, which first detected it on December…
The Ultimate MSP Guide to Structuring and Selling vCISO Services
[ad_1] The growing demand for cybersecurity and compliance services presents a great opportunity for Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs) to offer virtual Chief Information Security Officer (vCISO) services—delivering high-level cybersecurity leadership without the cost of a full-time hire. However, transitioning to vCISO services is not without its challenges. Many service…
New Snake Keylogger Variant Leverages AutoIt Scripting to Evade Detection
[ad_1] Feb 19, 2025The Hacker NewsMalware / Threat Intelligence A new variant of the Snake Keylogger malware is being used to actively target Windows users located in China, Turkey, Indonesia, Taiwan, and Spain. Fortinet FortiGuard Labs said the new version of the malware has been behind over 280 million blocked infection attempts worldwide since the…
CISA Adds Palo Alto Networks and SonicWall Flaws to Exploited Vulnerabilities List
[ad_1] Feb 19, 2025Ravie LakshmananThreat Intelligence / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added two security flaws impacting Palo Alto Networks PAN-OS and SonicWall SonicOS SSLVPN to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The flaws are listed below – CVE-2025-0108 (CVSS score: 7.8) –…
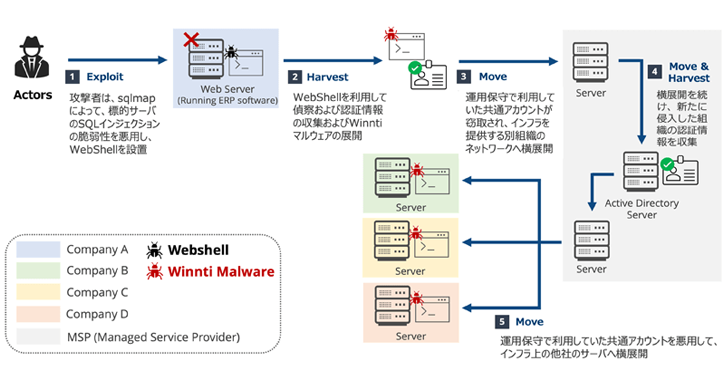
Winnti APT41 Targets Japanese Firms in RevivalStone Cyber Espionage Campaign
[ad_1] Feb 18, 2025Ravie LakshmananMalware / Network Security The China-linked threat actor known as Winnti has been attributed to a new campaign dubbed RevivalStone that targeted Japanese companies in the manufacturing, materials, and energy sectors in March 2024. The activity, detailed by Japanese cybersecurity company LAC, overlaps with a threat cluster tracked by Trend Micro…
Debunking the AI Hype: Inside Real Hacker Tactics
[ad_1] Feb 18, 2025The Hacker NewsArtificial Intelligence / Cyber Defense Is AI really reshaping the cyber threat landscape, or is the constant drumbeat of hype drowning out actual, more tangible, real-world dangers? According to Picus Labs’ Red Report 2025 which analyzed over one million malware samples, there’s been no significant surge, so far, in AI-driven…
New OpenSSH Flaws Enable Man-in-the-Middle and DoS Attacks — Patch Now
[ad_1] Feb 18, 2025Ravie LakshmananVulnerability / Network Security Two security vulnerabilities have been discovered in the OpenSSH secure networking utility suite that, if successfully exploited, could result in an active machine-in-the-middle (MitM) and a denial-of-service (DoS) attack, respectively, under certain conditions. The vulnerabilities, detailed by the Qualys Threat Research Unit (TRU), are listed below –…