[ad_1] Feb 13, 2025Ravie LakshmananWeb Security / Cloud Security A widespread phishing campaign has been observed leveraging bogus PDF documents hosted on the Webflow content delivery network (CDN) with an aim to steal credit card information and commit financial fraud. “The attacker targets victims searching for documents on search engines, resulting in access to malicious…
Category: Cyber News
Watch this Learn to Sync Dev and Sec Teams
[ad_1] Feb 13, 2025The Hacker NewsApplication Security / DevOps Ever felt like your team is stuck in a constant battle? Developers rush to add new features, while security folks worry about vulnerabilities. What if you could bring both sides together without sacrificing one for the other? We invite you to our upcoming webinar, “Opening the…
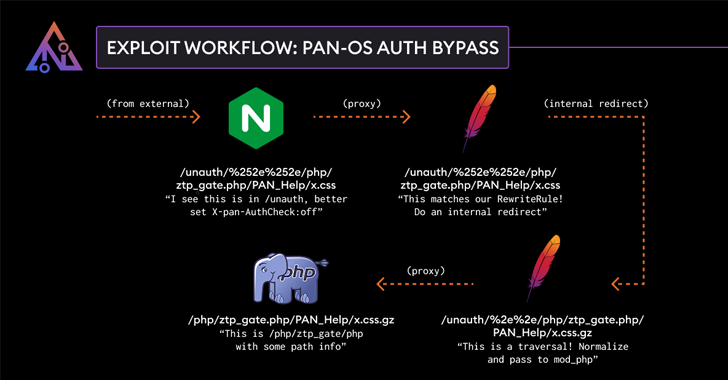
Palo Alto Networks Patches Authentication Bypass Exploit in PAN-OS Software
[ad_1] Feb 13, 2025Ravie LakshmananNetwork Security / Vulnerability Palo Alto Networks has addressed a high-severity security flaw in its PAN-OS software that could result in an authentication bypass. The vulnerability, tracked as CVE-2025-0108, carries a CVSS score of 7.8 out of 10.0. The score, however, drops to 5.1 if access to the management interface is…
FINALDRAFT Malware Exploits Microsoft Graph API for Espionage on Windows and Linux
[ad_1] Feb 13, 2025Ravie LakshmananMalware / Cyber Espionage Threat hunters have shed light on a new campaign targeting the foreign ministry of an unnamed South American nation with bespoke malware capable of granting remote access to infected hosts. The activity, detected in November 2024, has been attributed by Elastic Security Labs to a threat cluster…
Microsoft Uncovers Sandworm Subgroup’s Global Cyber Attacks Spanning 15+ Countries
[ad_1] A subgroup within the infamous Russian state-sponsored hacking group known as Sandworm has been attributed to a multi-year initial access operation dubbed BadPilot that stretched across the globe. “This subgroup has conducted globally diverse compromises of Internet-facing infrastructure to enable Seashell Blizzard to persist on high-value targets and support tailored network operations,” the Microsoft…
Microsoft’s Patch Tuesday Fixes 63 Flaws, Including Two Under Active Exploitation
[ad_1] Feb 12, 2025Ravie LakshmananPatch Tuesday / Vulnerability Microsoft on Tuesday released fixes for 63 security flaws impacting its software products, including two vulnerabilities that it said has come under active exploitation in the wild. Of the 63 vulnerabilities, three are rated Critical, 57 are rated Important, one is rated Moderate, and two are rated…
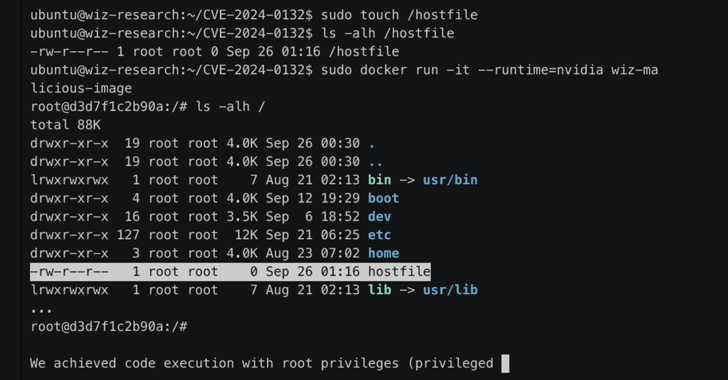
Researchers Find New Exploit Bypassing Patched NVIDIA Container Toolkit Vulnerability
[ad_1] Feb 12, 2025Ravie LakshmananContainer Security / Vulnerability Cybersecurity researchers have discovered a bypass for a now-patched security vulnerability in the NVIDIA Container Toolkit that could be exploited to break out of a container’s isolation protections and gain complete access to the underlying host. The new vulnerability is being tracked as CVE-2025-23359 (CVSS score: 8.3)….
How to Steer AI Adoption: A CISO Guide
[ad_1] Feb 12, 2025The Hacker NewsAI Security / Data Protection CISOs are finding themselves more involved in AI teams, often leading the cross-functional effort and AI strategy. But there aren’t many resources to guide them on what their role should look like or what they should bring to these meetings. We’ve pulled together a framework…
North Korean Hackers Exploit PowerShell Trick to Hijack Devices in New Cyberattack
[ad_1] Feb 12, 2025Ravie LakshmananIT Security / Cybercrime The North Korea-linked threat actor known as Kimsuky has been observed using a new tactic that involves deceiving targets into running PowerShell as an administrator and then instructing them to paste and run malicious code provided by them. “To execute this tactic, the threat actor masquerades as…
Ivanti Patches Critical Flaws in Connect Secure and Policy Secure – Update Now
[ad_1] Feb 12, 2025Ravie LakshmananNetwork Security / Vulnerability Ivanti has released security updates to address multiple security flaws impacting Connect Secure (ICS), Policy Secure (IPS), and Cloud Services Application (CSA) that could be exploited to achieve arbitrary code execution. The list of vulnerabilities is below – CVE-2024-38657 (CVSS score: 9.1) – External control of a…